● FCP - FortiAnalyzer 7.4 Administrator Exam Materials
Please note that the exam "FCP - FortiAnalyzer 7.4 Administrator" is no longer offered by Fortinet and is not available for booking through Pearson VUE, so we opened it on free view,
It has been replaced by the exam "NSE 5 - FortiAnalyzer 7.6 Analyst Exam"
The new exam version is available on Brave-Dumps and can be purchased.
It has been replaced by the exam "NSE 5 - FortiAnalyzer 7.6 Analyst Exam"
The new exam version is available on Brave-Dumps and can be purchased.
Question #31
Question #32
What is the purpose of trigger variables? (Choose one answer)
- A. To display statistics about the playbook runtime
- B. To use information from the trigger to filter the action in a task
- C. To provide the trigger information to make the playbook start running
- D. To store the start times of playbooks with On_Schedule triggers
Question #33
What are two effects of enabling auto-cache in a FortiAnalyzer report? (Choose two answers)
- A. The size of newly generated reports is optimized to conserve disk space.
- B. FortiAnalyzer local cache is used to store generated reports.
- C. When new logs are received, the hard-cache data is updated automatically.
- D. The generation time for reports is decreased.
Question #34
Why must you wait for several minutes before you run a playbook that you just created? (Choose one answer)
- A. FortiAnalyzer needs that time to parse the new playbook.
- B. FortiAnalyzer needs that time to back up the current playbooks.
- C. FortiAnalyzer needs that time to ensure there are no other playbooks running.
- D. FortiAnalyzer needs that time to debug the new playbook.
Question #35
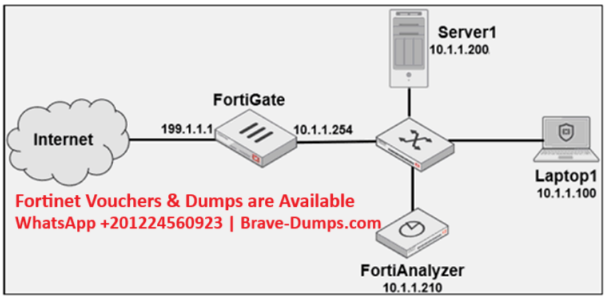
Refer to the exhibit.
Laptop1 is used by several administrators to manage FortiAnalyzer. You want to configure a generic text filter that matches all login attempts to the web interface generated by any user other than “admin" and coming from Laptop1.
Which filter will achieve the desired result?
(Choose one answer)
- A. operation-login & performed_on=="GUI(10.1.1.100)" & user!=admin
- B. operation-login & srcip==10.1.1.100 & dstip==10.1.1.210 & user==admin
- C. operation-login & dstip==10.1.1.210 & userl-admin
- D. operation-login & performed_on=="GUI(10.1.1.210)' & user!=admin
Question #36
Which two actions should an administrator take to view Compromised Hosts on FortiAnalyzer? (Choose two answers)
- A. Enable web filtering in firewall policies on FortiGate devices, and make sure these logs are sent to FortiAnalyzer.
- B. Subscribe FortiAnalyzer to FortiGuard to keep its local threat database up to date.
- C. Make sure all endpoints are reachable by FortiAnalyzer.
- D. Enable device detection on the FortiGate devices that are sending logs to FortiAnalyzer.
Question #37
How can you attach a report to an incident? (Choose one answer)
- A. By attaching it to an event handler alert
- B. By editing the settings of the desired report
- C. From the properties of an existing incident
- D. Saving it in JSON format, and then importing it
Question #38
What happens when the IOC breach detection engine on FortiAnalyzer finds web logs that match a blocklisted IP address? (Choose one answer)
- A. The endpoint is marked as Compromised and, optionally, can be put in quarantine.
- B. FortiAnalyzer flags the associated host for further analysis.
- C. A new Infected entry is added for the corresponding endpoint.
- D. The detection engine classifies those logs as Suspicious.
Question #39
Which two of the following must you configure on FortiAnalyzer to email a FortiAnalyzer report externally? (Choose two answers)
- A. Mail server
- B. Output profile
- C. SFTP server
- D. Report scheduling
Question #40
For which two purposes would you use the command set log-checksum? (Choose two answers)
- A. To encrypt log communications and data
- B. To prevent log modification or tampering
- C. To protect log data from man-in-the-middle attacks
- D. To send an identical set of logs to a second logging server
Which log will generate an event with the status Contained? (Choose one answer)