View all questions & answers for the FCSS - FortiSASE 25 Administrator Exam Materials exam
FCSS - FortiSASE 25 Administrator Exam Materials-Question 42 Discussion
Comments
Selected Answers: B, C
Configure ZTNA tags on FortiGate (Option C):
ZTNA (Zero Trust Network Access) tags are used to define access control policies based on the security posture of devices. By configuring ZTNA tags on FortiGate, administrators can enforce granular access controls, ensuring that only compliant devices can access protected resources.
Configure FortiGate as a zero trust network access (ZTNA) access proxy (Option B):
FortiGate can act as a ZTNA access proxy, which allows it to mediate and secure connections between remote endpoints and protected servers. This setup ensures that all TCP traffic passes through FortiGate, enabling inspection and enforcement of security policies.
Configure ZTNA servers and ZTNA policies on FortiGate (Option A):
To enable ZTNA functionality, administrators must define ZTNA servers (the protected resources) and create ZTNA policies on FortiGate. These policies determine how traffic is routed, inspected, and controlled based on device posture and user identity
Selected Answers: A, B
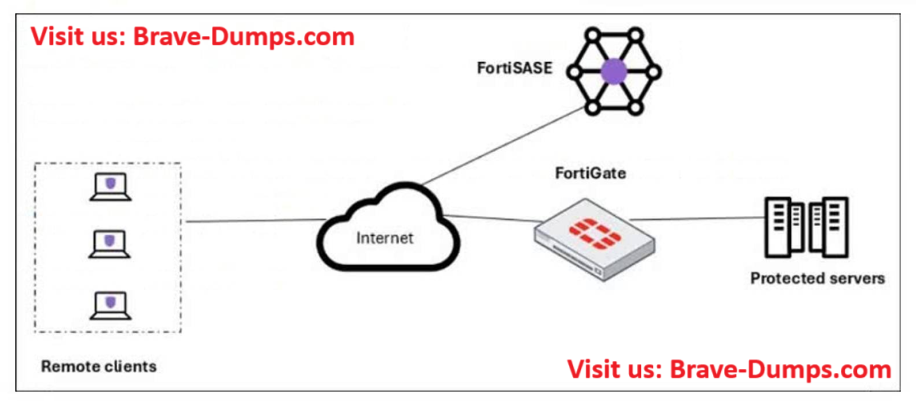
Refer to the exhibit. A customer needs to implement device posture checks for their remote endpoints while accessing the protected server. They also want the TCP traffic between the remote endpoints and the protected servers to be processed by FortiGate. In this scenario, which two setups will achieve these requirements? (Choose two answers)
Brave-Dump Clients Votes