● FCSS - FortiSASE 24 Administrator Exam Materials
Please note that the exam "FCSS - FortiSASE 24 Administrator Exam" is no longer offered by Fortinet and is not available for booking through Pearson VUE, so we opened it on free view,
It has been replaced by the exam "NSE 7 - FortiSASE 25 Enterprise Administrator Exam"
The new exam version is available on Brave-Dumps and can be purchased.
It has been replaced by the exam "NSE 7 - FortiSASE 25 Enterprise Administrator Exam"
The new exam version is available on Brave-Dumps and can be purchased.
Question #51
Question #52
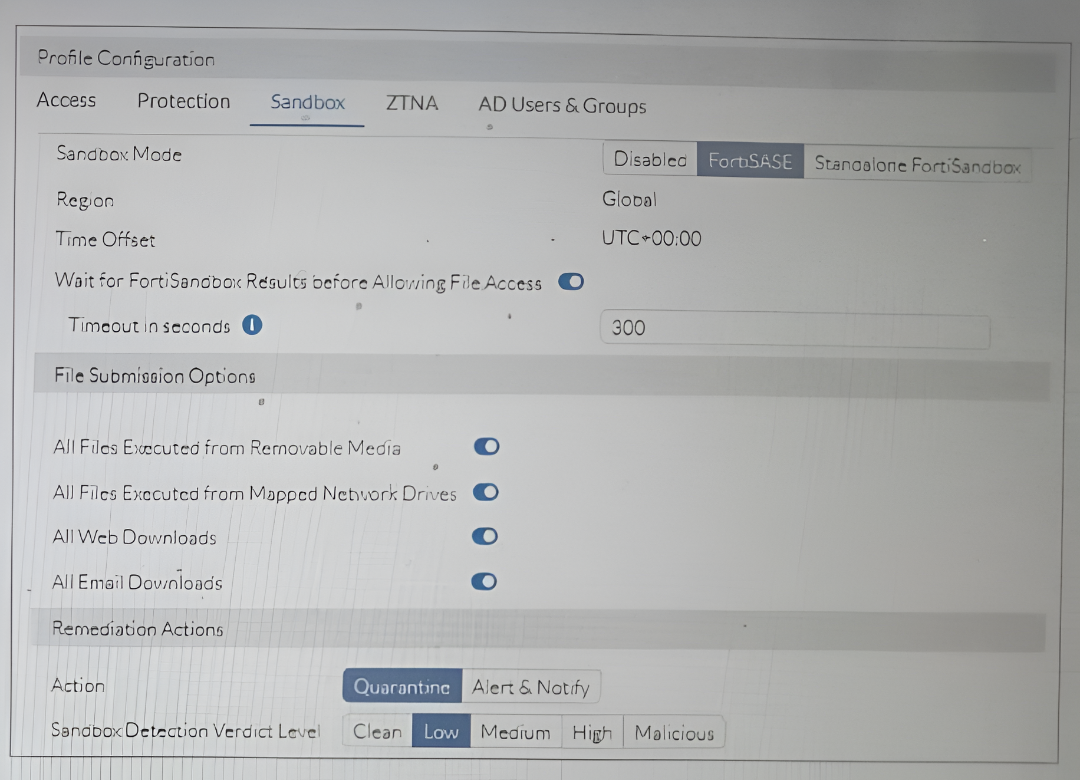
Refer to the exhibit.
Based on the configuration shown, in which two ways will FortiSASE process sessions that require FortiSandbox inspection?
(Choose two answers)
- A. FortiSASE will quarantine all infected files that FortiSandbox detects as malicious.
- B. FortiSandbox will scan only files that are found on off-net endpoints.
- C. The sandbox feature only works for endpoints assigned with policy for Sandbox Detection.
- D. FortiSASE will submit all files that it detects on a USB drive to FortiSandbox for analysis.
Question #53
Which two settings are automatically pushed from FortiSASE to FortiClient in a new FortiSASE deployment with default settings? (Choose two answers)
- A. ZTNA tags
- B. SSL VPN profile
- C. FortiSASE CA certificate
- D. Real-time protection
Question #54
Which FortiSASE component secures internet access for remote users who have configured FortiSASE as an explicit web proxy? (Choose one answer)
- A. secure web gateway (SWG)
- B. zero trust network access (ZTNA)
- C. Firewall-as-a-Service (FWaaS)
- D. SD-WAN
Question #55
An administrator wants to configure dead peer detection (DPD) on IPsec VPN for detecting dead tunnels. The requirement is that FortiGate sends DPD probes only when there is outbound traffic but no response from the peer.
Which DPD mode on FortiGate meets this requirement?
(Choose one answer)
- A. On Demand
- B. On Idle
- C. Disabled
- D. Enabled
Question #56
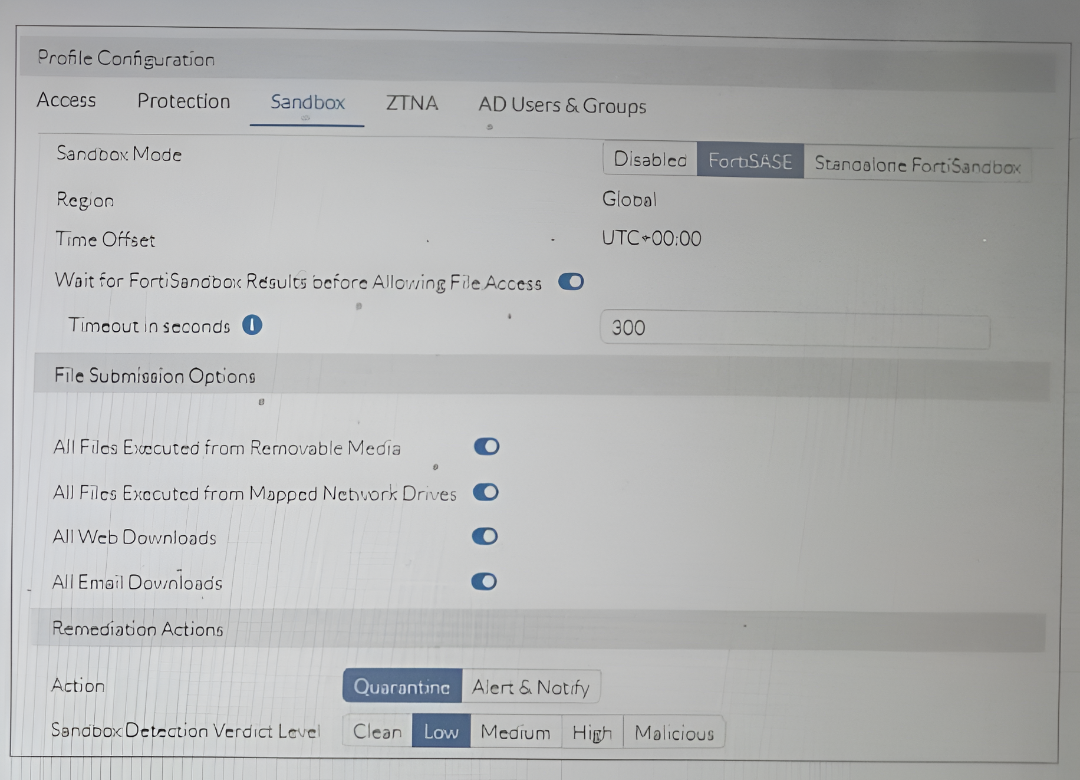
Refer to the exhibit.
Based on the configuration shown, in which two ways will FortiSASE process sessions that require FortiSandbox inspection?
(Choose two answers)
- A. All files detected on a USB drive will be sent to FortiSandbox for analysis.
- B. All infected files that FortiSandbox detects as malicious will be quarantined.
- C. Only endpoints assigned with profile for Sandbox Detection will be processed by the sandbox feature.
- D. All infected files will be sent to an on-premises FortiSandbox for inspection.
Question #57
Which FortiSASE feature ensures least-privileged user access to corporate applications that are protected by an on-premises FortiGate? (Choose one answer)
- A. role-based access control (RBAC)
- B. Privileged access management (PAM)
- C. Identity & access management (IAM)
- D. zero trust network access (ZTNA)
Question #58
Which technology is used with IPsec for spoke-to-spoke connectivity in a Secure Private Access (SPA) with SD-WAN deployment? (Choose one answer)
- A. EVPN
- B. ADVPN
- C. EBGP
- D. VTEP
Question #59
In the Secure Private Access (SPA) use case, which two FortiSASE features facilitate access to corporate applications? (Choose two answers)
- A. Thin edge
- B. Cloud access security broker (CASB)
- C. SD-WAN
- D. Zero trust network access (ZTNA)
Question #60
What access point communication protocol does FortiAP use to communicate with FortiSASE in a micro branch deployment? (Choose one answer)
- A. Control and Provisioning of Wireless Access Points (CAPWAP)
- B. Inter-Access Point Protocol (IAPP)
- C. Lightweight Access Point Protocol (LWAPP)
- D. Wireless Application Protocol (WAP)
When you configure FortiSASE Secure Private Access (SPA) with SD-WAN integration, you must establish a routing adjacency between FortiSASE and the FortiGate SD-WAN hub.
Which routing protocol must you use? (Choose one answer)