● FCSS - Enterprise Firewall 7.4 Administrator Exam Materials
Please note that the exam "FCSS - Enterprise Firewall 7.4 Administrator Exam" is no longer offered by Fortinet and is not available for booking through Pearson VUE, so we opened it on free view,
It has been replaced by the exam "NSE 7 - Enterprise Firewall 7.6 Administrator"
The new exam version is available on Brave-Dumps and can be purchased.
It has been replaced by the exam "NSE 7 - Enterprise Firewall 7.6 Administrator"
The new exam version is available on Brave-Dumps and can be purchased.
Question #31
Question #32

Refer to the exhibit, which shows a LAN interface connected from FortiGate to two FortiSwitch devices.
What two conclusions can you draw from the corresponding LAN interface?
(Choose two answers)
- A. You must enable STP or RSTP on FortiGate and FortiSwitch to avoid layer 2 loopbacks.
- B. The LAN interface must use a 802.3ad type interface.
- C. This connection is using a FortiLInk to manage VLANs on FortiGate.
- D. FortiGate is using an SD-WAN-type interface to connect to a FortiSwitch device with MCLAG.
Question #33
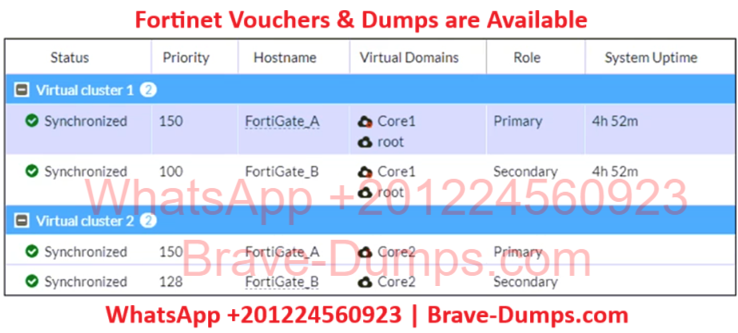
Refer to the exhibit, which shows the HA status of an active-passive cluster.
An administrator wants FortiGate_B to handle the Core2 VDOM traffic.
Which modification must the administrator apply to achieve this?
(Choose one answer)
- A. The administrator must disable override on FortiGate_A.
- B. The administrator must change the priority from 100 to 160 for FortiGate_B.
- C. The administrator must change the load balancing method on FortiGate_B.
- D. The administrator must change the priority from 128 to 200 for FortiGate_B.
Question #34
During the maintenance window, an administrator must sniff all the traffic going through a specific firewall policy, which is handled by NP6 interfaces. The output of the sniffer trace provides just a few packets.
Why is the output of sniffer trace limited?
(Choose one answer)
- A. The traffic corresponding to the firewall policy is encrypted.
- B. auto-asic-off load is set to enable in the firewall policy,
- C. inspection-mode is set to proxy in the firewall policy.
- D. The option npudbg is not added in the diagnose sniff packet command.
Question #35
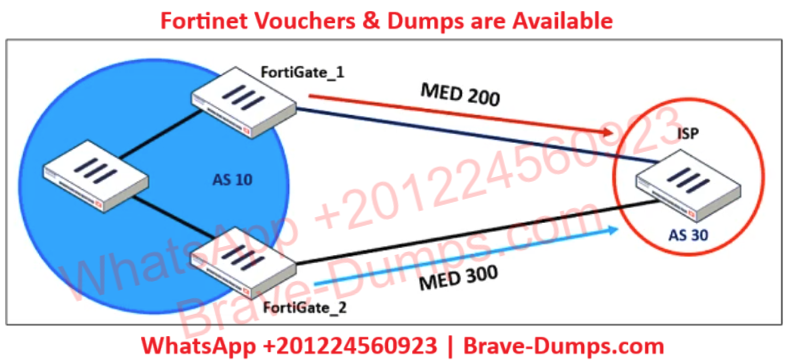
Refer to the exhibit, which shows a network diagram.
An administrator would like to modify the MED value advertised from FortiGate_1 to a BGP neighbor in the autonomous system 30.
What must the administrator configure on FortiGate_1 to implement this?
(Choose one answer)
- A. route-map-out
- B. network-import-check
- C. prefix-list-out
- D. distribute-list-out
Question #36
An administrator received a FortiAnalyzer alert that a 1 ТВ disk filled up in a day. Upon investigation, they found thousands of unusual DNS log requests, such as JHCMQK.website.com, with no answers. They later discovered that DNS exfiltration was occurring through both UDP and TLS.
How can the administrator prevent this data theft technique?
(Choose one answer)
- A. Create an inline-CASB to protect against DNS exfiltration.
- B. Configure a File Filter profile to prevent DNS exfiltration.
- C. Enable DNS Filter to protect against DNS exfiltration.
- D. Use an IPS profile and DNS exfiltration-related signatures.
Question #37
An administrator configured the FortiGate devices in an enterprise network to join the Fortinet Security Fabric.
The administrator has a list of IP addresses that must be blocked by the data center firewall. This list is updated daily.
How can the administrator automate a firewall policy with the daily updated list?
(Choose one answer)
- A. With FortiNAC
- B. With FortiAnalyzer
- C. With a Security Fabric automation
- D. With an external connector from Threat Feeds
Question #38
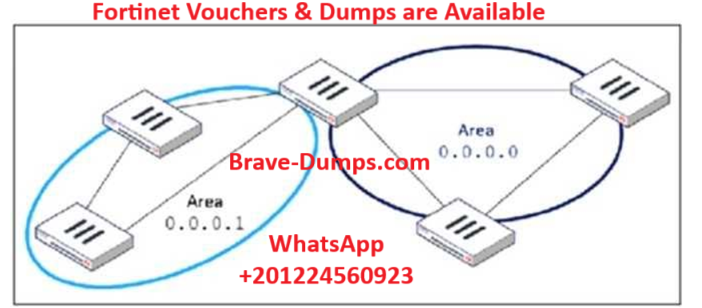
Refer to the exhibit, which shows an OSPF network.
Which configuration must the administrator apply to optimize the OSPF database?
(Choose one answer)
- A. Set a route map in the AS boundary FortiGate.
- B. Set the area 0.0.0.1 to the type STUB in the area border FortiGate.
- C. Set an access list in the AS boundary FortiGate.
- D. Set the area 0.0.0.1 to the type NSSA in the area border FortiGate.
Question #39
The IT department discovered during the last network migration that all zero phase selectors in phase 2 IPsec configurations impacted network operations.
What are two valid approaches to prevent this during future migrations?
(Choose two answers)
- A. Use routing protocols to specify allowed subnets over the tunnel.
- B. Configure an IPsec-aggregate to create redundancy between each firewall peer.
- C. Clearly indicate to the VPN which segments will be encrypted in the phase two selectors.
- D. Configure an IP address on the IPsec interface of each firewall to establish unique peer connections and avoid impacting network operations.
Question #40
How will configuring set tcp-mss-sender and set tcp-mss-receiver in a firewall policy affect the size and handling of TCP packets in the network? (Choose one answer)
- A. The maximum segment size permitted in the firewall policy determines whether TCP packets are allowed or denied.
- B. Applying commands in a firewall policy determines the largest payload a device can handle in a single TCP segment.
- C. The administrator must consider the payload size of the packet and the size of the IP header to configure a correct value in the firewall policy.
- D. The TCP packet modifies the packet size only if the size of the packet is less than the one the administrator configured in the firewall policy.
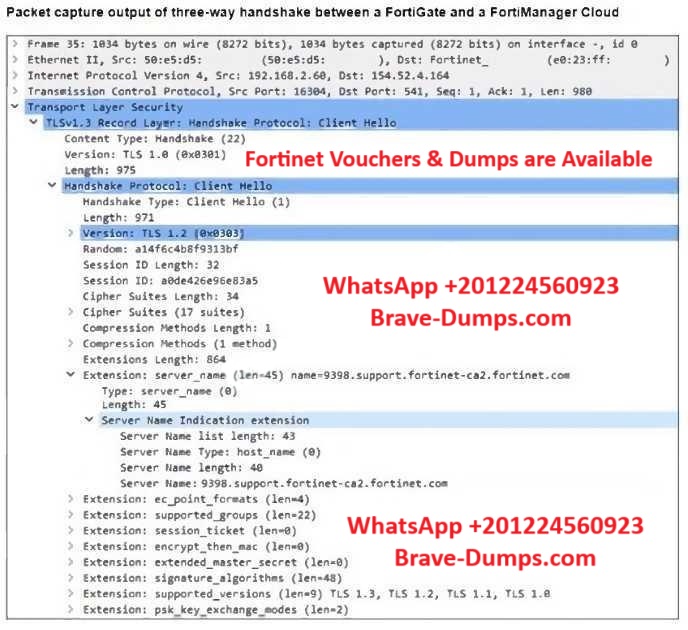
Refer to the exhibit, which shows the packet capture output of a three-way handshake between FortiGate and FortiManager Cloud.
What two conclusions can you draw from the exhibit? (Choose two answers)