● NSE 6 - OT Security 7.2 Architect Exam Materials
Please note that the exam "NSE 6 - OT Security 7.2 Architect" is no longer offered by Fortinet and is not available for booking through Pearson VUE, so we opened it on free view,
It has been replaced by the exam "NSE 6 - OT Security 7.6 Architect"
The new exam version is available on Brave-Dumps and can be purchased.
It has been replaced by the exam "NSE 6 - OT Security 7.6 Architect"
The new exam version is available on Brave-Dumps and can be purchased.
Question #31

Question #32
An OT supervisor has configured LDAP and FSSO for authentication. The goal is that all users be authenticated against passive authentication first and, if passive authentication is not successful, then users should be challenged with active authentication.
What should the OT supervisor do to achieve this on FortiGate?
(Choose one answer)
- A. Under config user settings, configure set auth-on-demand implicit.
- B. Configure a firewall policy with LDAP users and place it at the top of the list of firewall policies.
- C. Configure a firewall policy with FSSO users and place it at the top of the list of firewall policies.
- D. Enable two-factor authentication with FSSO
Question #33
As an OT network administrator, you are required to generate reports that primarily use the same type of data sent to FortiSIEM. These reports are based on the preloaded analytic searches.
Which two actions can you take on FortiSIEM to enhance running reports for future use?
(Choose two answers)
- A. Automate running these reports upon receiving new logs.
- B. Create custom reports to process additional analytic searches.
- C. Export the preloaded analytics searches to an external syslog server.
- D. Save the analytic searches and turn them into report definitions.
Question #34
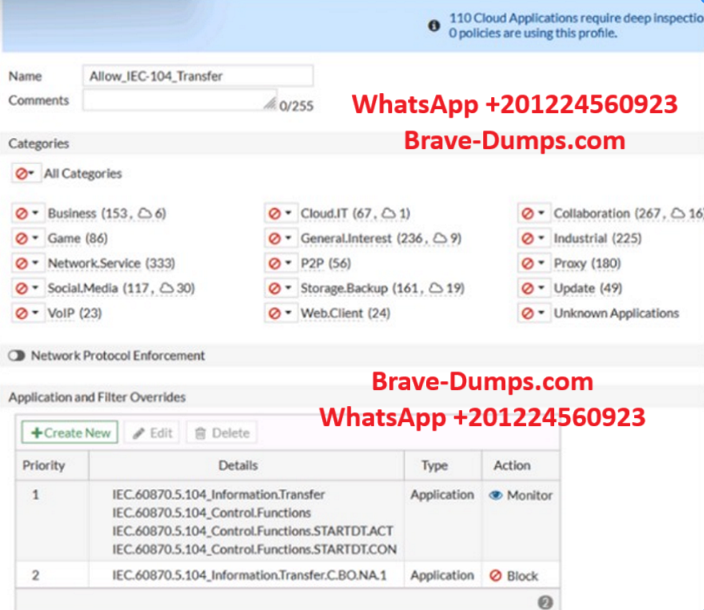
Refer to the exhibit.
An OT network security audit concluded that the application sensor requires changes to ensure the correct security action is committed against the overrides filters.
Which change must the OT network administrator make?
(Choose one answer)
- A. Set the priority of the C.BO.NA.1 signature override to 1.
- B. Remove IEC.60870.5.104_Information.Transfer from the first filter override.
- C. Change the security action of the industrial category to monitor.
- D. Set all application categories to apply default actions.
Question #35
Which statement about the IEC 104 protocol is true? (Choose one answer)
- A. IEC 104 is used for telecontrol SCADA in electrical engineering applications.
- B. IEC 104 is IEC 101 compliant in old SCADA systems.
- C. IEC 104 protects data transmission between OT devices and services.
- D. IEC 104 uses non-TCP/IP standards.
Question #36

Refer to the exhibit.
A new operational technology rule is being created to monitor Modbus protocol traffic on FortiSIEM.
Which action will ensure all Modbus messages on the network match the rule?
(Choose one answer)
- A. Remove attributes in the Group By section that are not configured in the Filter section.
- B. Add a new condition to filter Modbus traffic based on the Source TCP/UDP port.
- C. Set the Aggregate attribute value to equal to or greater than zero.
- D. This rule is valid and requires no additional changes.
Question #37
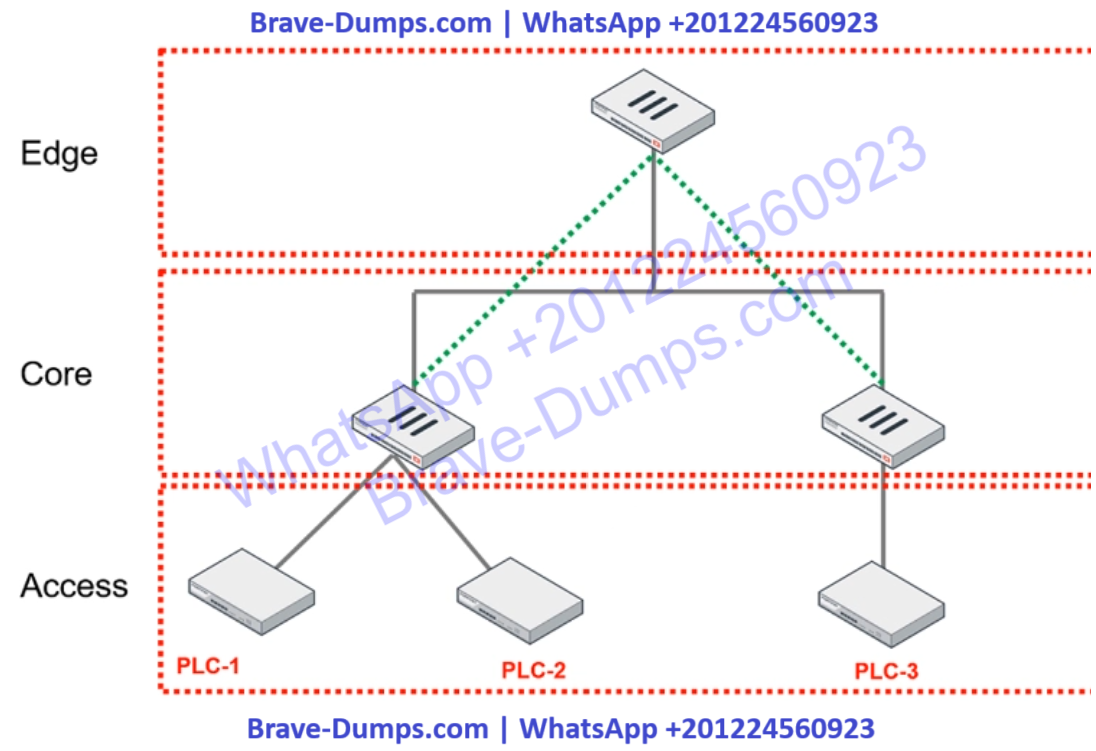
Refer to the exhibit.
You are assigned to implement a remote authentication server in the OT network.
Which part of the hierarchy should the authentication server be part of?
(Choose one answer)
- A. Edge
- B. Cloud
- C. Core
- D. Access
Question #38
An OT administrator deployed many devices to secure the OT network. However, the SOC team is reporting that there are too many alerts, and that many of the alerts are false positive. The OT administrator would like to find a solution that eliminates repetitive tasks, improves efficiency, saves time, and saves resources.
Which products should the administrator deploy to address these issues and automate most of the manual tasks done by the SOC team?
(Choose one answer)
- A. FortiSIEM and FortiManager
- B. FortiSandbox and FortiSIEM
- C. FortiSOAR and FortiSIEM
- D. A syslog server and FortiSIEM
Question #39
Which three Fortinet products can you use for device identification in an OT industrial control system (ICS)? (Choose three answers)
- A. FortiSIEM
- B. FortiManager
- C. FortiAnalyzer
- D. FortiGate
- E. FortiNAC
Question #40
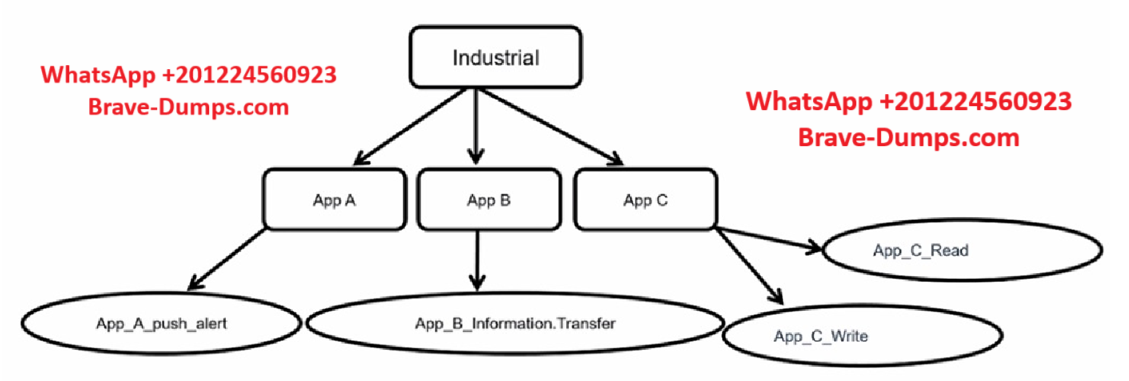
Refer to the exhibits.
Which statement is true about application control inspection?
(Choose one answer)
- A. The parent signature takes precedence over the child application signature.
- B. Security actions cannot be applied on the lowest level of the hierarchy.
- C. You can control security actions only on the parent-level application signature.
- D. The industrial application control inspection process is unique among application categories.
Refer to the exhibits.
Which statement is true about the traffic passing through to PLC-2? (Choose one answer)