● FCP - FortiManager 7.4 Administrator Exam Materials
Please note that the exam "FCP - FortiGate 7.4 Administrator Exam " is no longer offered by Fortinet and is not available for booking through Pearson VUE, so we opened it on free view,
It has been replaced by the exam "NSE 5 - FortiManager 7.6 Administrator Exam"
The new exam version is available on Brave-Dumps and can be purchased.
It has been replaced by the exam "NSE 5 - FortiManager 7.6 Administrator Exam"
The new exam version is available on Brave-Dumps and can be purchased.
Question #31

Question #32
An administrator runs the reload failure command diagnose test deploymanager reloadconf <deviceid> on FortiManager.
What does this command do?
(Choose one answer)
- A. It compares and provides differences in configuration on FortiManager with the current running configuration of the specified FortiGate.
- B. It downloads the latest configuration from the specified FortiGate and performs a reload operation on the device database.
- C. It reloads the policy package from the FortiManager to FortiGate.
- D. It installs the latest configuration on the specified FortiGate and updates the revision history database.
Question #33
What happens if you create an ADOM with version 7.2, add FortiGate devices running FortiOS 7.2, and then upgrade the FortiGate devices to FortiOS 7.4? (Choose one answer)
- A. The ADOM can concurrently manage FortiGate devices running different firmware versions.
- B. Adding higher version FortiGate devices to a lower version ADOM triggers an automatic ADOM upgrade.
- C. The ADOM restricts access to devices running lower firmware versions.
- D. Upgrading the FortiGate devices to FortiOS 7.4 may result in ADOM database corruption.
Question #34
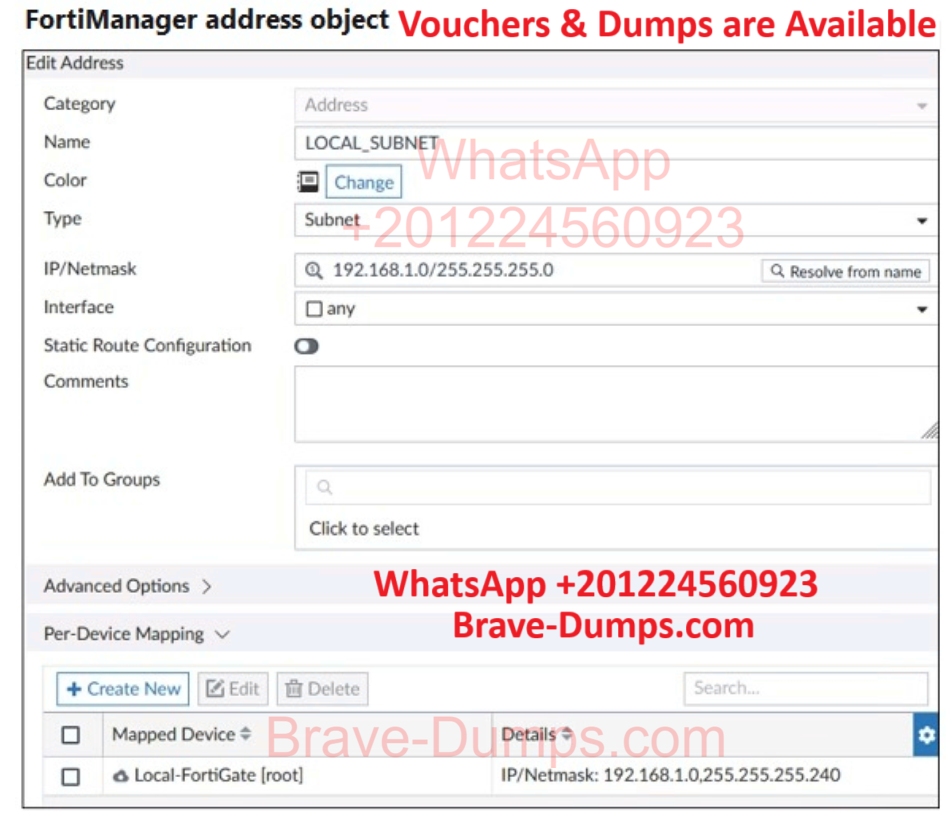
Refer to the exhibit.
An administrator has created a firewall address object that is used in multiple policy packages for multiple FortiGate devices in an ADOM.
After the installation operation is performed, which IP/netmask will be shown on FortiManager for this firewall address object?
(Choose one answer)
- A. FortiManager generates an error for each FortiGate without a per-device mapping defined for that object
- B. 192.168.1.0/24
- C. FortiManager replaces the address object to none.
- D. 192.168.1.0/28
Question #35
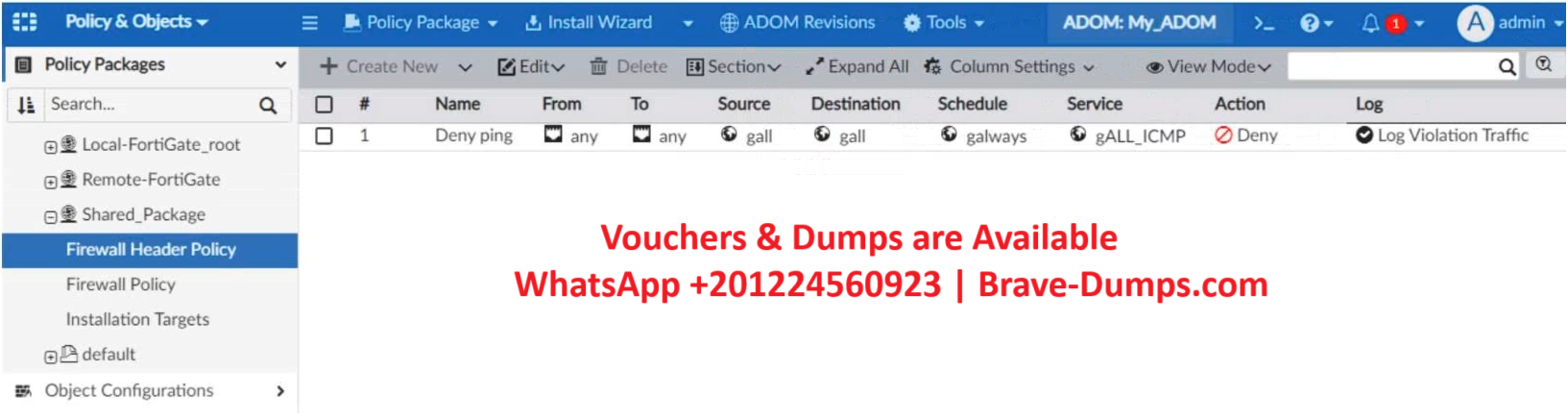
Refer to the exhibit.
A service provider administrator has assigned a global policy package to a managed customer ADOM named My_ADOM, which has four policy packages. The customer administrator has access only to My_ADOM.
How can customer or service provider administrators remove both global header and footer policies from the policy package named Shared_Package?
(Choose one answer)
- A. The customer administrator can unassign both polices by locking My_ADOM
- B. The customer administrator can unassign both global polices from My_ADOM
- C. The service provider administrator can unassign both global policies from My_ADOM
- D. The service provider administrator can unassign both policies from the global ADOM
Question #36
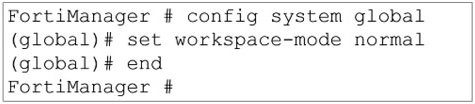
Refer to the exhibit.
Given the configuration shown in the exhibit, what are two results from this configuration?
(Choose two answers)
- A. Unlocking an ADOM will submit configuration changes automatically to the approval administrator.
- B. Ungraceful closed sessions will keep the ADOM in a locked state until the administrator session times out
- C. Unlocking an ADOM will install configuration changes automatically on managed devices.
- D. The same administrator can lock more than one ADOM at the same time.
Question #37
When an installation is performed from FortiManager, what is the recovery logic used between FortiManager and FortiGate for an FGFM tunnel? (Choose one answer)
- A. FortiGate will reject the CLI commands that will cause the tunnel to go down.
- B. FortiManager will revert and install a previous configuration revision on the managed FortiGate.
- C. FortiManager will not push the CLI commands as part of the installation that will cause the tunnel to go down.
- D. After 15 minutes, FortiGate will unset all CLI commands that were part of the installation that caused the tunnel to go down.
Question #38
What are two outcomes of ADOM revisions? (Choose two answers)
- A. ADOM revisions can create System Checkpoints for the FortiManager configuration.
- B. ADOM revisions can save the current state of the whole ADOM.
- C. ADOM revisions can significantly increase the size of the configuration backups.
- D. ADOM revisions can save the current state of all policy packages and objects for an ADOM
Question #39
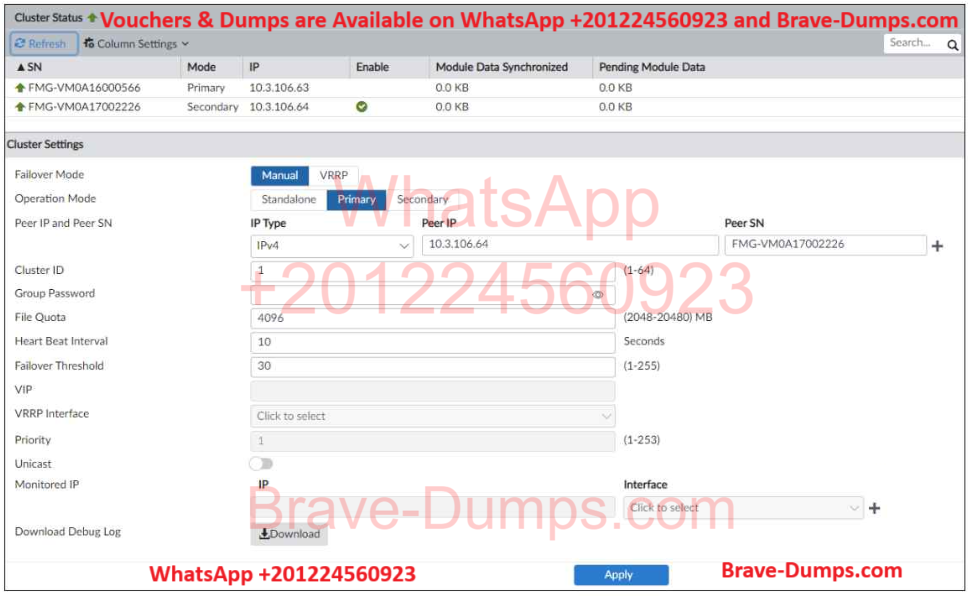
Refer to the exhibit.
Which statement about the environment shown in the exhibit is correct?
(Choose one answer)
- A. You must restart the secondary unit if you promote it to become the primary.
- B. A failover will take place after five minutes without receiving heartbeat packets.
- C. FortiAnalyzer features are not enabled on this FortiManager device.
- D. No FortiGuard packages have been synchronized between the cluster members yet.
Question #40
An administrator would like to review, approve, or reject all the firewall policy changes made by the junior administrators.
How should the workspace mode settings be configured on FortiManager?
(Choose one answer)
- A. Set to read/write and using the policy locking feature
- B. Set to normal and using the approval group feature
- C. Set to workflow and using the ADOM locking feature
- D. Set to workspace and using the policy locking feature
Refer to the exhibit.
An administrator created two new meta fields in FortiManager.
Which operation can be performed with these parameters? (Choose one answer)