● FCP - FortiAuthenticator 6.5 Administrator Exam Materials
Please note that the exam "FCP - FortiAuthenticator 6.5 Administrator" is no longer offered by Fortinet and is not available for booking through Pearson VUE, so we opened it on free view,
Question #1
Question #2
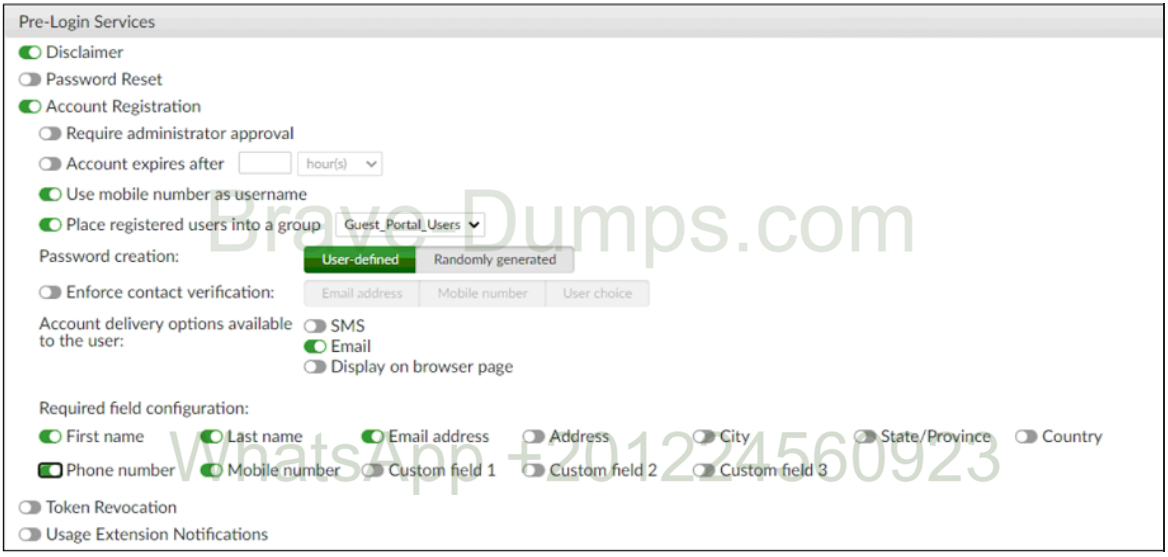
Examine the screenshot shown in the exhibit.
Which two statements regarding the configuration are true?
(Choose two answers)
- A. All guest accounts created using the account registration feature will be placed under the Guest_Portal_Users group.
- B. Guest user account will expire after eight hours.
- C. All accounts registered through the guest portal must be validated through email.
- D. Guest users must fill in all the fields on the registration form.
Question #3
When generating a TOTP for two-factor authentication, what two pieces of information are used by the algorithm to generate the TOTP? (Choose one answer)
- A. Time and FortiAuthenticator serial number
- B. Time and mobile location
- C. Time and seed
- D. UUID and time
Question #4
Which interface service must be enabled for the SCEP client to connect to FortiAuthenticator? (Choose one answer)
- A. HTTP/HTTPS
- B. SSH
- C. REST API
- D. OCSP
Question #5
An administrator wants to keep local CA cryptographic keys stored in a central location.
Which FortiAuthenticator feature would provide this functionality?
(Choose one answer)
- A. Network HSM
- B. SCEP support
- C. SFTP server
- D. REST API
Question #6
A system administrator wants to integrate FortiAuthenticator with an existing identity management system with the goal of authenticating and deauthenticating users into FSSO.
What feature does FortiAuthenticator offer for this type of integration?
(Choose one answer)
- A. RADIUS learning mode for migrating users
- B. SNMP monitoring and traps
- C. The ability to import and export users from CSV files
- D. REST API
Question #7
Which option correctly describes an SP-initiated SSO SAML packet flow for a host without a SAML assertion? (Choose one answer)
- A. Service provider contacts identity provider, identity provider validates principal for service provider, service provider establishes communication with principal
- B. Principal contacts identity provider and authenticates, identity provider relays principal to service provider after valid authentication
- C. Principal contacts service provider, service provider redirects principal to identity provider; after successful authentication identity provider redirects principal to service provider
- D. Principal contacts identity provider and is redirected to service provider, principal establishes connection with service provider, service provider validates authentication with identity provider
Question #8
How can a SAML metadata file be used? (Choose one answer)
- A. To import the required IDP configuration
- B. To resolve the IDP realm for authentication
- C. To define a list of trusted user names
- D. To correlate the IDP address to its hostname
Question #9
Which EAP method is known as the outer authentication method? (Choose one answer)
- A. PEAP
- B. MSCHAPv2
- C. EAP-GTC
- D. EAP-TLS
Question #10
Which of the following is an OATH-based standard to generate event-based, one-time password tokens? (Choose one answer)
- A. SOTP
- B. OLTP
- C. HOTP
- D. TOTP
You are an administrator for a large enterprise and you want to delegate the creation and management of guest users to a group of sponsors.
How would you associate the guest accounts with individual sponsors? (Choose one answer)