● NSE 7 - Enterprise Firewall 7.6 Administrator Exam Materials
● Over 50 Students Passed NSE 7 - Enterprise Firewall 7.6 Administrator Dump (FCSS_EFW_AD-7.6 Dump) Using This Dump – Join Them Today!
● Less Than 80 Verified Questions for the NSE 7 - Enterprise Firewall 7.6 Administrator Exam (FCSS_EFW_AD-7.6 Exam)
● 100% score in the Real NSE 7 - Enterprise Firewall 7.6 Administrator Exam (EFW_AD-7.6) at the Pearson VUE Testing Center
● Less Than 80 Verified Questions for the NSE 7 - Enterprise Firewall 7.6 Administrator Exam (FCSS_EFW_AD-7.6 Exam)
● 100% score in the Real NSE 7 - Enterprise Firewall 7.6 Administrator Exam (EFW_AD-7.6) at the Pearson VUE Testing Center
Question #1
Question #2
You must update a firewall policy to block multiple websites within the subnet 172.165.58.0/24.
What must you do to block these addresses efficiently?
(Choose one answer)
- A. Create a URL filter and apply the web filter profile to the firewall policy.
- B. Create an IP address external connector and apply it to the destination field of the firewall policy.
- C. Create an application sensor and apply the application control profile to the firewall policy.
- D. Create an Internet Service Database (ISDB) group and apply it to the destination field of the firewall policy.
Question #3
You receive a FortiAnalyzer alert warning that a 1 TB disk filled up in a day. Upon investigation, you find thousands of unusual DNS log requests, such as JHCMQK.website.com, with no answers. You later discover that DNS exfiltration is occurring through both UDP and TLS.
How can you prevent this data theft technique?
(Choose one answer)
- A. Enable DNS filter to protect against DNS exfiltration.
- B. Enable data loss prevention (DLP) to prevent DNS exfiltration.
- C. Use an intrusion prevention system (IPS) profile and DNS exfiltration-related signatures.
- D. Use a file filter profile to protect against DNS exfiltration.
Question #4
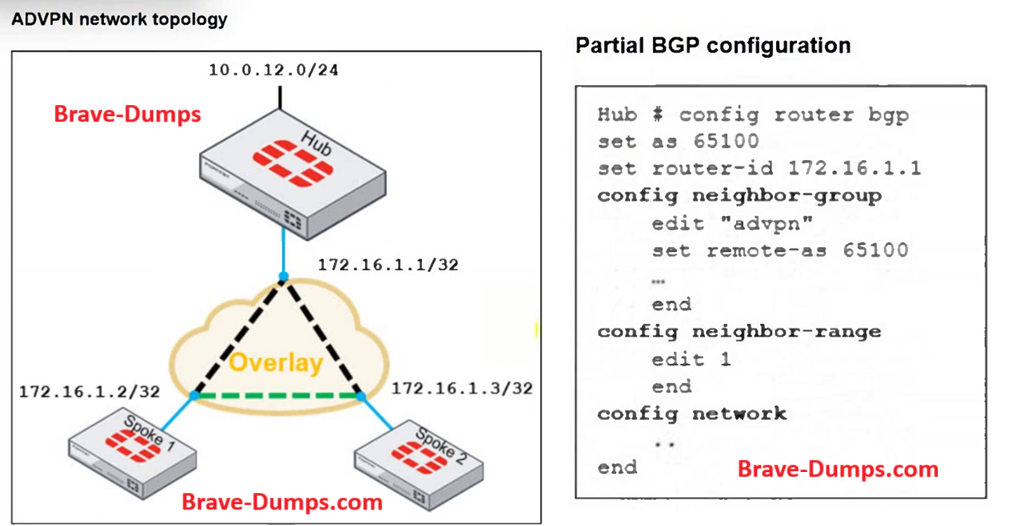
Refer to the exhibits.
The ADVPN network topology and partial BGP configuration are shown.
Which two parameters must you configure in the config neighbor range for spokes shown in the exhibit?
(Choose two answers)
- A. set neighbor-group advpn
- B. set prefix 172.16.1.0 255.255.255.0
- C. set prefix 10.0.12.0 255.255.255.0
- D. set route-reflector-client enable
Question #5
You are checking an enterprise network and see a suspicious packet with the MAC address 00:09:0f:09:18:81.
Which two statements about the suspicious packet are correct?
(Choose two answers)
- A. The suspicious packet is related to a cluster configured with the FortiGate Session Life Protocol (FGSP).
- B. The suspicious packet is related to a cluster that has VDOMs enabled.
- C. The suspicious packet corresponds to a port with a physical index equal to 2.
- D. The suspicious packet is related to a cluster with a group-id value lower than 255.
Question #6
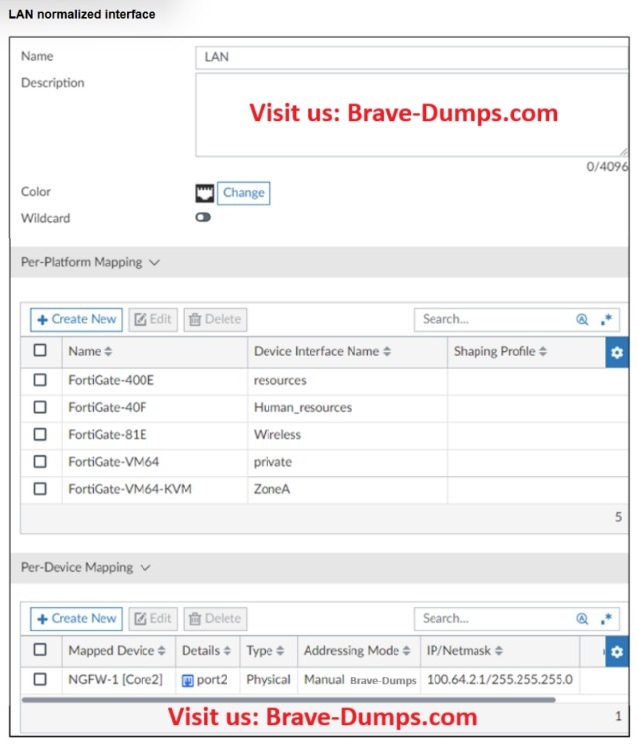
Refer to the exhibit.
A normalized interface LAN on FortiManager is shown.
Which two statements about this interface configuration are correct?
(Choose two answers)
- A. The normalized interface LAN will be mapped to the wireless interface for FortiGate-81E model devices.
- B. The normalized interface LAN will be mapped to the port2 interface for NGFW-1 [Core2].
- C. The normalized interface LAN will be mapped to the Human_Resources interface for any FortiGate-40F model devices.
- D. The normalized interface LAN will be mapped to the private interface for FortiGate-VM64 model devices.
Question #7
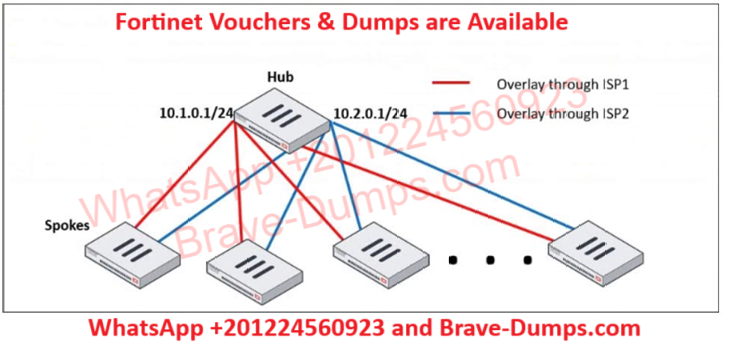
Refer to the exhibit.
A network diagram with a hub and spokes deployment is shown.
You must deploy several spokes, including the BGP configuration for the spokes that connect to the hub.
Which two commands would you use to minimize the amount of configuration needed on the hub?
(Choose two answers)
- A. ebgp-multipath
- B. neighbor-range
- C. route-overlap
- D. neighbor-group
Question #8
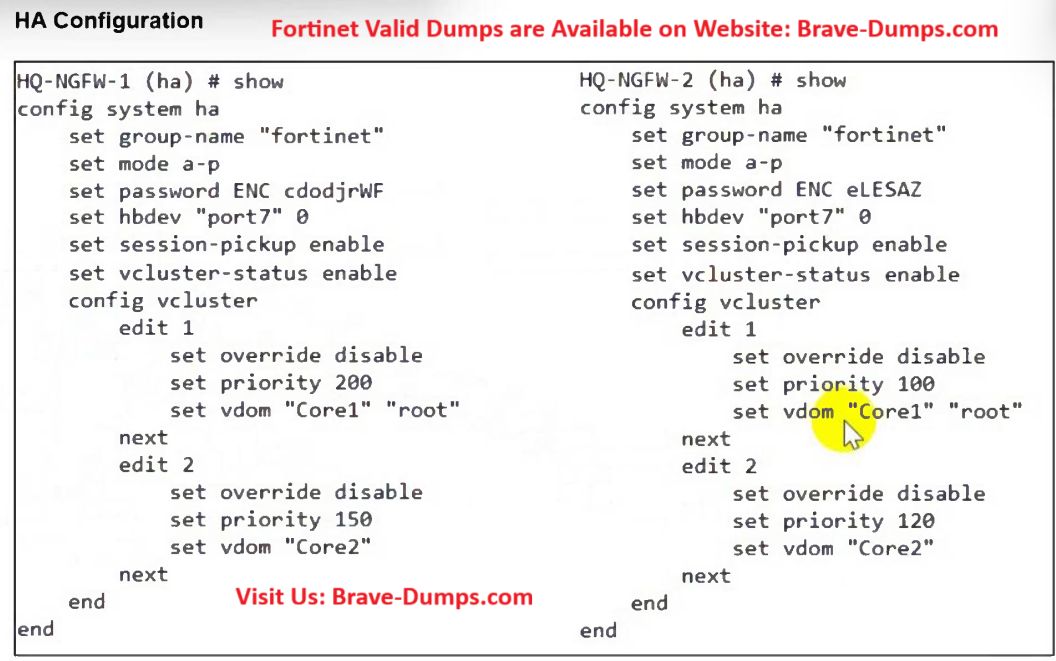
Refer to the exhibit.
An HA configuration of an active-active (A-A) cluster with the same HA uptime is shown.
You want HQ-NGFW-2 to handle the Core2 VDOM traffic.
Which modification must you make to achieve this outcome?
(Choose one answer)
- A. Reboot HQ-NGFW-2.
- B. Change the priority from 100 to 160 for HQ-NGFW-2.
- C. Change the priority from 120 to 200 for HQ-NGFW-2.
- D. Enable override in virtual cluster 2 for HQ-NGFW-2.
Question #9
During the last network migration, the IT department discovered that all zero phase selectors in phase 2 IPsec configurations impact network operations.
What are two valid recommendations to prevent potential invalid paths during future migrations?
(Choose two answers)
- A. Configure routing protocols to specify allowed subnets over the tunnel.
- B. Configure the VPN with the exact segments that will be encrypted in the phase two selectors.
- C. Configure an IPsec aggregate to create redundancy between each firewall peer
- D. Configure an IP address on the IPsec interface of each firewall to establish unique peer connections and avoid impacting network operations.
Question #10
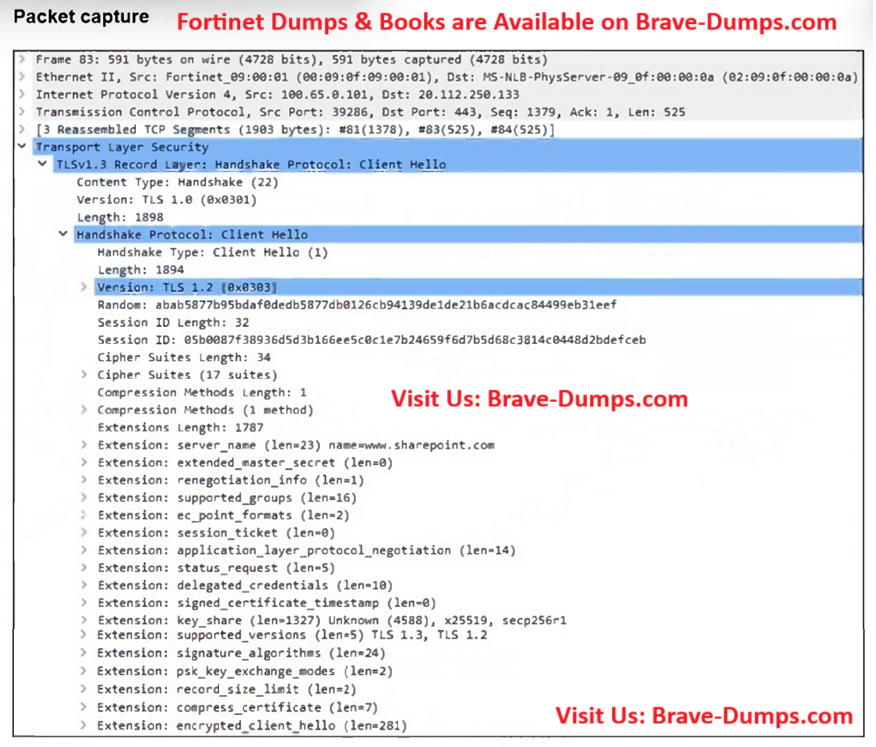
Refer to the exhibit.
The packet capture output of a client hello message is shown.
You are updating a firewall policy that includes SSL certificate inspection. You are capturing packets from the traffic passing through this firewall policy.
Which two statements about the packet capture are correct?
(Choose two answers)
- A. You can effectively apply a web filtering profile to this traffic.
- B. The subject alternative name (SAN) is necessary to apply security profiles.
- C. The client supports only TLS versions 1.2 and 1.3.
- D. You can effectively apply an antivirus security profile to this traffic.
If you implement IKEv2 in a VPN topology, which two statements are true? (Choose two answers)