● NSE 7 - Public Cloud Security 7.6.4 Architect Exam Materials
● Over 30 Students Passed NSE 7 - Public Cloud Security 7.6.4 (NSE7_CDS_AR-7.6) Using This Dump – Join Them Today!
● Less Than 100 Verified Questions for the NSE 7 - Public Cloud Security 7.6.4 Architect Dump (NSE7_CDS_AR-7.6 Dump)
● 100% score in the Real NSE 7 - Public Cloud Security 7.6.4 Architect Exam (NSE7_CDS_AR-7.6 Exam) at the Pearson VUE Testing Center
● Less Than 100 Verified Questions for the NSE 7 - Public Cloud Security 7.6.4 Architect Dump (NSE7_CDS_AR-7.6 Dump)
● 100% score in the Real NSE 7 - Public Cloud Security 7.6.4 Architect Exam (NSE7_CDS_AR-7.6 Exam) at the Pearson VUE Testing Center
Question #1
Question #2
How does an administrator secure container environments in Amazon AWS from newly emerged security threats? (Choose one answer)
- A. Using Docker-related application control signatures.
- B. Using Amazon AWS-related application control signatures.
- C. Using distributed network-related application control signatures.
- D. Using Amazon AWS_S3-related application control signatures.
Question #3
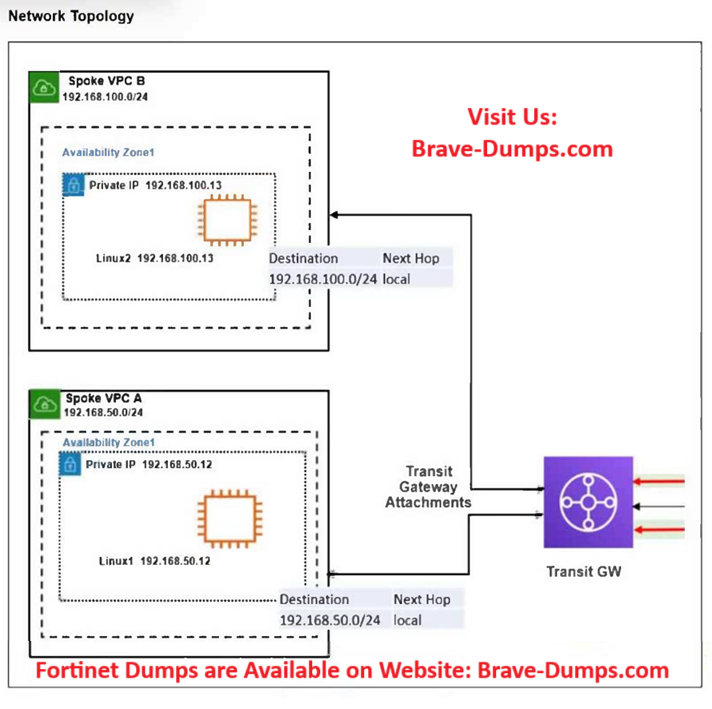
Refer to the exhibit.
The exhibit shows a customer deployment of two Linux instances and their main routing table in Amazon Web Services (AWS). The customer also created a Transit Gateway (TGW) and two attachments.
Which two steps are required to route traffic from Linux instances to the TGW?
(Choose two answers)
- A. In the main subnet routing table in VPC A and B, add a new route with destination 0.0.0.0/0, next hop TGW.
- B. In the TGW route table, associate two attachments.
- C. In the TGW route table, add route propagation to 192.168.0.0/16.
- D. In the main subnet routing table in VPC A and B, add a new route with destination 0.0.0.0/0, next hop Internet gateway (IGW).
Question #4
You have deployed a FortiGate HA cluster in Azure using a gateway load balancer for traffic inspection. However, traffic is not being routed correctly through the firewalls. What can be the cause of the issue? (Choose one answer)
- A. The gateway load balancer is not associated with the correct network security group (NSG) rules, which allow traffic to pass through.
- B. The health probes for the gateway load balancer are failing, which causes traffic to bypass the HA cluster.
- C. The protected VMs are in a different Azure subscription, which prevents the gateway load balancer from forwarding traffic.
- D. The Fortinet VMs have IP forwarding disabled, which is required for traffic inspection.
Question #5
Your organization has several FortiGate VMs deployed in Azure. You need to implement a solution with Azure native tools that allows you to determine whether packets are being permitted or blocked by the FortiGate VMs.
Which solution can you use to meet these requirements?
(Choose one answer)
- A. Install the Azure Monitor agent in all VMs.
- B. Use IP flow verify for each of the VMs.
- C. Configure Azure Advisor to analyze the network traffic.
- D. Insert the VM traffic logs in Azure Sentinel.
Question #6
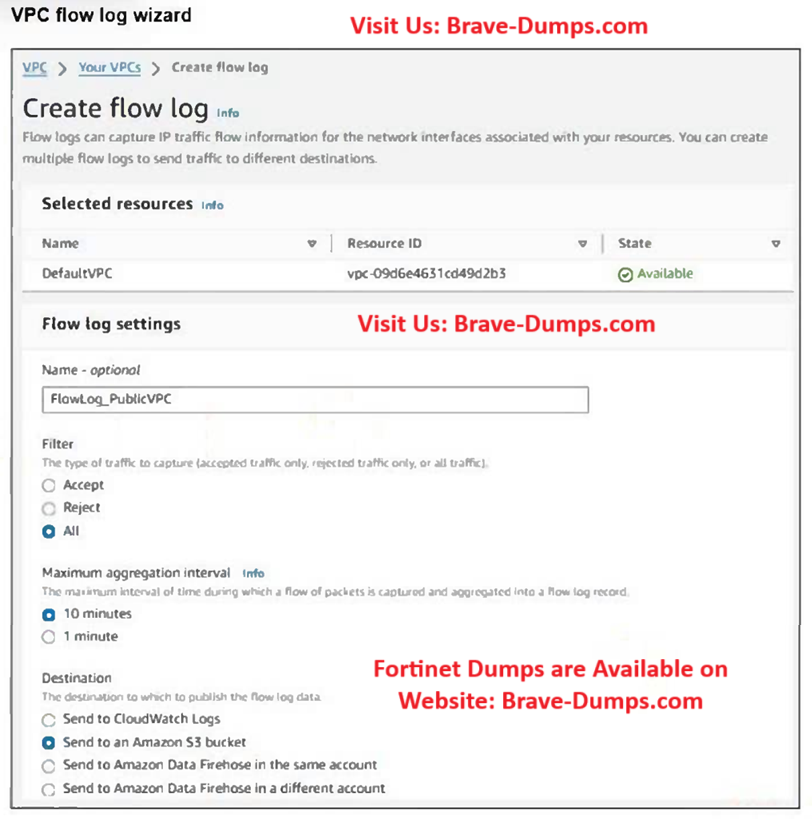
Refer to the exhibit.
Your team notices an unusually high volume of traffic sourced at one of the organizations FortiGate EC2 instances. They create a flow log to obtain and analyze detailed information about this traffic. However, when they checked the log, they found that it included traffic that was not associated with the FortiGate instance in question.
What can they do to obtain the correct logs?
(Choose one answer)
- A. Create a new flow log at the interface level.
- B. Change the maximum aggregation time to 1 minute.
- C. Ensure that the flow log data is not mixed with the rest of the traffic.
- D. Send the logs to Amazon Data Firehose instead to get more granular information.
Question #7
Your administrator instructed you to deploy an Azure vWAN solution to create a connection between the main company site and branch sites to the other company VNETs.
What is the best connection solution available between your company headquarters, branch sites, and the Azure vWAN hub?
(Choose one answer)
- A. An L2TP connection
- B. SSL VPN connections
- C. GRE tunnels
- D. ExpressRoute
Question #8
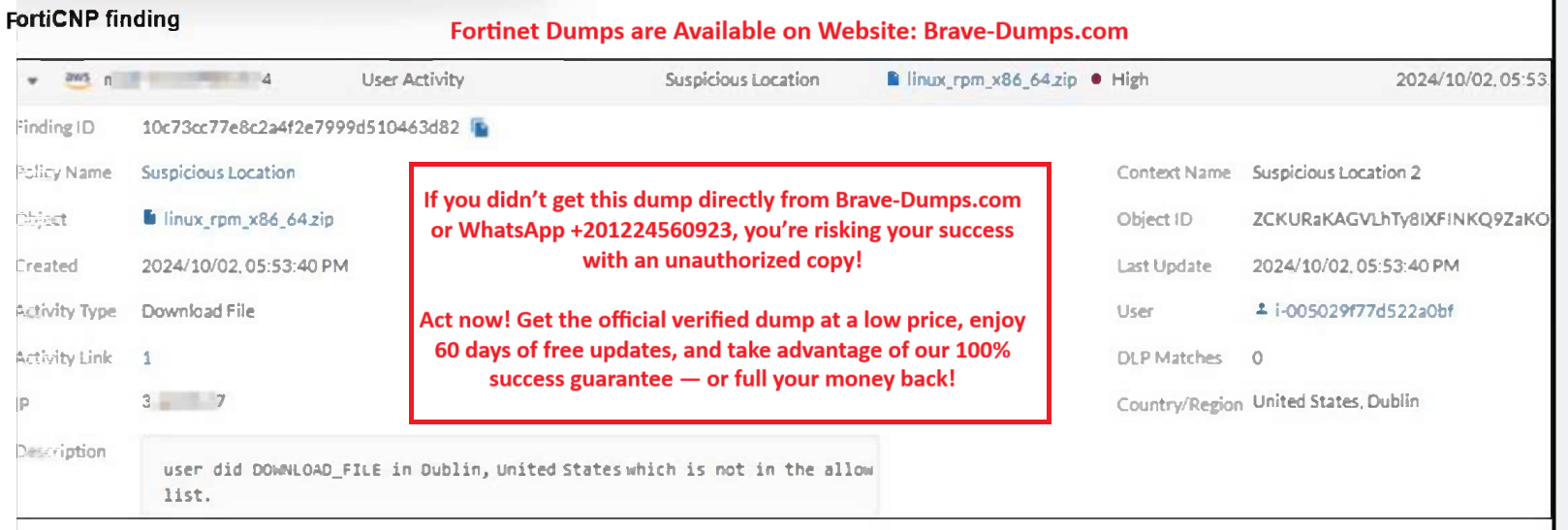
Refer to the exhibit.
Which FortiCNP policy type generated the finding shown in the exhibit?
(Choose one answer)
- A. This finding was generated by a data scan policy.
- B. This finding was generated by a threat detection policy.
- C. This finding was generated by a risk management policy.
- D. This finding was generated by a file collection policy.
Question #9
A Network security administrator is searching for a solution to secure traffic going in and out of the container infrastructure.
In which two ways can Fortinet container security help secure container infrastructures?
(Choose two answers)
- A. FortiGate NGFW and FortiWeb can be used to secure container traffic.
- B. FortiGate NGFW can connect to the worker nodes and protect the containers.
- C. FortiGate NGFW can inspect north-south container traffic with label aware policies.
- D. FortiGate NGFW can be placed between each application container for north-south traffic inspection.
Question #10
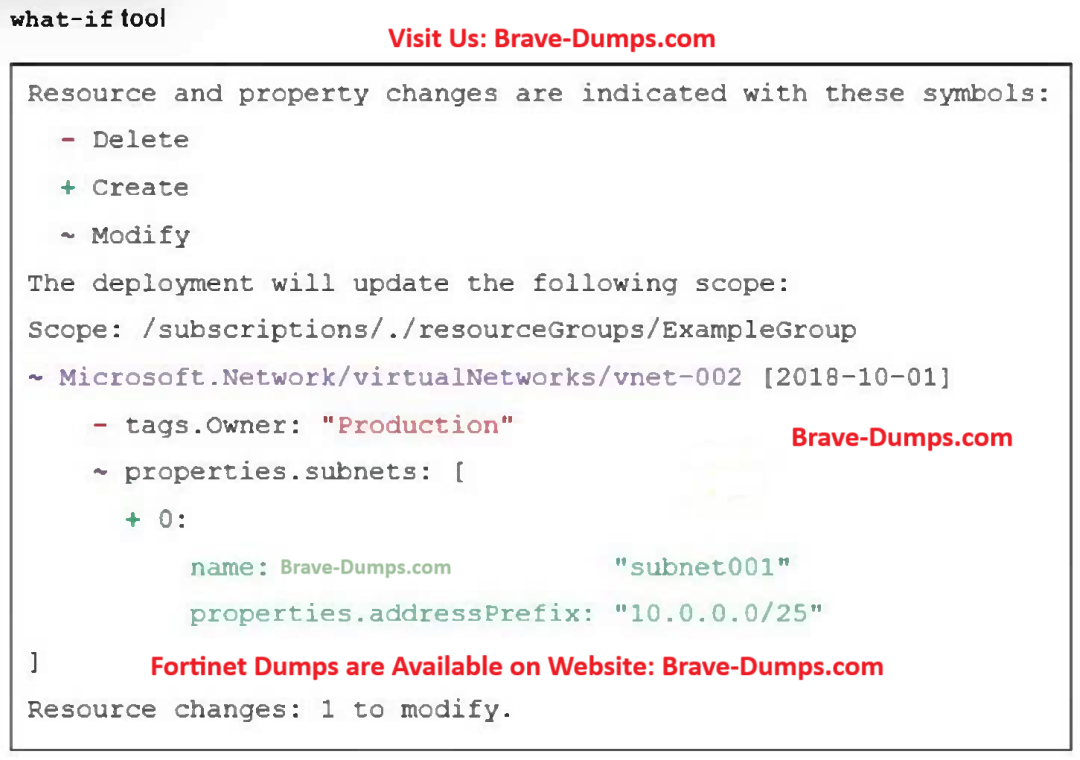
Refer to the exhibit.
An administrator used the what-if tool to preview the changes to an Azure Bicep file.
What will happen if the administrator applies these changes in Azure?
(Choose one answer)
- A. A new subnet will be added to vnet-002.
- B. The vnet-002 VNet will be renamed Production.
- C. The resulting VNet will have a single subnet.
- D. The VNet address space will be updated.
What are two main features in Amazon Web Services (AWS) network access control lists (NACLs)? (Choose two answers)