● Fortinet NSE 6 - FortiEDR 5.0 Exam Materials
Please note that the exam "Fortinet NSE 6 - FortiEDR 5.0 Exam" is no longer offered by Fortinet and is not available for booking through Pearson VUE.
It has been replaced by the exam "Fortinet NSE 6 - FortiEDR 7.0 Exam."
The new exam version is available on Brave-Dumps and can be purchased.
❌ Please do not order: Fortinet NSE 6 - FortiEDR 5.0 Exam
✅ Please order: Fortinet NSE 6 - FortiEDR 7.0 Exam
It has been replaced by the exam "Fortinet NSE 6 - FortiEDR 7.0 Exam."
The new exam version is available on Brave-Dumps and can be purchased.
❌ Please do not order: Fortinet NSE 6 - FortiEDR 5.0 Exam
✅ Please order: Fortinet NSE 6 - FortiEDR 7.0 Exam
Question #1
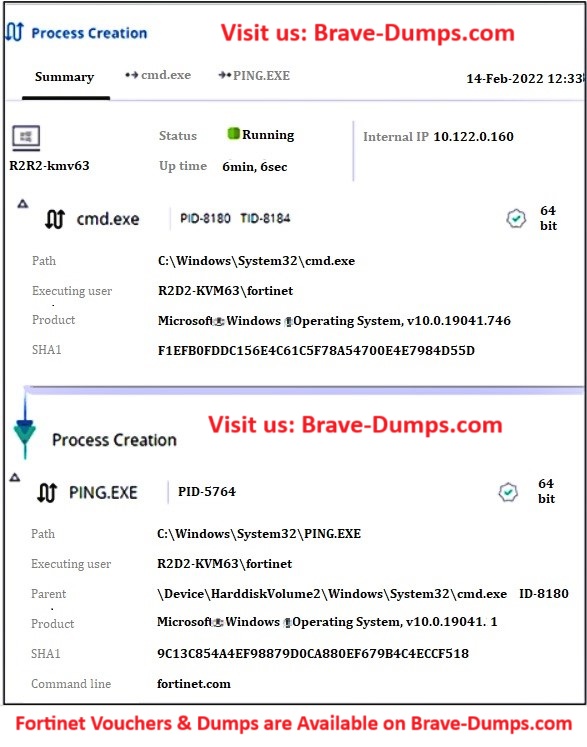
Question #2
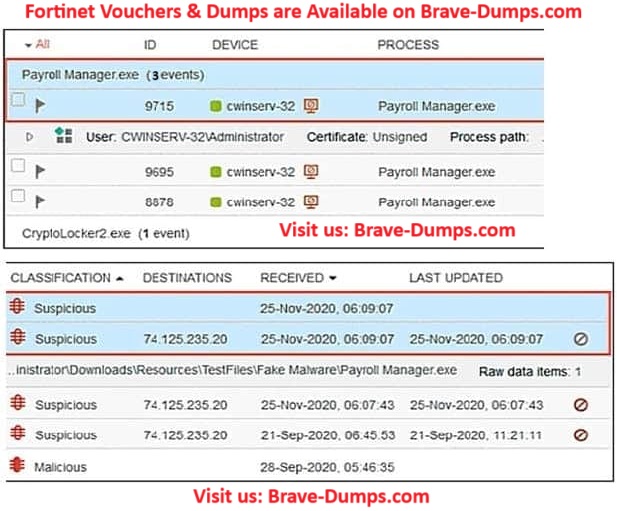
Refer to the exhibit.
The exhibit shows an event viewer.
What is true about the Payroll Manager exe event?
(Choose one answer)
- A. An event has not been handled by a console admin
- B. An event has been deleted
- C. A rule assigned action is set to block but the policy is in simulation mode
- D. An event has been handled by the communication control policy
Question #3
Which security policy has all of its rules disabled by default? (Choose one answer)
- A. Exfiltration Prevention
- B. Execution Prevention
- C. Device Control
- D. Ransomware Prevention
Question #4
Which FortiEDR component is required to find malicious files on the entire network of an organization? (Choose one answer)
- A. FortiEDR Central Manager
- B. FortiEDR Core
- C. FortiEDR Aggregator
- D. FortiEDR Threat Hunting Repository
Question #5
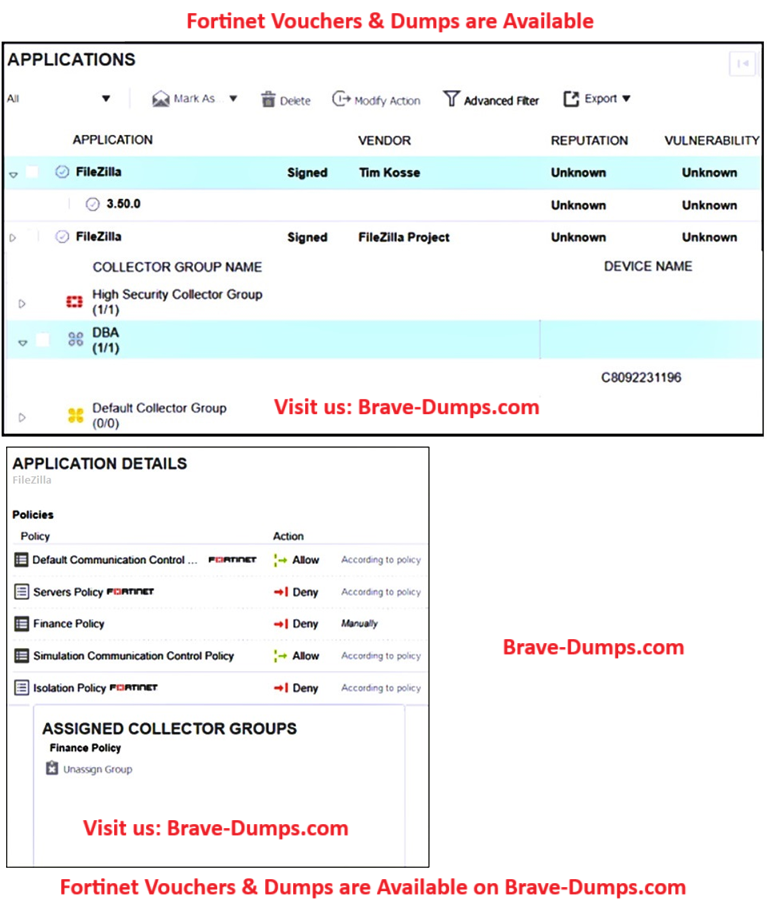
Refer to the exhibits.
The exhibits show application policy logs and application details. Collector C8092231196 is a member of the Finance group.
What must an administrator do to block the FileZilla application?
(Choose one answer)
- A. Deny application in Finance policy
- B. Assign Finance policy to DBA group
- C. Assign Finance policy to Default Collector Group
- D. Assign Simulation Communication Control Policy to DBA group
Question #6
Which two statements are true about the remediation function in the threat hunting module? (Choose two answers)
- A. The threat hunting module deletes files from collectors that are currently online.
- B. The file is quarantined.
- C. The threat hunting module sends the user a notification to delete the file.
- D. he file is removed from the affected collectors.
Question #7
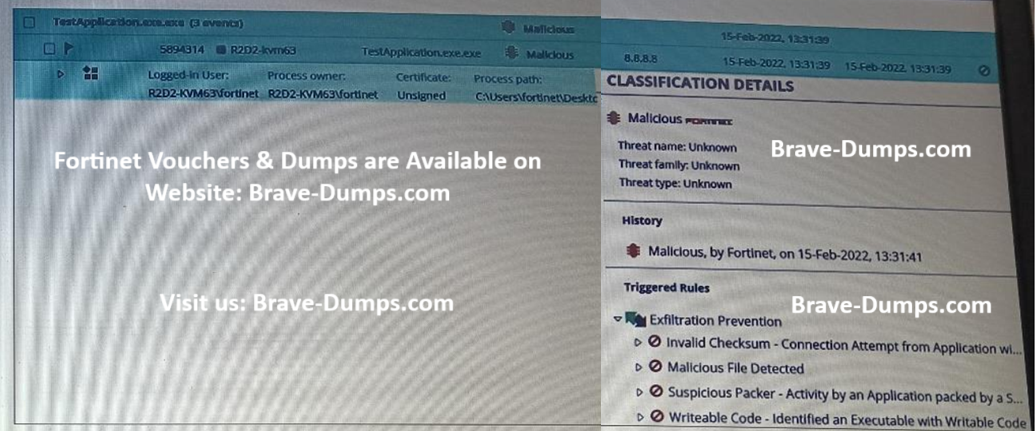
Refer to the exhibit
Based on the event shown in the exhibit, which two statements about the event are true?
(Choose two answers)
- A. The NGAV policy has blocked TestApplication.exe
- B. The user was able to launch TestApplication.exe
- C. TestApplication.exe is sophisticated malware
- D. FCS classified the event as malicious.
Question #8
When installing a FortiEDR collector, why is a ‘Registration Password’ for collectors needed? (Choose one answer)
- A. To restrict installation and uninstallation of collectors
- B. To verify Fortinet support request
- C. To restrict access to the management console
- D. To verify new group assignment
Question #9
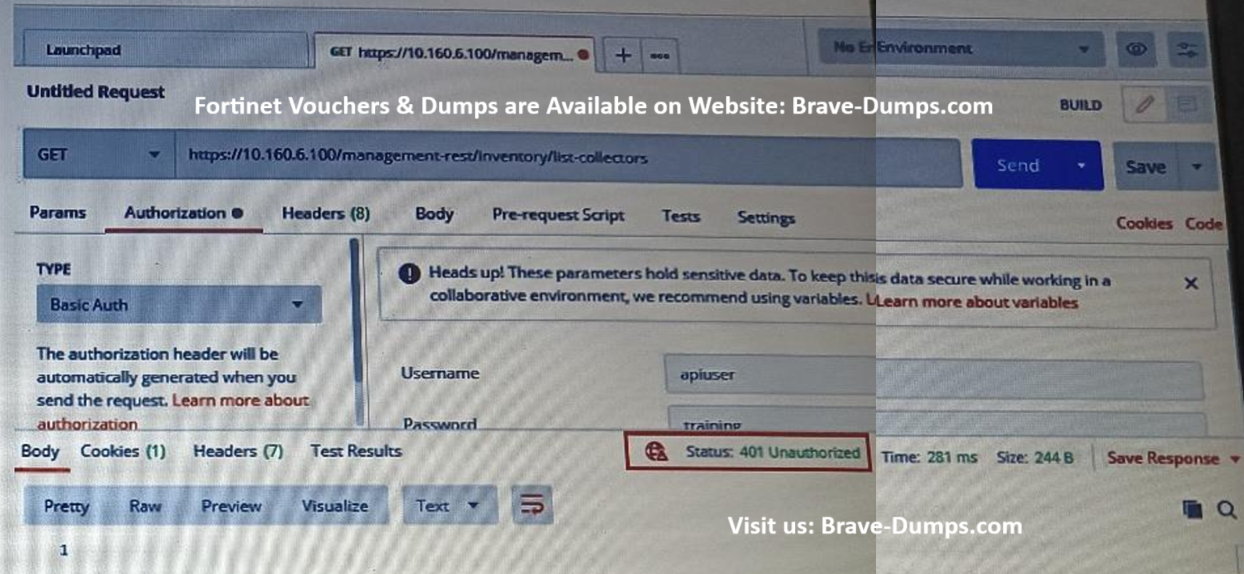
Refer to the exhibit.
Based on the postman output shown in the exhibit, why is the user getting an unauthorized error?
(Choose one answer)
- A. Postman cannot reach the central manager.
- B. API access is disabled on the central manager.
- C. The user has been assigned Admin and Rest API roles.
- D. FortiEDR requires a password reset the first time a user logs in.
Question #10
Which FortiEDR protection uses NGAV functionality? (Choose one answer)
- A. Incident Response
- B. Pre-infection
- C. Risk Mitigation
- D. Post-infection
Refer to the exhibit.
Based on the threat hunting event details shown in the exhibit, which two statements about the event are true? (Choose two answers)