● FCP - FortiGate 7.4 Administrator Exam Materials
Please note that the exam "FCP - FortiGate 7.4 Administrator Exam " is no longer offered by Fortinet and is not available for booking through Pearson VUE, so we opened it on free view,
It has been replaced by the exam "NSE 4 - FortiOS 7.6 Exam"
The new exam version is available on Brave-Dumps and can be purchased.
It has been replaced by the exam "NSE 4 - FortiOS 7.6 Exam"
The new exam version is available on Brave-Dumps and can be purchased.
Question #11

Question #12
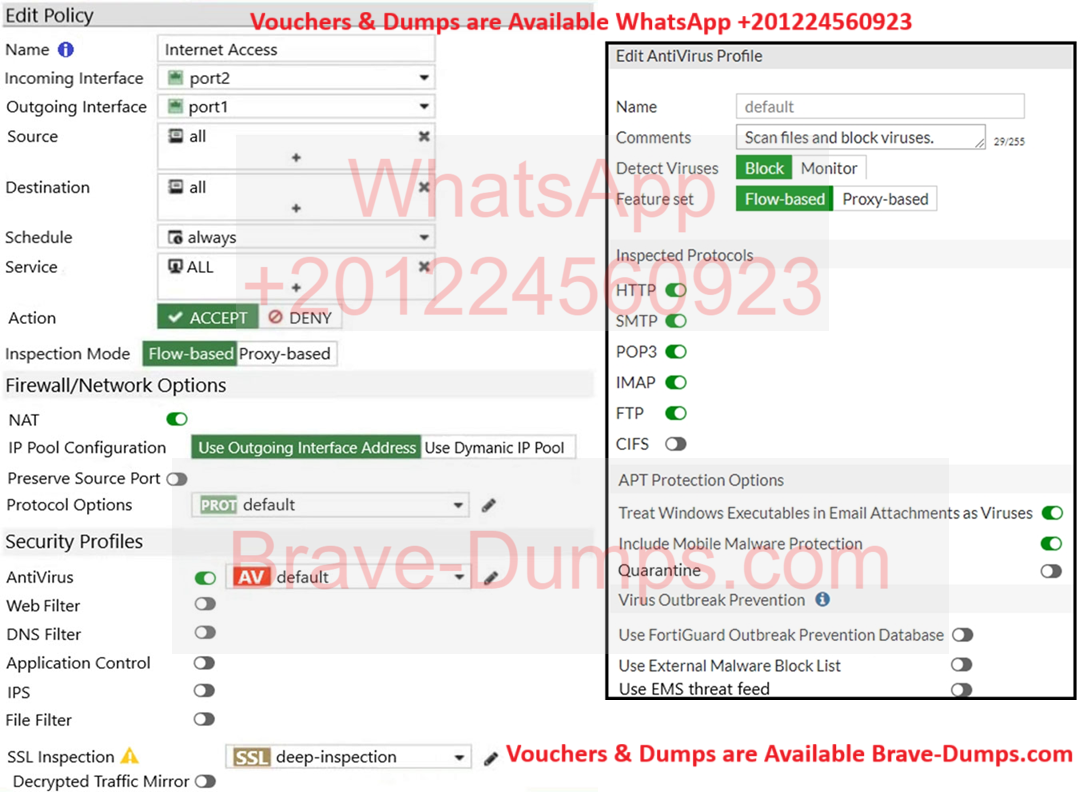
Refer to the exhibits to view the firewall policy (Exhibit A) and the antivirus profile (Exhibit B).
Why is the user unable to receive a block replacement message when downloading an infected file for the first time?
(Choose one answer)
- A. A. The intrusion prevention security profile must be enabled when using flow-based inspection mode.
- B. The option to send files to FortiSandbox for inspection is enabled
- C. The firewall policy performs a full content inspection on the file
- D. Flow-based inspection is used, which resets the last packet to the user
Question #13
Which two statements are true regarding FortiGate HA configuration synchronization? (Choose two answers)
- A. Checksums of devices are compared against each other to ensure configurations are the same.
- B. Checksums of devices will be different from each other because some configuration items are not synced to other HA members.
- C. Incremental configuration synchronization can occur only from changes made on the primary FortiGate device.
- D. Incremental configuration synchronization can occur from changes made on any FortiGate device within the HA cluster.
Question #14
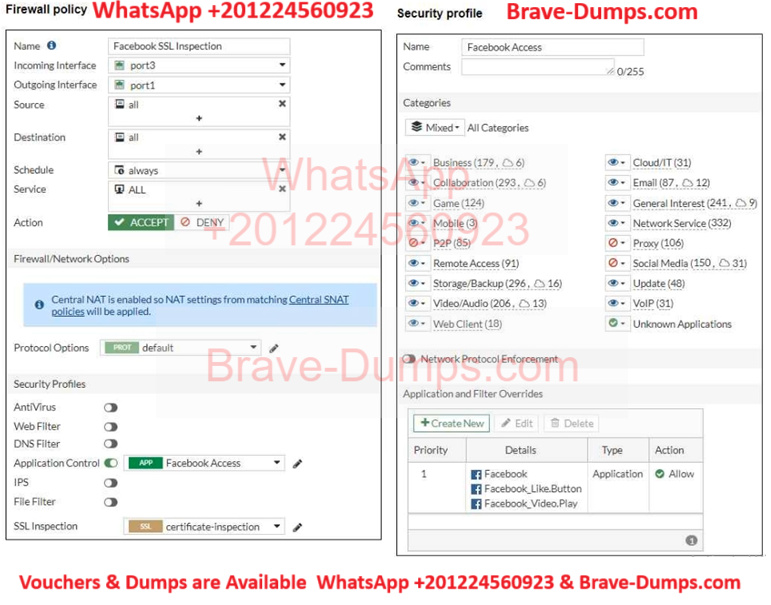
Refer to the exhibits,
which show the firewall policy and the security profile for Facebook.
Users are given access to the Facebook web application. They can play video content hosted on Facebook, but they are unable to leave reactions on videos or other types of posts.
Which part of the configuration must you change to resolve the issue?
(Choose one answer)
- A. Disable HTTP redirect to HTTPS on the web browser
- B. Make the SSL inspection a deep content inspection
- C. Add Facebook to the URL category in the security policy
- D. Get the additional application signatures required to add to the security policy
Question #15
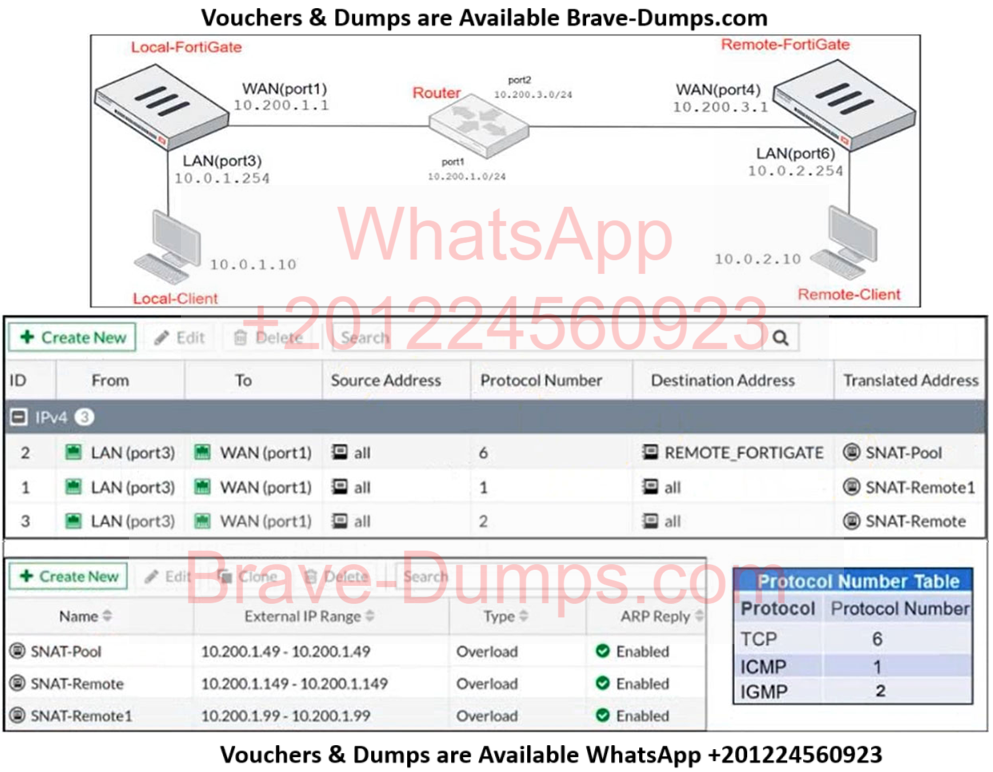
Refer to the exhibits.
The exhibits contain a network diagram, central SNAT policy, and IP pool configuration.
The WAN (port1) interface has the IP address 10.200.1.1/24.
The LAN (port3) interface has the IP address 10.0.1.254/24.
A firewall policy is configured to allow all destinations from LAN (port3) to WAN (port1).
Central NAT is enabled, so NAT settings from matching Central SNAT policies will be applied.
Which IP address will be used to source NAT the traffic, if the user on Local-Client (10.0.1.10) pings the IP address of Remote-FortiGate (10.200.3.1)?
(Choose one answer)
- A. 10.200.1.1
- B. 10.200.1.149
- C. 10.200.1.99
- D. 10.200.1.49
Question #16
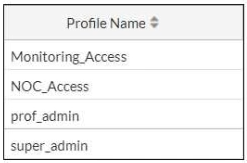
Refer to the exhibit.
The NOC team connects to the FortiGate GUI with the NOC_Access admin profile. They request that their GUI sessions do not disconnect too early during inactivity.
What must the administrator configure to answer this specific request from the NOC team?
(Choose one answer)
- A. Enable the parameter Never Timeout in the admin profiles
- B. Increase the admintimeout value under config system accprofile super_admin
- C. Increase the admintimeout value under config system global
- D. Increase the offline value of the Override idle Timeout parameter in the NOC_Access admin profile
Question #17
What are three key routing principles in SD-WAN? (Choose three answers)
- A. Regular policy routes have precedence over SD-WAN rules.
- B. By default, SD-WAN rules are skipped if the best route to the destination is not an SD-WAN member.
- C. By default, SD-WAN rules are skipped if only one route to the destination is available.
- D. By default, SD-WAN members are skipped if they do not have a valid route to the destination.
- E. SD-WAN rules have precedence over any other type of routes.
Question #18
A FortiGate administrator is required to reduce the attack surface on the SSL VPN portal.
Which SSL timer can you use to mitigate a denial of service (DoS) attack?
(Choose one answer)
- A. SSL VPN dtls-hello-timeout
- B. SSL VPN http-request-header-timeout
- C. SSL VPN idle-timeout
- D. SSL VPN login-timeout
Question #19
Which three statements about SD-WAN zones are true? (Choose three answers)
- A. You can define up to three SD-WAN zones per FortiGate device.
- B. An SD-WAN zone is a logical grouping of members.
- C. An SD-WAN zone can contain physical and logical interfaces.
- D. An SD-WAN zone must contains at least two members.
- E. You can use an SD-WAN zone in static route definitions.
Question #20
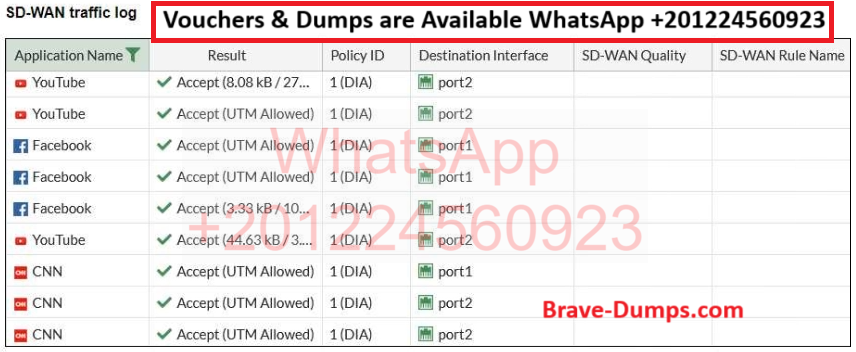
Refer to the exhibit.
The administrator configured SD-WAN rules and set the FortiGate traffic log page to display SD-WAN-specific columns: SD-WAN Quality and SD-WAN Rule Name.
FortiGate allows the traffic according to policy ID 1. This is the policy that allows SD-WAN traffic.
Despite these settings the traffic logs do not show the name of the SD-WAN rule used to steer those traffic flows.
What can be the reason?
(Choose one answer)
- A. FortiGate load balanced the traffic according to the implicit SD-WAN rule
- B. There is no application control profile applied to the firewall policy
- C. Destination in the SD-WAN rules are configured per application but the feature visibility is not enabled.
- D. SD-WAN rule names do not appear immediately. The administrator needs to refresh the page
Refer to the exhibit.
Which statement about this firewall policy list is true? (Choose one answer)