● F5 BIG-IP ASM Specialist (303) Exam Materials
Question #1
Question #2
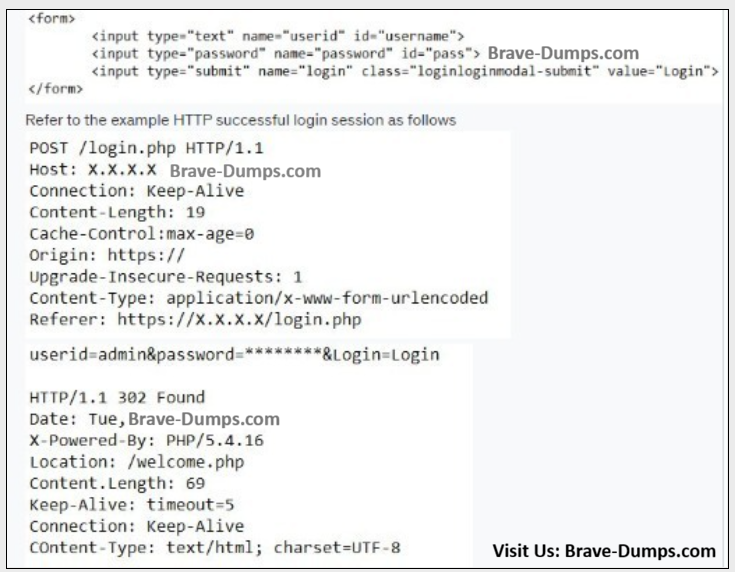
An ASM Specialist needs to configure a login page based on the following form:
What are the correct settings for the login page?
(Choose one answer)
- A. Login URL: Explicit HTTPS /login.php Expected HTTP response status code: 302
- B. Login URL: Explicit HTTP /welcome.php Expected HTTP response status code: 200
- C. Login URL: Explicit HTTPS /welcome.php Expected HTTP response status code: 200
- D. Login URL: Explicit HTTP /login.php Expected HTTP response status code: 302
Question #3
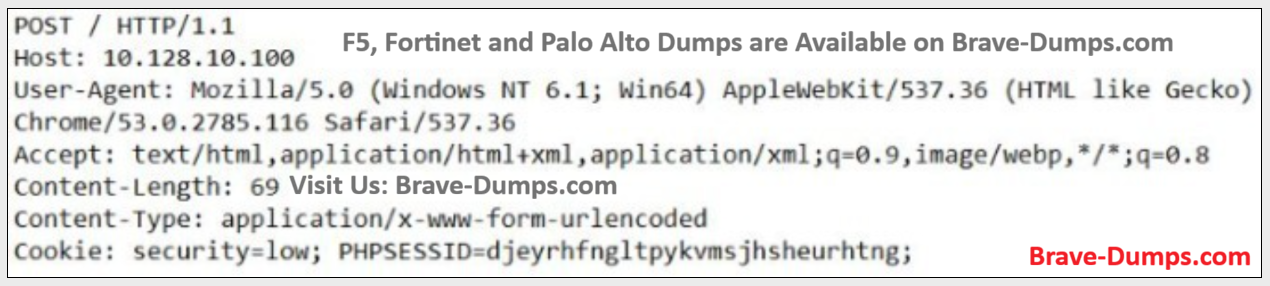
Refer to the exhibit.
Which option should an ASM Specialist configure in the policy to mitigate the potential attacks in the request?
(Choose one answer)
- A. add the header Upgrade-Insecure-Requests to the policy
- B. create the cookie "security" as an Enforced Cookie
- C. enable HTTP Protocol Compliance Failed violation
- D. apply the Generic Detection Signatures set
Question #4
An ASM Specialist finds that bots are continuously making username and password attempts on the login page of an organization’s web application.
What is a potential effect on the web application?
(Choose one answer)
- A. reduced memory utilization of the application
- B. randomly locked accounts
- C. reduced application latency
- D. application server reboot
Question #5
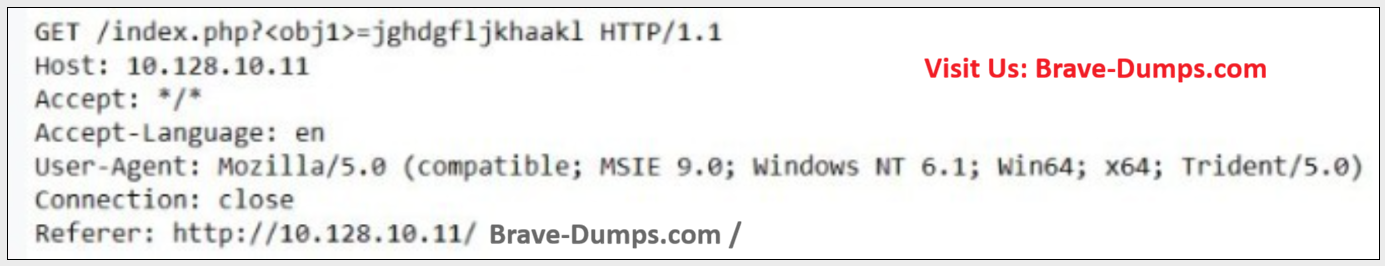
Review the following request
An ASM Specialist is modifying a security policy and must allow the web request shown through the ASM to a critical application.
How should the ASM Specialist meet this request and support security objectives?
(Choose one answer)
- A. modify allowed meta characters
- B. disable XSS signatures
- C. validate headers for HTTP 1.1
- D. permit the Trident 5.0 User Agent
Question #6
While reviewing the ASM Policy status, an ASM Specialist discovers URLs that contain %APPDATA%.
Which type of common attack does this represent?
(Choose one answer)
- A. Content Spoofing
- B. Predictable Resource Location
- C. Command Execution
- D. Format String Attack
Question #7
An ASM Specialist enables Data Guard to prevent credit card numbers from being exposed in several legacy applications. Users report that it takes too long to download files through these applications.
Which Data Guard configuration changes should the ASM Specialist make to resolve the issue?
(Choose one answer)
- A. configure an ignored URLs list for approved documents
- B. create custom patterns to match credit card numbers only
- C. disable mask data
- D. enable exception patterns for Word and PDF documents
Question #8
An e-commerce website sets a cookie on the client machine specifying that the user is eligible for a 25% discount on the user’s next visit (Brave-Dumps.com) The user maliciously changes the content of this cookie to specify that they are eligible for a 100% discount on their next visit.
How should an ASM Specialist adjust the configuration to protect the website while the ASM module is in Blocking mode?
(Choose one answer)
- A. make sure that the "Block" checkbox for "ASM cookie hijacking" is checked
- B. check the "Block" checkbox for "Cookie not RFC- Compliant"
- C. add cookie to "Enforced Cookies" list
- D. add cookie to "Allow Cookies" list
Question #9
An ASM Specialist recently modified the ASM configuration to respond to an ongoing DoS attack on the protected website. The ASM policy of the website is in Blocking mode.
The Stress-based DoS Detection settings are as follows:
- Blocking
- Detection by Source IP
- Mitigation of Client Side Integrity Defense
- Standard Protection in Behavioral settings
- Visit Brave-Dumps.com for original dump copy
Which method should the ASM Specialist use to determine if the attack has been successfully mitigated?
(Choose one answer)
- A. review the Historical and Recent Attacks log and look for the flag of an attack in progress
- B. make sure that Bot Signature Checking is working by verifying that Googlebot or other friendly bots can reach the website
- C. check the Dashboard to make sure that the CPU and memory usage on the Web Server have returned to normal pre-attack levels
- D. look for Client Side Integrity Defense log entries on the website servers to verify that protection is in place.
Question #10
index.php?name=<script>window.onload = function() {var link=document.getElementByTagName("a");link[0].href="http://mybank.com";} ;</script>
Which learning suggestion should be generated by the request shown?
(Choose one answer)
- A. Attack Signature Detected - Cross-Site Request Forgery (CSRF)
- B. Attack Signature Detected - JavaScript buffer overflow attempt
- C. attack signature Detected - Cross-Site Scripting (XSS)
- D. Attack Signature Detected - XPath injection Script
Which setting should an ASM Specialist configure on an ASM module before a WhiteHat Sentinel scanner vulnerability can be imported? (Choose one answer)