● NSE 7 - FortiSASE 25 Enterprise Administrator Exam Materials
● Over 50 Students Passed FortiSASE 25 Enterprise Administrator (NSE7_SSE_AD-25) Using This Dump – Join Them Today!
● Less Than 80 Verified Questions for the NSE 7 - FortiSASE 25 Enterprise Administrator Dump (NSE7_SSE_AD-25 Dump)
● 100% Score in the Real FortiSASE 25 Enterprise Administrator Exam (NSE7_SSE_AD-25 Exam) at the Pearson VUE Testing Center
● Less Than 80 Verified Questions for the NSE 7 - FortiSASE 25 Enterprise Administrator Dump (NSE7_SSE_AD-25 Dump)
● 100% Score in the Real FortiSASE 25 Enterprise Administrator Exam (NSE7_SSE_AD-25 Exam) at the Pearson VUE Testing Center
Question #1
Question #2
What is the role of ZTNA tags in the FortiSASE Secure Internet Access (SIA) and Secure Private Access (SPA) use cases? (Choose one answer)
- A. ZTNA tags are created to isolate browser sessions in SIA and enforce data loss prevention in SPA for all devices.
- B. ZTNA tags determine device posture for non-web traffic protocols and are applied only in agentless deployments for SIA.
- C. ZTNA tags determine device posture for endpoints running FortiClient and are used to grant or deny access in SIA or SPA based on that posture
- D. ZTNA tags are applied to unmanaged endpoints without FortiClient to secure HTTP and HTTPS traffic in SIA and SPA.
Question #3
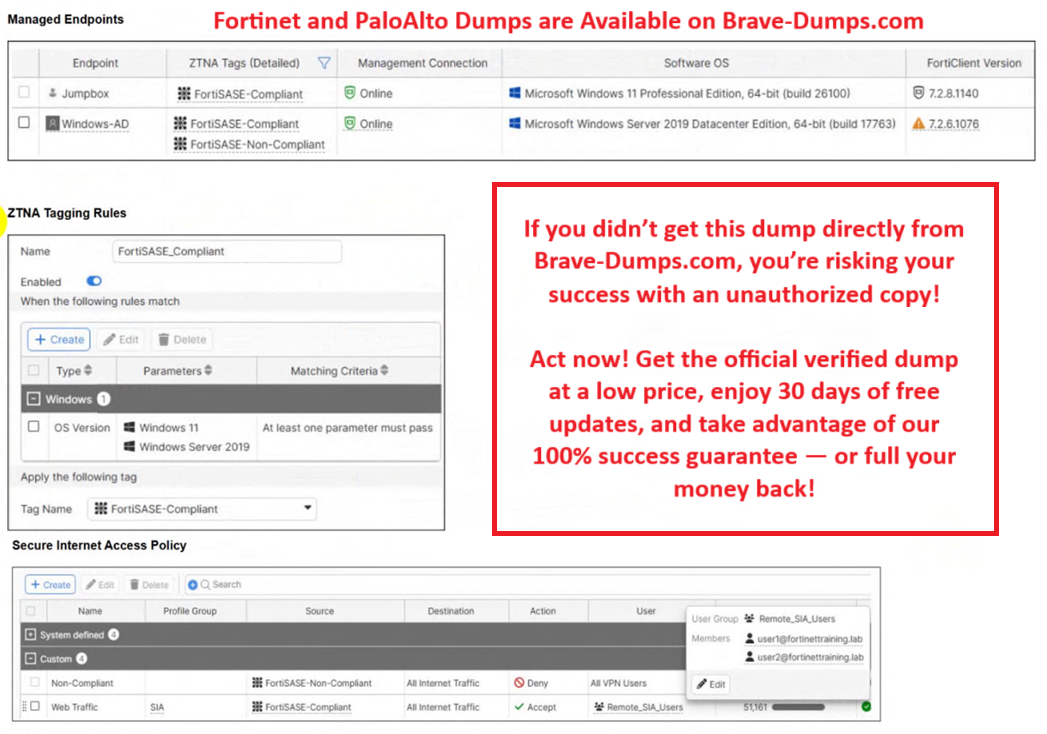
Refer to the exhibits.
Jumpbox and Windows-AD are endpoints from the same remote location. Jumpbox can access the internet through FortiSASE, while Windows-AD can no longer access the internet.
Based on the information in the exhibits, which reason explains the outage on Windows-AD?
(Choose one answer)
- A. The device security posture for Windows-AD has changed.
- B. The FortiClient version installed on Windows-AD does not match the expected version on FortiSASE.
- C. Windows-AD is excluded from FortiSASE management.
- D. The remote VPN user on Windows-AD no longer matches any VPN policy.
Question #4
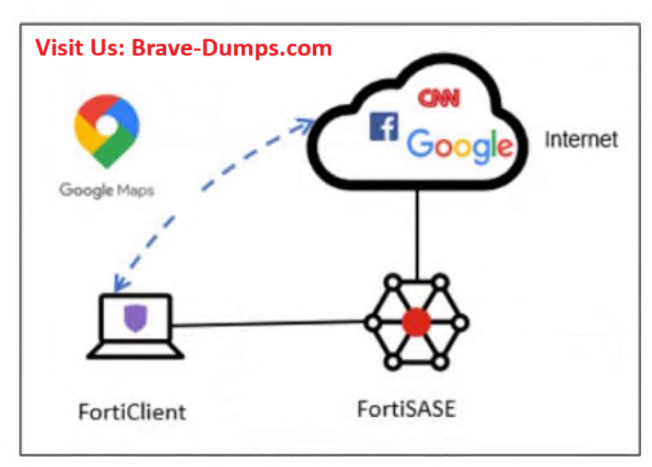
Refer to the exhibit.
An organization must inspect all the endpoint internet traffic on FortiSASE, and exclude Google Maps traffic from the FortiSASE tunnel and redirect it to the endpoint physical interface.
Which configuration must you apply to achieve this requirement?
(Choose one answer)
- A. Add the Google Maps URL in the zero trust network access (ZTNA) TCP access proxy forwarding rule.
- B. Configure a steering bypass tunnel firewall policy using Google Maps FQDN to exclude and redirect the traffic.
- C. Exempt Google Maps in URL filtering in the web filter profile.
- D. Add the Google Maps URL as a steering bypass destination in the endpoint profile.
Question #5
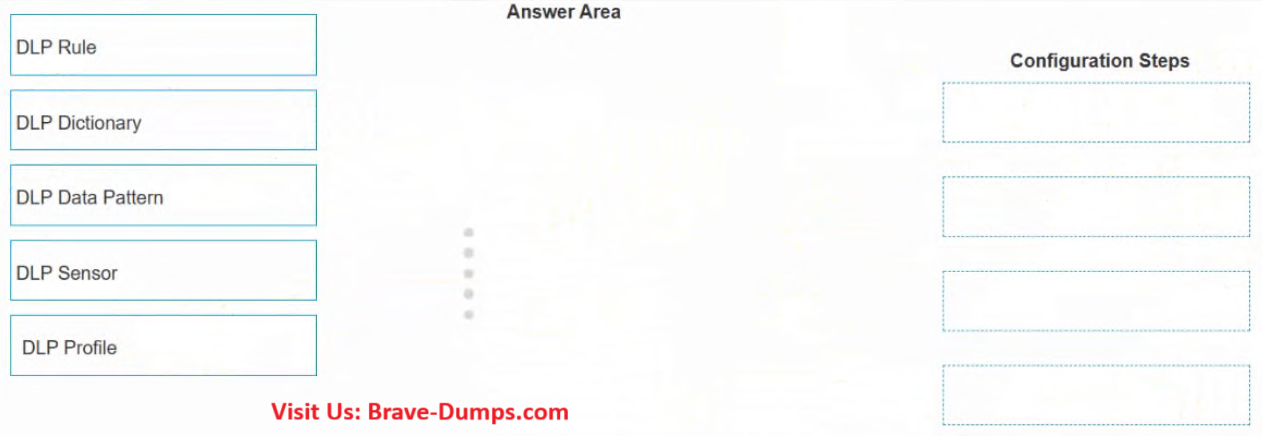
* Drag and Drop Question *
When configuring the DLP rule in FortiSASE using Regex format, what would be the correct order for the configuration steps?
Select the step in the left column, hold and drag it to a blank position in the column on the right. Place the four correct steps in order, placing the first step in the first position at the top of the column. Once you place a step, you can move it again if you want to change your answer before moving to the next question. You need to drop four steps in the work area.
Select and drag the screen divider to change the viewable area of the source and work areas.
(Choose four answers)
- A. Configuration Step1: DLP Data Pattern
- B. Configuration Step2: DLP Dictionary
- C. Configuration Step3: DLP Sensor
- D. Configuration Step4: DLP Profile
Question #6
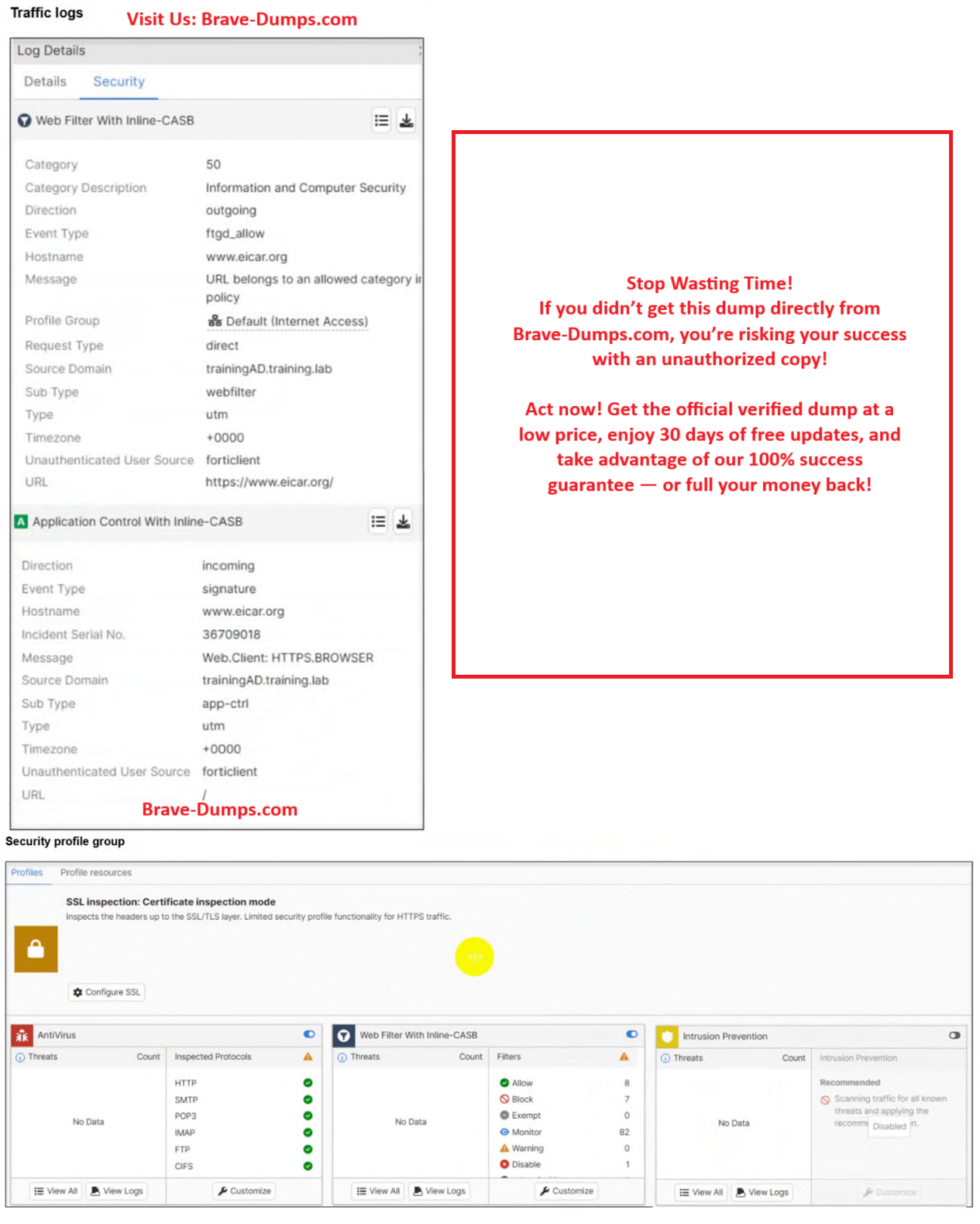
Refer to the exhibits.
A FortiSASE administrator has configured an antivirus profile in the security profile group and applied it to the internet access policy. Remote users are still able to download the eicar.com-zip file from https://eicar.org
.
Which configuration on FortiSASE is allowing users to perform the download?
(Choose one answer)
- A. Deep inspection is not enabled.
- B. Application control is exempting all the browser traffic.
- C. Web filter is allowing the URL.
- D. Intrusion prevention is disabled.
Question #7
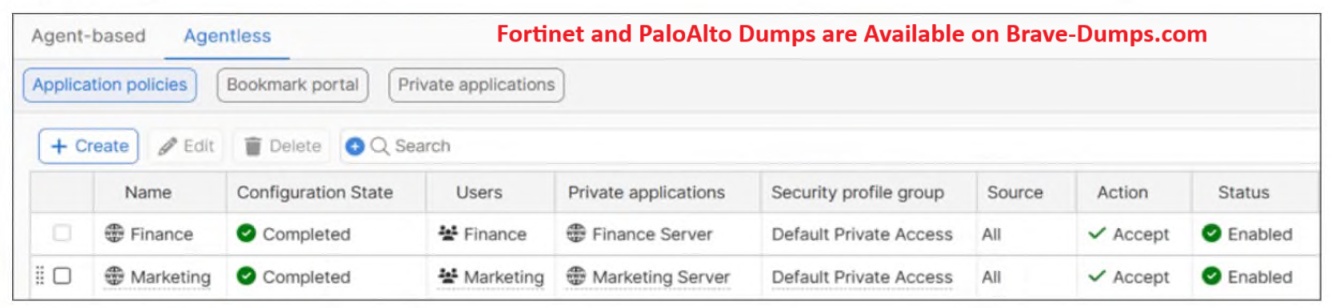
Refer to the exhibit.
Which two prerequisites must be met to use the feature shown in the exhibit?
(Choose two answers)
- A. The secure private access (SPA) feature must be configured in FortiSASE.
- B. The relevant FortiGate ZTNA application gateway must be configured.
- C. FortiClient must be installed on the user's device to access the private application.
- D. The proxy and proxy user single sign-on (SSO) features must be configured in FortiSASE.
Question #8
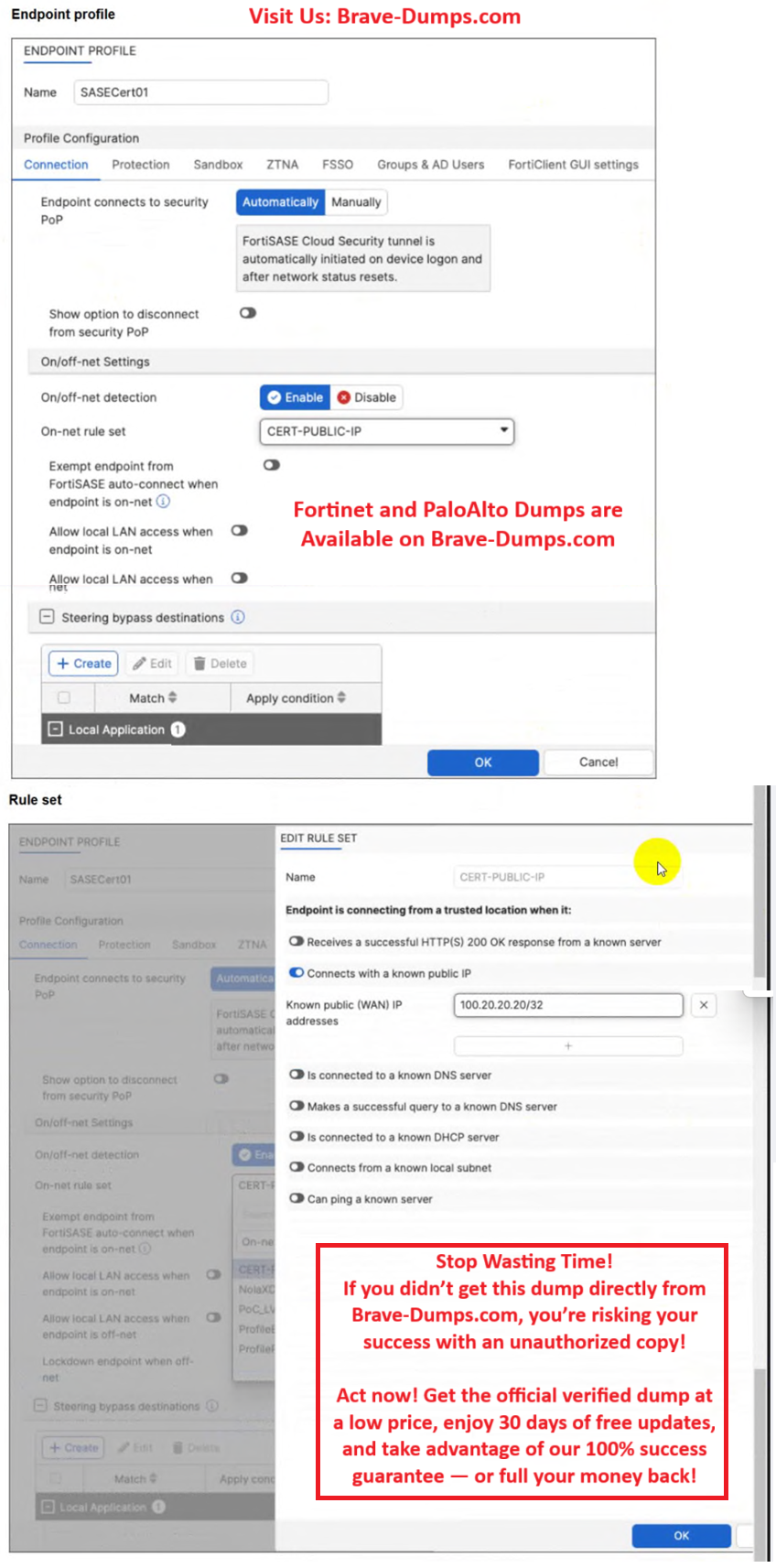
A customer configured the On/off-net detection rule to disable FortiSASE VPN auto-connect when users are inside the corporate network. The rule is set to Connects with a known public IP using the company’s public IP address. However, when the users are on the corporate network, the FortiSASE VPN still auto-connects. The customer has confirmed that traffic is going to the internet with the correct IP address.
Which configuration is causing the issue?
(Choose one answer)
- A. The On-net rule set configuration is incorrect.
- B. Allow local LAN access when endpoint is on-net is disabled when it should be enabled.
- C. Exempt endpoint from FortiSASE auto-connect is disabled when it should be enabled.
- D. Is connected to a known DNS server should be enabled and configured.
Question #9
How does FortiSASE Secure Private Access (SPA) facilitate connectivity to private resources in a hub-and-spoke network? (Choose one answer)
- A. SPA establishes direct links to spokes without IPsec or BGP and uses an easy configuration key to secure web traffic for remote users.
- B. SPA applies source network address translation (SNAT) for remote user traffic and uses IKEv1 for IPsec tunnels to connect to standalone hubs without BGP support.
- C. SPA connects to private resources using HTTP and HTTPS protocols and relies on FortiClient for agentless access to SD-WAN deployments.
- D. SPA connects a FortiSASE POP to a FortiGate hub or SD-WAN deployment using IPsec and BGP for dynamic route exchange with an easy configuration key for simplified setup on FortiOS.
Question #10
For monitoring potentially unwanted applications on endpoints, which information is available on the FortiSASE software installations page? (Choose two answers)
- A. The endpoint the software is installed on
- B. The license status of the software
- C. The vendor of the software
- D. The usage frequency of the software
Which authentication method overrides any other previously configured user authentication on FortiSASE? (Choose one answer)