● NSE 6 - OT Security 7.2 Architect Exam Materials
Please note that the exam "NSE 6 - OT Security 7.2 Architect" is no longer offered by Fortinet and is not available for booking through Pearson VUE, so we opened it on free view,
It has been replaced by the exam "NSE 6 - OT Security 7.6 Architect"
The new exam version is available on Brave-Dumps and can be purchased.
It has been replaced by the exam "NSE 6 - OT Security 7.6 Architect"
The new exam version is available on Brave-Dumps and can be purchased.
Question #11
Question #12
As an OT network administrator, you are managing three FortiGate devices that each protect different levels on the Purdue model. To increase traffic visibility, you are required to implement additional security measures to detect exploits that affect PLCs.
Which security sensor must implement to detect these types of industrial exploits?
(Choose one answer)
- A. Intrusion prevention system (IPS)
- B. Deep packet inspection (DPI)
- C. Antivirus inspection
- D. Application control
Question #13
The HR and SALES endpoints are on the same VLAN. They are not able to ping each other. What configuration must you change to allow ping traffic? (Choose one answer)
- A. Enable ICMP snoofing on the interface
- B. Proxy ARP should be configured on FortiGate.
- C. Client to Client traffic is allowed only at layer 2
- D. Enable NAT on the firewall policy
Question #14
An OT network administrator is trying to implement active authentication.
Which two methods should the administrator use to achieve this?
(Choose two answers)
- A. Two-factor authentication on FortiAuthenticator
- B. Role-based authentication on FortiNAC
- C. FSSO authentication on FortiGate
- D. Local authentication on FortiGate
Question #15
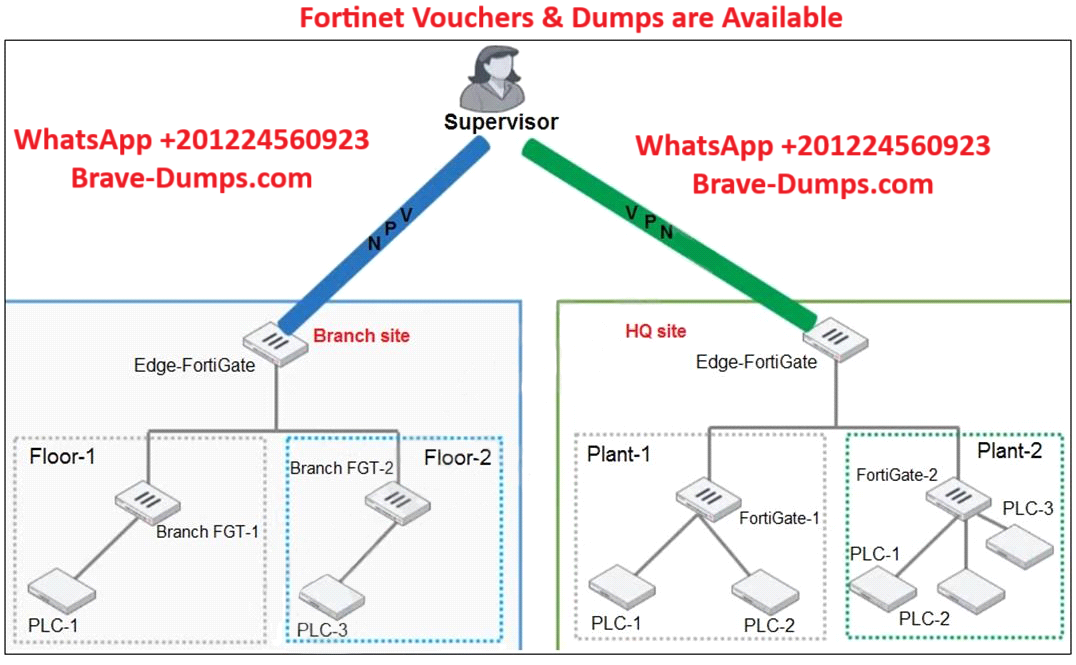
You need to configure VPN user access for supervisors at the breach and HQ sites using the same soft FortiToken. Each site has a FortiGate VPN gateway.
What must you do to achieve this objective?
(Choose one answer)
- A. You must use a FortiAuthenticator
- B. You must register the same FortiToken on more than one FortiGate.
- C. You must use the user self-registration server.
- D. You must use a third-party RADIUS OTP server
Question #16
An OT administrator is defining an incident notification policy using FortiSIEM and would like to configure the system with a notification policy. If an incident occurs, the administrator would like to be able to intervene and block an IP address or disable a user in Active Directory from FortiSIEM.
Which step must the administrator take to achieve this task?
(Choose one answer)
- A. Configure a fabric connector with a notification policy on FortiSIEM to connect with FortiGate.
- B. Create a notification policy and define a script/remediation on FortiSIEM.
- C. Define a script/remediation on FortiManager and enable a notification rule on FortiSIEM.
- D. Deploy a mitigation script on Active Directory and create a notification policy on FortiSIEM.
Question #17
Which type of attack posed by skilled and malicious users of security level 4 (SL 4) of IEC 62443 is designed to defend against intentional attacks? (Choose one answer)
- A. Users with substantial resources
- B. Users with unintentional operator error
- C. Users with low access to resources
- D. Users with access to moderate resources
Question #18
An OT administrator configured and ran a default application risk and control report in FortiAnalyzer to learn more about the key application crossing the network.
However, the report output is empty despite the fact that some related real-time and historical logs are visible in the FortiAnalyzer.
What are two possible reasons why the report output was empty?
(Choose two answers)
- A. The administrator selected the wrong logs to be indexed in FortiAnalyzer.
- B. The administrator selected the wrong time period for the report.
- C. The administrator selected the wrong devices in the Devices section.
- D. The administrator selected the wrong hcache table for the report.
Question #19
What triggers Layer 2 polling of infrastructure devices connected in the network? (Choose one answer)
- A. A failed Layer 3 poll
- B. A matched security policy
- C. A matched profiling rule
- D. A linkup or linkdown trap
Question #20
Which statement is correct about processing matched rogue devices by FortiNAC? (Choose one answer)
- A. FortiNAC matches the rogue device with only one device profiling rule.
- B. FortiNAC remembers the matching rule of the rogue device.
- C. FortiNAC disables matching rule of previously-profiled rogue devices.
- D. FortiNAC cannot revalidate matched devices.
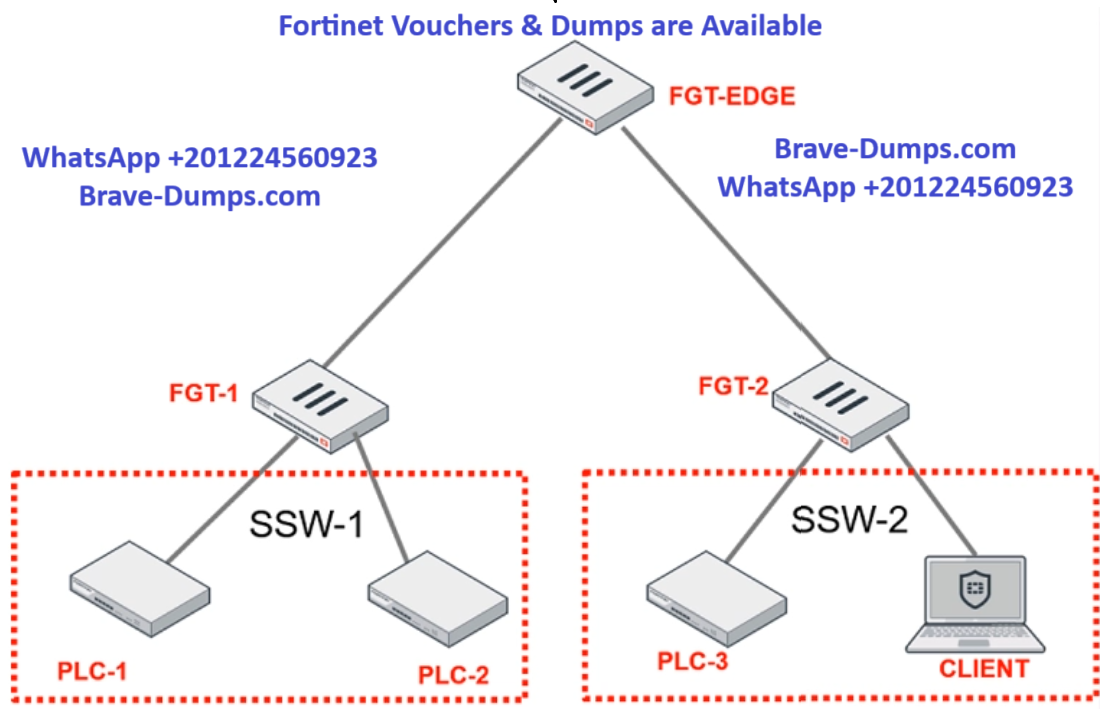
Refer to the exhibit.
PLC-3 and CLIENT can send traffic to PLC-1 and PLC-2. FGT-2 has only one software switch (SSW-1) connecting both PLC-3 and CLIENT. PLC-3 and CLIENT cannot send traffic to each other.
Which two statements about the traffic between PCL-1 and PLC-2 are true? (Choose two answers)