● FCSS - FortiSASE 24 Administrator Exam Materials
Please note that the exam "FCSS - FortiSASE 24 Administrator Exam" is no longer offered by Fortinet and is not available for booking through Pearson VUE, so we opened it on free view,
It has been replaced by the exam "NSE 7 - FortiSASE 25 Enterprise Administrator Exam"
The new exam version is available on Brave-Dumps and can be purchased.
It has been replaced by the exam "NSE 7 - FortiSASE 25 Enterprise Administrator Exam"
The new exam version is available on Brave-Dumps and can be purchased.
Question #11
Question #12
You are designing a new network for Company X and one of the new cybersecurity policy requirements is that all remote users working from home must always be connected and protected.
Which FortiSASE component facilitates this always-on security measure?
(Choose one answer)
- A. Unified FortiClient
- B. Thin-branch SASE extension
- C. Cloud access security broker
- D. Secure web gateway
Question #13
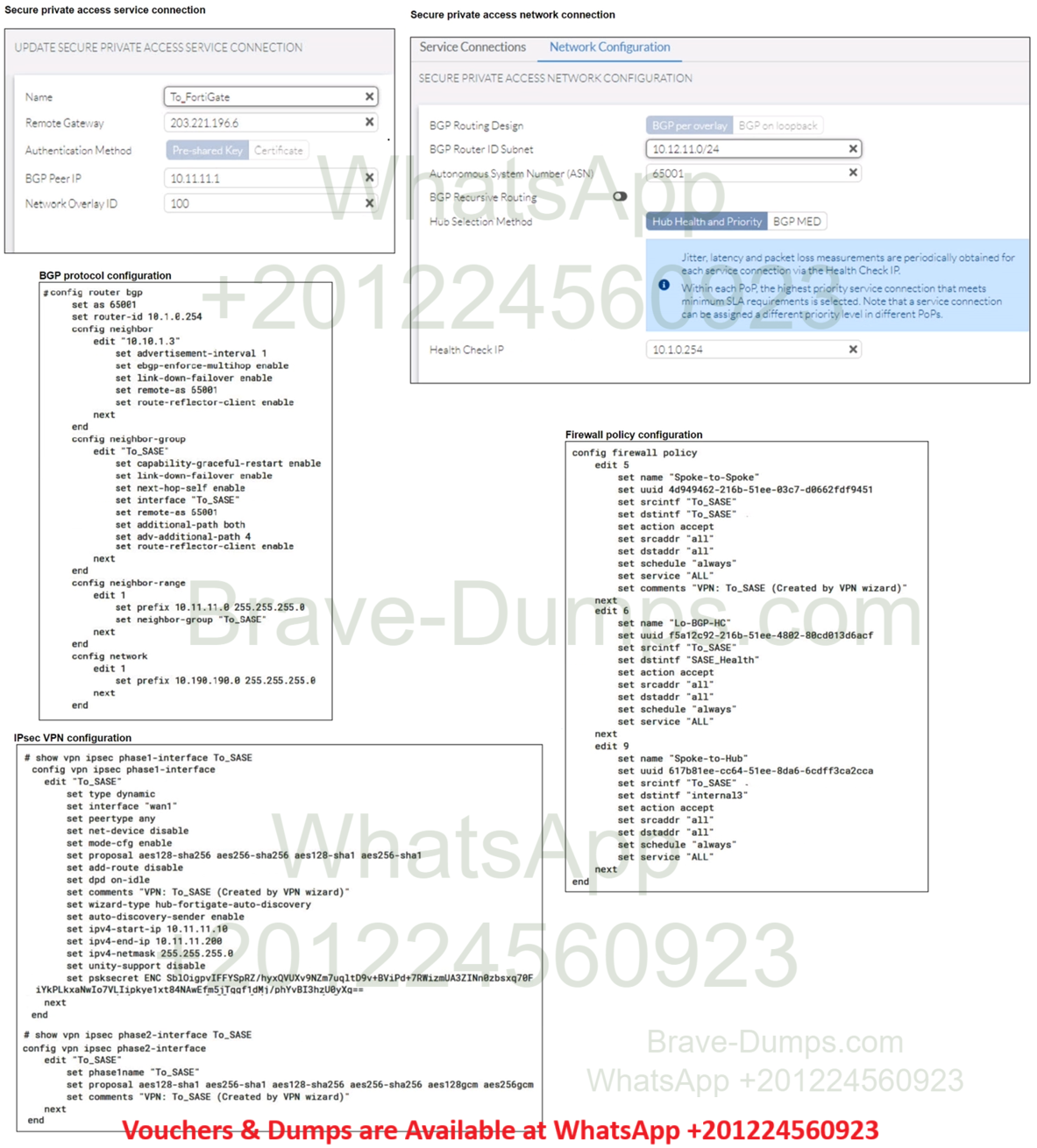
A FortiSASE administrator is trying to configure FortiSASE as a spoke to a FortiGate hub. The VPN tunnel does not establish.
Based on the provided configuration, what configuration needs to be modified to bring the tunnel up?
(Choose one answer)
- A. FortiSASE spoke devices do not support mode config.
- B. The hub needs IKEv2 enabled in the IPsec phase 1 settings.
- C. NAT needs to be enabled in the Spoke-to-Hub firewall policy.
- D. The BGP router ID needs to match on the hub and FortiSASE.
Question #14
A customer needs to implement device posture checks for their remote endpoints while accessing the protected server.
They also want the TCP traffic between the remote endpoints and the protected servers to be processed by FortiGate.
In this scenario, which three setups will achieve the above requirements?
(Choose three answers)
- A. Sync ZTNA tags from FortiSASE to FortiGate.
- B. Configure ZTNA tags on FortiGate.
- C. Configure FortiGate as a zero trust network access (ZTNA) access proxy.
- D. Configure ZTNA servers and ZTNA policies on FortiGate.
- E. Configure private access policies on FortiSASE with ZTNA.
Question #15
In which three ways does FortiSASE help organizations ensure secure access for remote workers? (Choose three answers)
- A. It offers zero trust network access (ZTNA) capabilities.
- B. It uses the identity & access management (IAM) portal to validate the identities of remote workers.
- C. It secures traffic from endpoints to cloud applications.
- D. It enforces granular access policies based on user identities.
- E. It enforces multi-factor authentication (MFA) to validate remote users
Question #16
A FortiSASE administrator is configuring a Secure Private Access (SPA) solution to share endpoint information with a corporate FortiGate.
Which three configuration actions will achieve this solution?
(Choose three answers)
- A. Authorize the corporate FortiGate on FortiSASE as a ZTNA access proxy.
- B. Apply the FortiSASE zero trust network access (ZTNA) license on the corporate FortiGate.
- C. Add the FortiGate IP address in the secure private access configuration on FortiSASE.
- D. Use the FortiClient EMS cloud connector on the corporate FortiGate to connect to FortiSASE.
- E. Register FortiGate and FortiSASE under the same FortiCloud account.
Question #17
When deploying FortiSASE agent-based clients, which three features are available compared to an agentless solution? (Choose three answers)
- A. Anti-ransomware protection
- B. SSL inspection
- C. Vulnerability scan
- D. ZTNA tags
- E. Web filter
Question #18
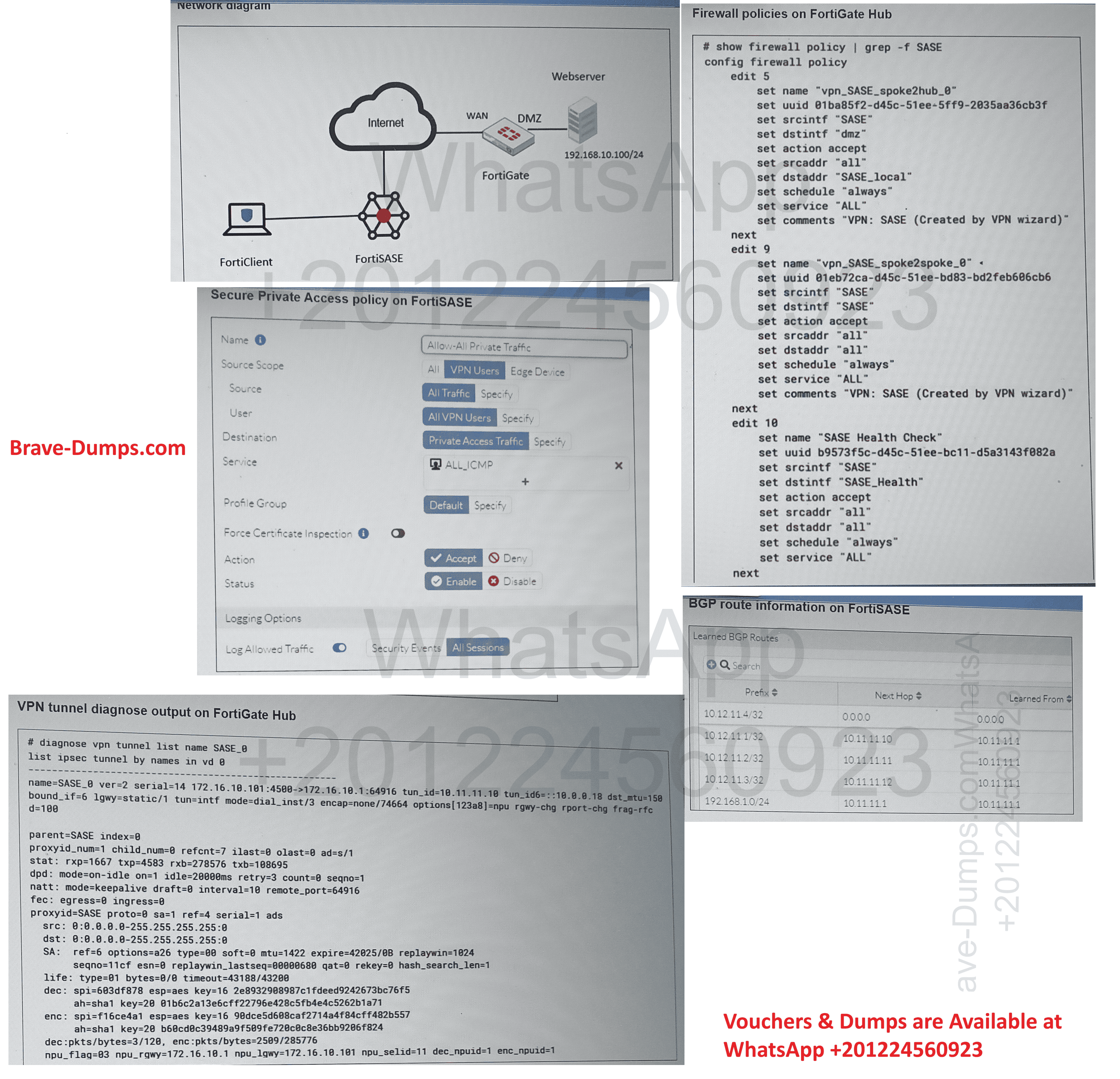
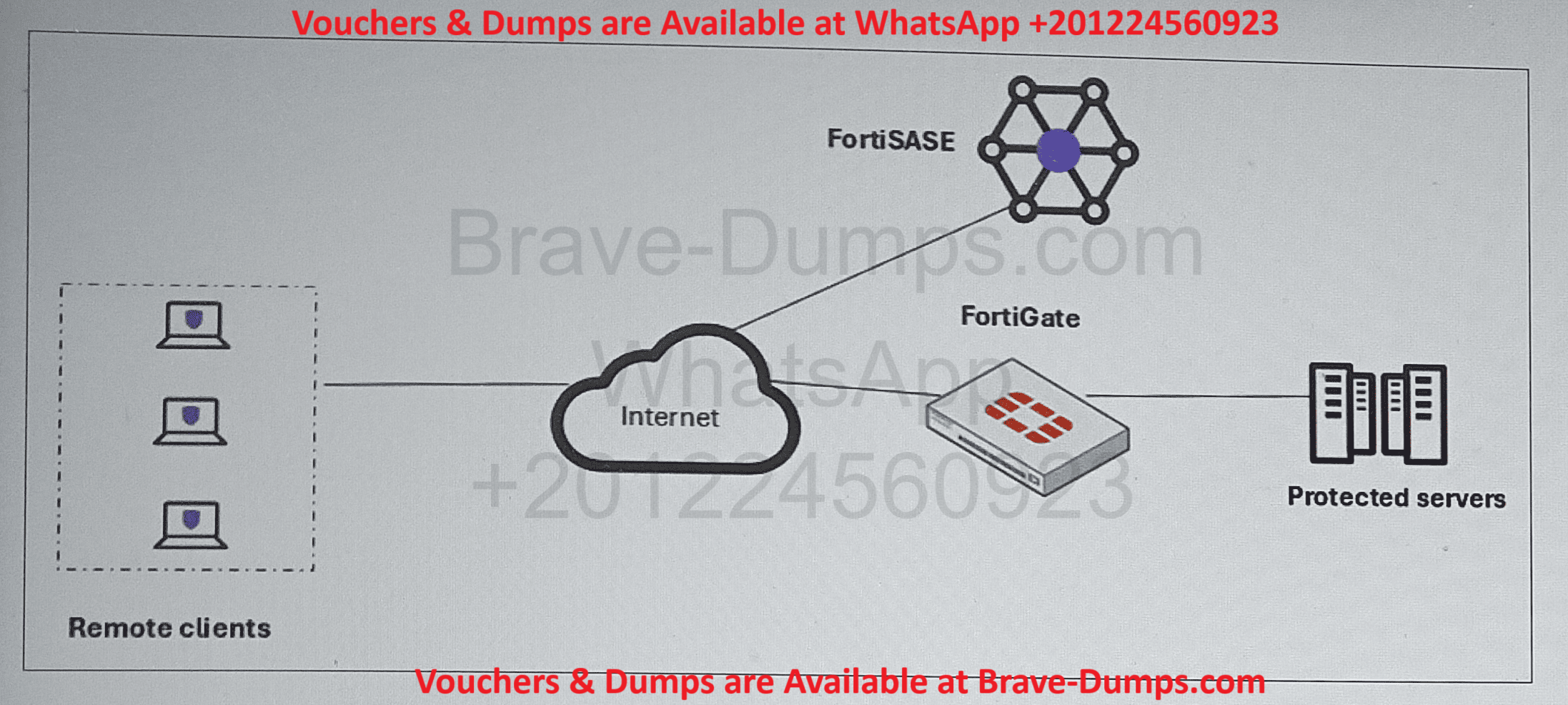
Refer to the exhibits.
A FortiSASE administrator is trying to configure FortiSASE as a spoke to a FortiGate hub. The tunnel is up to the FortiGate hub. However, the administrator is not able to ping the webserver hosted behind the FortiGate hub.
Based on the output, what is the reason for the ping failures?
(Choose one answer)
- A. Quick mode selectors are restricting the subnet.
- B. The BGP route is not received.
- C. Network address translation (NAT) is not enabled on the spoke-to-hub policy.
- D. The Secure Private Access (SPA) policy needs to allow PING service.
Question #19
What are two advantages of using zero-trust tags? (Choose two answers)
- A. Zero-trust tags can help in diagnosing connectivity issues.
- B. Zero-trust tags can be used to allow or deny access to network resources.
- C. Zero-trust tags can determine the security posture of an endpoint.
- D. Zero-trust tags can be assigned to endpoint profiles based on user groups.
Question #20
Which secure internet access (SIA) use case minimizes individual endpoint configuration? (Choose one answer)
- A. Agentless remote user internet access
- B. SIA for SSL VPN remote users
- C. SIA using ZTNA
- D. Site-based remote user internet access
Your organization is currently using FortiSASE for its cybersecurity. They have recently hired a contractor who will work from the HQ office and who needs temporary internet access in order to set up a web-based point of sale (POS) system.
What is the recommended way to provide internet access to the contractor? (Choose one answer)