● NSE 5 - FortiNAC-F 7.6 Administrator Exam Materials
*
● Over 20 Students Passed Fortinet NSE 5 - FortiNAC-F 7.6 Administrator NSE5_FNC_AD_7.6) Using This Dump – Join Them Today!
● Less Than 80 Verified Questions for the NSE 5 - FortiNAC-F 7.6 Administrator Dump (NSE5_FNC_AD_7.6 Dump)
● 100% Score in the Real FortiNAC-F 7.6 Administrator Exam (NSE5_FNC_AD_7.6 Exam) at the Pearson VUE Testing Center
*
● Over 20 Students Passed Fortinet NSE 5 - FortiNAC-F 7.6 Administrator NSE5_FNC_AD_7.6) Using This Dump – Join Them Today!
● Less Than 80 Verified Questions for the NSE 5 - FortiNAC-F 7.6 Administrator Dump (NSE5_FNC_AD_7.6 Dump)
● 100% Score in the Real FortiNAC-F 7.6 Administrator Exam (NSE5_FNC_AD_7.6 Exam) at the Pearson VUE Testing Center
*
Question #1

Question #2
When configuring isolation networks in the configuration wizard, why does a layer 3 network type allow for more than one DHCP scope for each isolation network type? (Choose one answer)
- A. The layer 3 network type allows for one scope for each possible host status.
- B. Configuring more than one DHCP scope allows for DHCP server redundancy.
- C. There can be more than one isolation network of each type.
- D. Any scopes beyond the first scope are used if the initial scope runs out of IP addresses.
Question #3
When FortiNAC-F is managing VPN clients connecting through FortiGate, why must the clients run a FortiNAC-F agent? (Choose one answer)
- A. To transparently update the client IP address upon successful authentication
- B. To collect user authentication details
- C. To collect the client IP address and MAC address
- D. To validate the endpoint policy compliance
Question #4
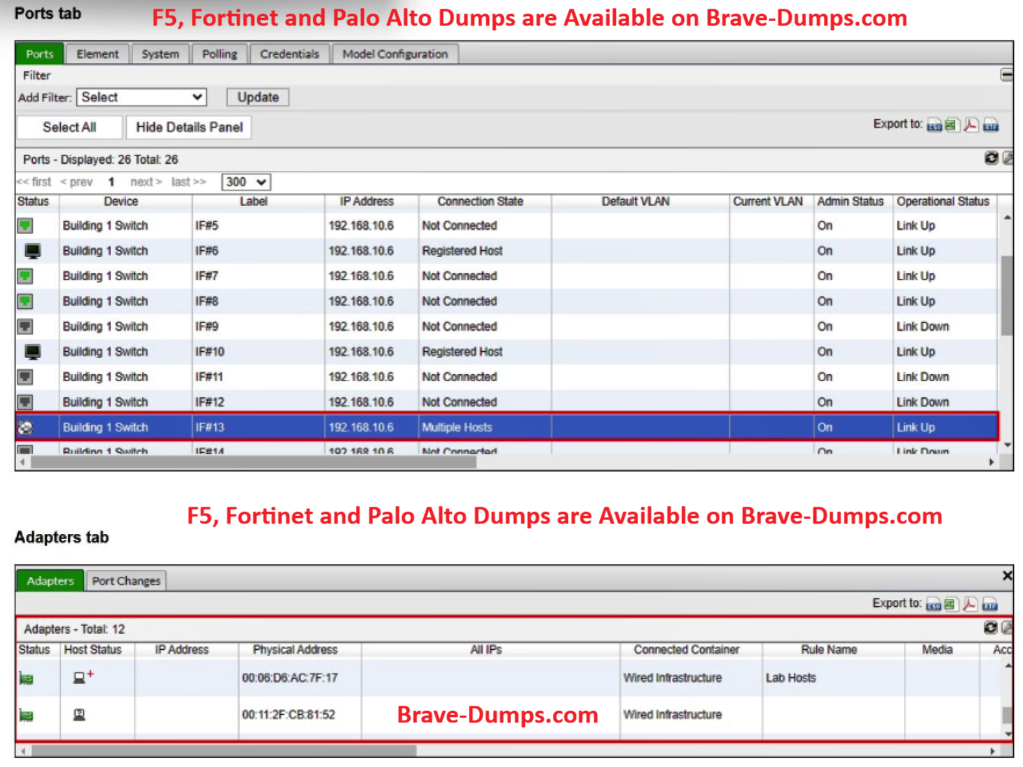
Refer to the exhibits.
What would happen if the highlighted port with connected hosts was placed in both the Forced Registration and Forced Remediation port groups?
(Choose one answer)
- A. Both types of enforcement would be applied.
- B. Enforcement would be applied only to rogue hosts.
- C. Multiple enforcement groups could not contain the same port.
- D. Only the higher ranked enforcement group would be applied.
Question #5
An administrator wants to build a security rule that will quarantine contractors who attempt to access specific websites.
In addition to a user host profile, which two components must the administrator configure to create the security rule?
(Choose two answers)
- A. Methods
- B. Action
- C. Endpoint compliance policy
- D. Trigger
- E. Security String
Question #6
A user was attempting to register their host through the registration captive portal. After successfully registering, the host remained in the registration VLAN.
Which two conditions would cause this behavior?
(Choose two answers)
- A. The wrong agent is installed.
- B. There is no agent installed on the host.
- C. The port default VLAN is the same as the Registration VLAN.
- D. There is another unregistered host on the same port.
Question #7
While discovering network infrastructure devices, a switch appears in the inventory topology with a question mark (?) on the icon.
What would cause this?
(Choose one answer)
- A. The wrong SNMP community string was entered during discovery.
- B. The SNMP ObjectID is not recognized by FortiNAC-F.
- C. A read-only SNMP community string was used.
- D. SNMP is not enabled on the switch.
Question #8
An administrator manages a corporate environment where all users log into the corporate domain each time they connect to the network. The administrator wants to leverage login scripts to use a FortiNAC-F agent to enhance endpoint visibility.
Which agent can be deployed as part of a login script?
(Choose one answer)
- A. Persistent
- B. Dissolvable
- C. Mobile
- D. Passive
Question #9
An administrator wants to control user access to corporate resources by integrating FortiNAC-F with FortiGate using firewall tags defined on FortiNAC-F.
Where would the administrator assign the firewall tag value that will be sent to FortiGate?
(Choose one answer)
- A. RADIUS group attribute
- B. Logical network
- C. Device profiling rule
- D. Security rule
Question #10
Which two requirements must be met to set up an N+1 HA cluster? (Choose two answers)
- A. A FortiNAC-F manager
- B. A FortiNAC-F device designated as a secondary
- C. A dedicated VLAN for primary and secondary synchronization
- D. At least two FortiNAC-F devices designated as primary
Refer to the exhibit.
What would FortiNAC-F generate if only one of the security filters is satisfied? (Choose one answer)