● FCSS - Enterprise Firewall 7.4 Administrator Exam Materials
Please note that the exam "FCSS - Enterprise Firewall 7.4 Administrator Exam" is no longer offered by Fortinet and is not available for booking through Pearson VUE, so we opened it on free view,
It has been replaced by the exam "NSE 7 - Enterprise Firewall 7.6 Administrator"
The new exam version is available on Brave-Dumps and can be purchased.
It has been replaced by the exam "NSE 7 - Enterprise Firewall 7.6 Administrator"
The new exam version is available on Brave-Dumps and can be purchased.
Question #41
Question #42
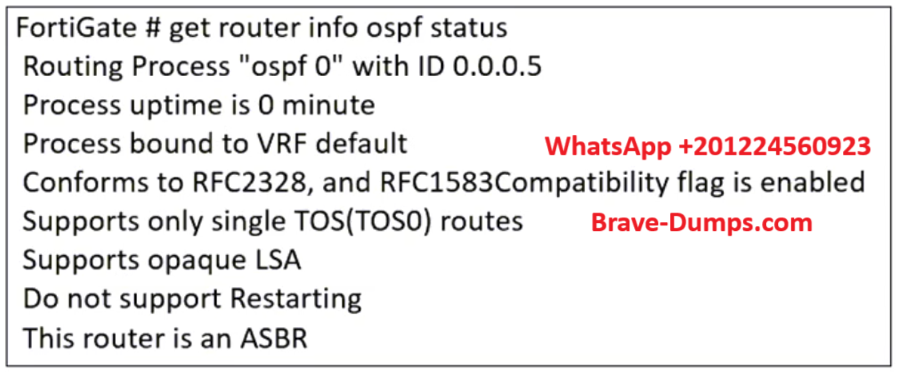
Refer to the exhibit, which contains the partial output of an OSPF command.
An administrator is checking the OSPF status of a FortiGate device and receives the output shown in the exhibit.
Which statement on this FortiGate device is correct?
(Choose one answer)
- A. The FortiGate device can inject external routing information.
- B. The FortiGate device is in the area 0.0.0.5.
- C. The FortiGate device does not support OSPF ECMP.
- D. The FortiGate device is a backup designated router.
Question #43
An administrator is setting up an ADVPN configuration and wants to ensure that peer IDs are not exposed during VPN establishment.
Which protocol can the administrator use to enhance security?
(Choose one answer)
- A. Use IKEv2, which encrypts peer IDs and prevents exposure.
- B. Opt for SSL VPN web mode because it does not use peer IDs at all.
- C. Choose IKEv1 aggressive mode because it simplifies peer identification.
- D. Stick with IKEv1 main mode because it offers better performance.
Question #44
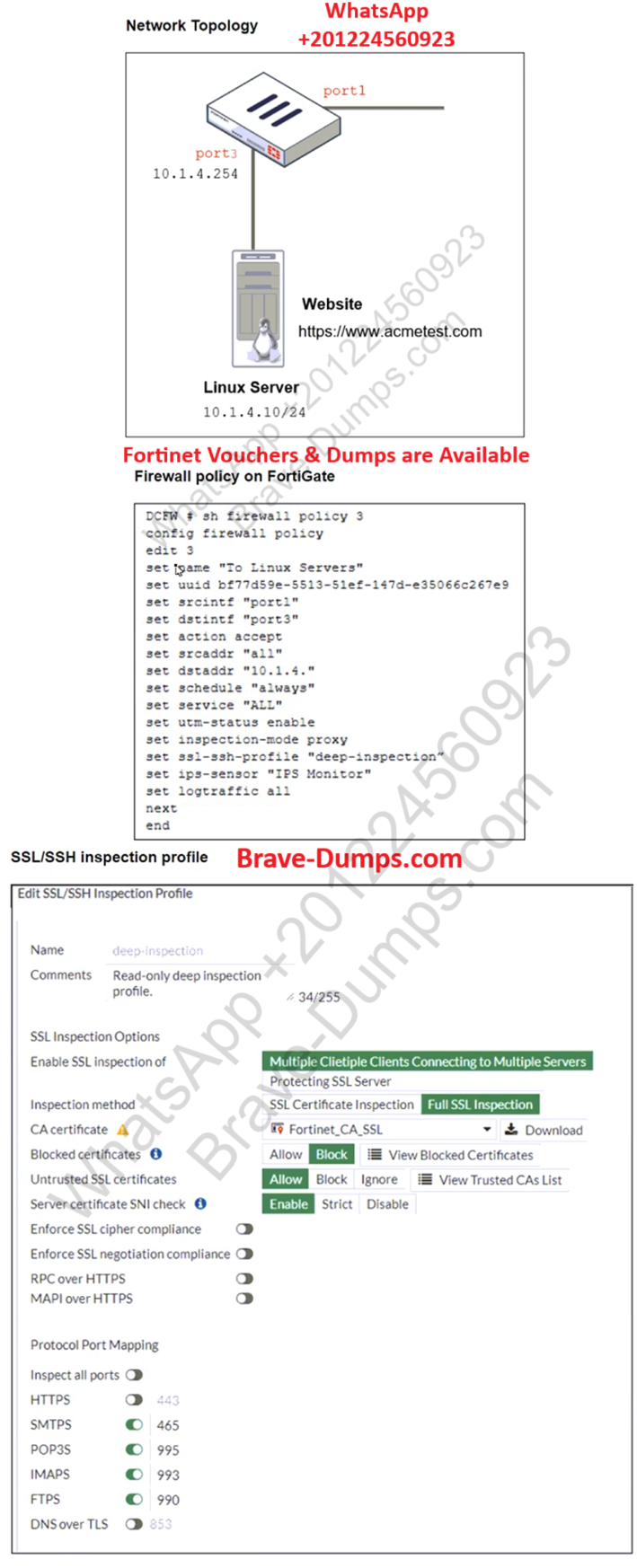
Refer to the exhibits. The exhibits show a network topology, a firewall policy, and an SSL/SSH inspection profile configuration.
Why is FortiGate unable to detect HTTPS attacks on firewall policy ID 3 targeting the Linux server?
(Choose one answer)
- A. The administrator must set the policy to inspection mode to analyze the HTTPS packets as expected.
- B. The administrator must enable HTTPS in the protocol port mapping of the deep- inspection SSL/SSH inspection profile.
- C. The administrator must enable SSL inspection of the SSL server and upload the certificate of the Linux server website to the SSL/SSH inspection profile.
- D. The administrator must enable cipher suites in the SSL/SSH inspection profile to decrypt the message.
Question #45
An administrator must minimize CPU and RAM use on a FortiGate firewall while also enabling essential security features, such as web filtering and application control for HTTPS traffic.
Which SSL inspection setting helps reduce system load while also enabling security features, such as web filtering and application control for encrypted HTTPS traffic?
(Choose one answer)
- A. Use full SSL inspection to thoroughly inspect encrypted payloads.
- B. Disable SSL inspection entirely to conserve resources.
- C. Configure SSL inspection to handle HTTPS traffic efficiently.
- D. Enable SSL certificate inspection mode to perform basic checks without decrypting traffic.
Question #46
An administrator must standardize the deployment of FortiGate devices across branches with consistent interface roles and policy packages using FortiManager.
What is the recommended best practice for interface assignment in this scenario?
(Choose one answer)
- A. Enable metadata variables to use dynamic configurations in the standard interfaces of FortiManager.
- B. Use the Install On feature in the policy package to automatically assign different interfaces based on the branch.
- C. Create interfaces using device database scripts to use them on the same policy package of FortiGate devices.
- D. Create normalized interface types per-platform to automatically recognize device layer interfaces based on the FortiGate model and interface name.
Question #47
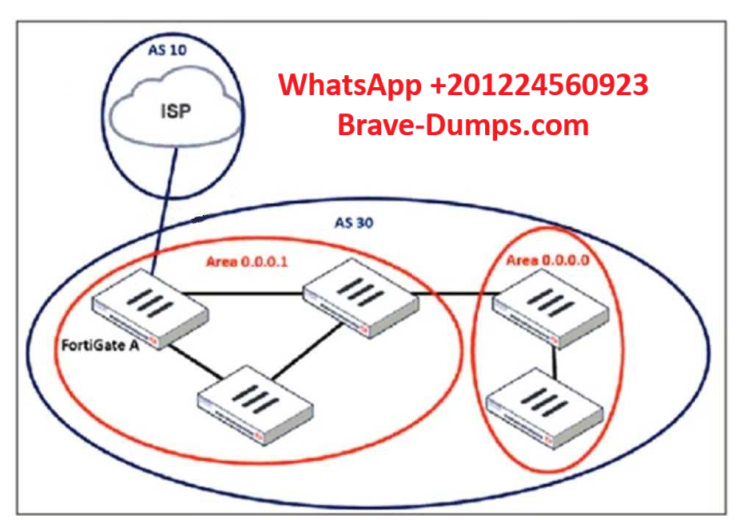
Refer to the exhibit, which shows an enterprise network connected to an internet service provider.
An administrator must configure a loopback as a BGP source to connect to the ISP.
Which two commands are required to establish the connection?
(Choose two answers)
- A. ebgp-enforce-multihop
- B. update-source
- C. ibgp-enforce-multihop
- D. recursive-next-hop
Question #48
What action can be taken on a FortiGate to block traffic using IPS protocol decoders, focusing on network transmission patterns and application signatures? (Choose one answer)
- A. Use the DNS filter to block application signatures and protocol decoders.
- B. Use application control to limit non-URL-based software handling.
- C. Enable application detection-based SD-WAN rules.
- D. Configure a web filter profile in flow mode.
Question #49
An administrator is designing an ADVPN network for a large enterprise with spokes that have varying numbers of internet links. They want to avoid a high number of routes and peer connections at the hub.
Which method should be used to simplify routing and peer management?
(Choose one answer)
- A. Deploy a full-mesh VPN topology to eliminate hub dependency.
- B. Implement static routing over IPsec interfaces for each spoke.
- C. Use a dynamic routing protocol using loopback interfaces to streamline peers and routes.
- D. Establish a traditional hub-and-spoke VPN topology with policy routes.
Question #50

Refer to the exhibit, which shows the ADVPN IPsec interface representing the VPN IPsec phase 1 from Hub A to Spoke 1 and Spoke 2, and from Hub B to Spoke 3 and Spoke 4.
An administrator must configure an ADVPN using IBGP and EBGP to connect overlay network 1 with2.
What must the administrator configure in the phase 1 VPN IPsec configuration of the ADVPN tunnels?
(Choose one answer)
- A. set auto-discovery-sender enable and set network-id x
- B. set auto-discovery-forwarder enable and set remote-as x
- C. set auto-discovery-crossover enable and set enforce-multihop enable
- D. set auto-discovery-receiver enable and set npu-offload enable
A vulnerability scan report has revealed that a user has generated traffic to the website example.com (10.10.10.10) using a weak SSL/TLS version supported by the HTTPS web server.
What can the firewall administrator do to block all outdated SSL/TLS versions on any HTTPS web server to prevent possible attacks on user traffic? (Choose one answer)