View all questions & answers for the NSE 4 - FortiOS 7.6 Administrator Exam Materials exam
NSE 4 - FortiOS 7.6 Administrator Exam Materials-Question 14 Discussion
Comments
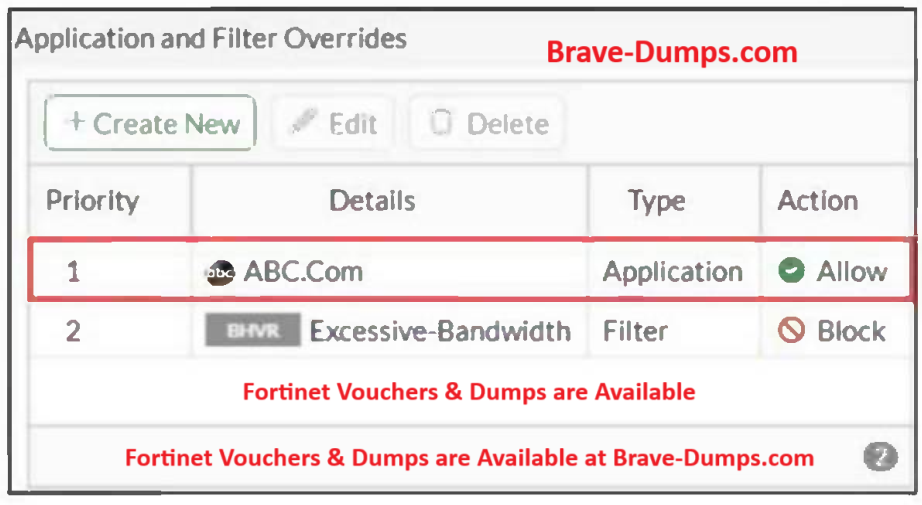
Selected Answers: C
- Security logs are typically generated when an action such as Block, Quarantine, or Monitor is triggered.
- An "Allow" action simply lets the traffic pass, so there’s no event to log under security logs.
Refer to the exhibit. An administrator has configured an Application Overrides for the ABC.Com application signature and set the Action to Allow. This application control profile is then applied to a firewall policy that is scanning all outbound traffic. Logging is enabled in the firewall policy. To test the configuration, the administrator accessed the ABC.Com web site several times. Why are there no logs generated under security logs for ABC.Com? (Choose one answer)
Brave-Dump Clients Votes