● NSE 6 - OT Security 7.2 Architect Exam Materials
Please note that the exam "NSE 6 - OT Security 7.2 Architect" is no longer offered by Fortinet and is not available for booking through Pearson VUE, so we opened it on free view,
It has been replaced by the exam "NSE 6 - OT Security 7.6 Architect"
The new exam version is available on Brave-Dumps and can be purchased.
It has been replaced by the exam "NSE 6 - OT Security 7.6 Architect"
The new exam version is available on Brave-Dumps and can be purchased.
Question #21
Question #22
You are investigating a series of incidents that occurred in the OT network over past 24 hours in FortiSIEM.
Which three FortiSIEM options can you use to investigate these incidents?
(Choose three answers)
- A. Security
- B. IPS
- C. List
- D. Risk
- E. Overview
Question #23
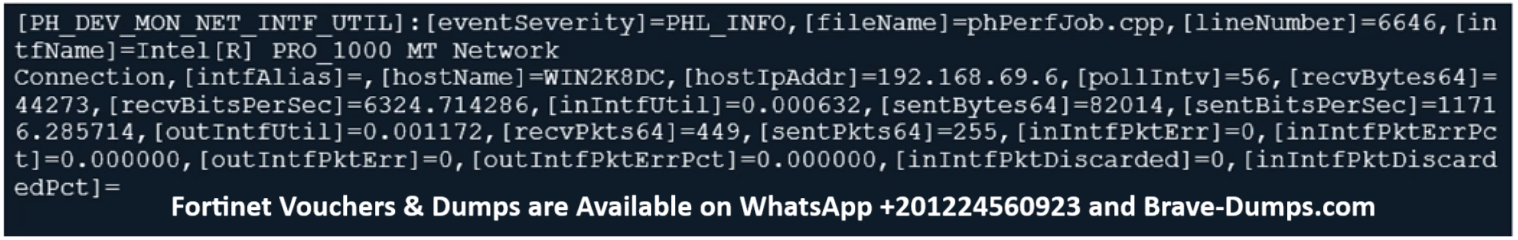
Refer to the exhibit.
From your analysis of the output, which statement about the output is true?
(Choose one answer)
- A. This is a sample of an SNMP temperature control event log.
- B. This is a sample of a FortiAnalyzer system interface event log.
- C. This is a sample of a PAM event type.
- D. This is a sample of FortiGate interface statistics.
Question #24
How can you achieve remote access and internet availability in an OT network? (Choose one answer)
- A. Add additional internal firewalls to access OT devices.
- B. Implement SD-WAN to manage traffic on each ISP link.
- C. Create more access policies to prevent unauthorized access.
- D. Create a back-end backup network as a redundancy measure.
Question #25
With the limit of using one firewall device, the administrator enables multi-VDOM on FortiGate to provide independent multiple security domains to each ICS network.
Which statement ensures security protection is in place for all ICS networks?
(Choose one answer)
- A. Each traffic VDOM must have a direct connection to FortiGuard services to receive the required security updates.
- B. The management VDOM must have access to all global security services.
- C. Each VDOM must have an independent security license.
- D. Traffic between VDOMs must pass through the physical interfaces of FortiGate to check for security incidents.
Question #26
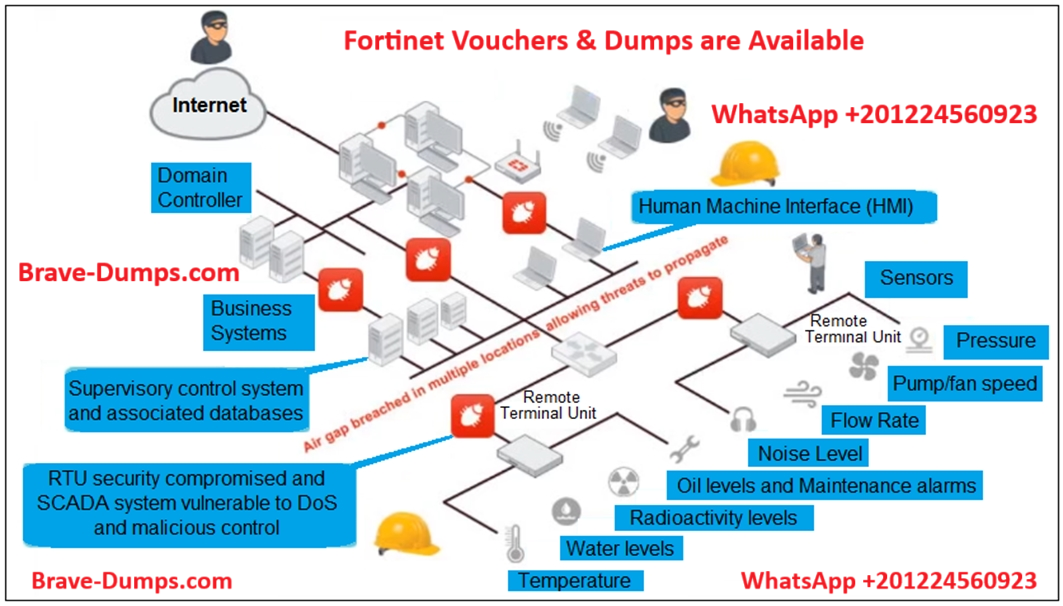
Refer to the exhibit, which shows a non-protected OT environment.
An administrator needs to implement proper protection on the OT network.
Which three steps should an administrator take to protect the OT network?
(Choose three answers)
- A. Deploy an edge FortiGate between the internet and an OT network as a one-arm sniffer.
- B. Deploy a FortiGate device within each ICS network.
- C. Configure firewall policies with web filter to protect the different ICS networks.
- D. Configure firewall policies with industrial protocol sensors
- E. Use segmentation
Question #27
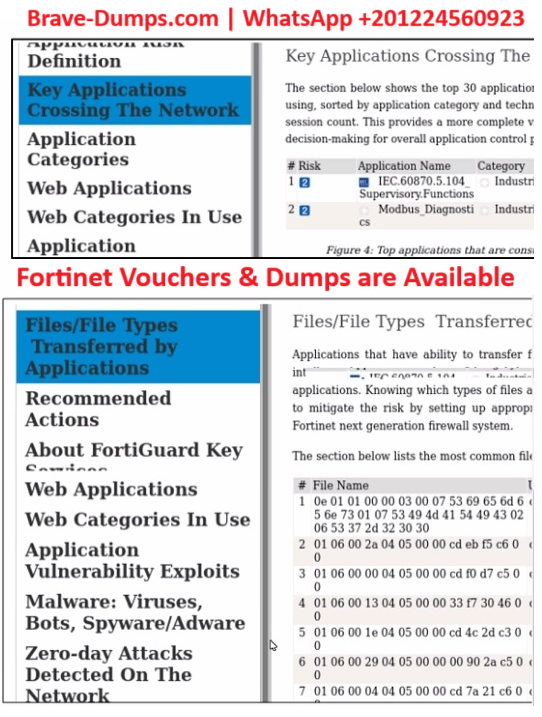
Refer to the exhibits.
Which statement about some of the generated report elements from FortiAnalyzer is true?
(Choose one answer)
- A. The file types confirm the infected applications on the PLCs.
- B. FortiGate collects the logs and generates the report to FortiAnalyzer.
- C. The report confirms Modbus and IEC 104 are the key applications crossing the network.
- D. This report is predefined and is not available for customization.
Question #28
The OT network analyst run different level of reports to quickly explore failures that could put the network at risk. Such reports can be about device performance.
Which FortiSIEM reporting method helps to identify device failures?
(Choose one answer)
- A. Business service reports
- B. Device inventory reports
- C. CMDB operational reports
- D. Active dependent rules reports
Question #29
Which type of attack posed by skilled and malicious users of security level 3 (SL 3) of IEC 62443 is designed to defend against intentional attacks? (Choose one answer)
- A. Unintentional operator error
- B. Access to moderate resources
- C. Low access to resources
- D. Substantial resources
Question #30
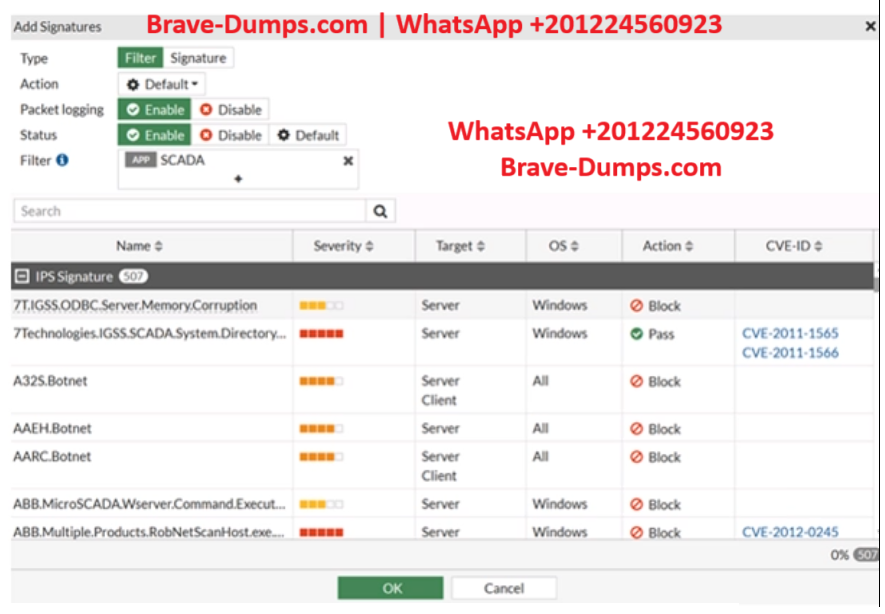
Refer to the exhibit.
The IPS profile is added on all of the security policies on FortiGate.
For an OT network, which statement of the IPS profile is true?
(Choose one answer)
- A. FortiGate has no IPS industrial signature database enabled.
- B. The listed IPS signatures are classified as SCADA applications.
- C. All IPS signatures are overridden and must block traffic match signature patterns.
- D. The IPS profile inspects only traffic originating from SCADA equipment.
A FortiGate device is newly deployed as the edge gateway of an OT network security fabric. The downstream FortiGate devices are also newly deployed as Security Fabric leafs to protect the control area zone.
With no additional essential networking devices, and to implement micro-segmentation on this OT network, what configuration must the OT network architect apply to control intra-VLAN traffic? (Choose one answer)