● NSE 6 - OT Security 7.2 Architect Exam Materials
Please note that the exam "NSE 6 - OT Security 7.2 Architect" is no longer offered by Fortinet and is not available for booking through Pearson VUE, so we opened it on free view,
It has been replaced by the exam "NSE 6 - OT Security 7.6 Architect"
The new exam version is available on Brave-Dumps and can be purchased.
It has been replaced by the exam "NSE 6 - OT Security 7.6 Architect"
The new exam version is available on Brave-Dumps and can be purchased.
Question #41
Question #42
An OT administrator has configured FSSO and local firewall authentication. A user who is part of a user group is not prompted for credentials during authentication.
What is a possible reason?
(Choose one answer)
- A. Two-factor authentication is not configured with the RADIUS authentication method.
- B. The user was determined by the Security Fabric.
- C. FortiGate determined the user by passive authentication.
- D. FortiNAC determined the user by the DHCP fingerprint method.
Question #43
An OT architect has deployed a Layer 2 switch in the OT network at Level 1 in the Purdue model—process control. The purpose of the Layer 2 switch is to segment traffic between PLC1 and PLC2 with two VLANs.
All the traffic between PLC1 and PLC2 must first flow through the Layer 2 switch and then through the FortiGate device in the Level 2 supervisory control network.
Which statement about the traffic between PLC1 and PLC2 is true?
(Choose one answer)
- A. The Layer 2 switch rewrites VLAN tags before sending traffic to the FortiGate device.
- B. The Layer 2 switch routes any traffic to the FortiGate device through an Ethernet link.
- C. In order to communicate, PLC1 must be in the same VLAN as PLC2.
- D. PLC1 and PLC2 traffic must flow through the Layer 2 switch trunk link to the FortiGate device.
Question #44
FortiAnalyzer is implemented in the OT network to receive logs from responsible FortiGate devices. The logs must be processed by FortiAnalyzer.
In this scenario, which statement is correct about the purpose of FortiAnalyzer receiving and processing multiple log messages from a given PLC or RTU?
(Choose one answer)
- A. To isolate PLCs or RTUs in the event of external attacks
- B. To determine which type of messages from the PLC or RTU causes issues in the plant
- C. To help OT administrators configure the network and prevent breaches
- D. To configure event handlers and take further action on FortiGate
Question #45
What are two benefits of a Nozomi integration with FortiNAC? (Choose two answers)
- A. Importation and classification of hosts
- B. Enhanced point of connection details
- C. Adapter consolidation for multi-adapter hosts
- D. Direct VLAN assignment
Question #46
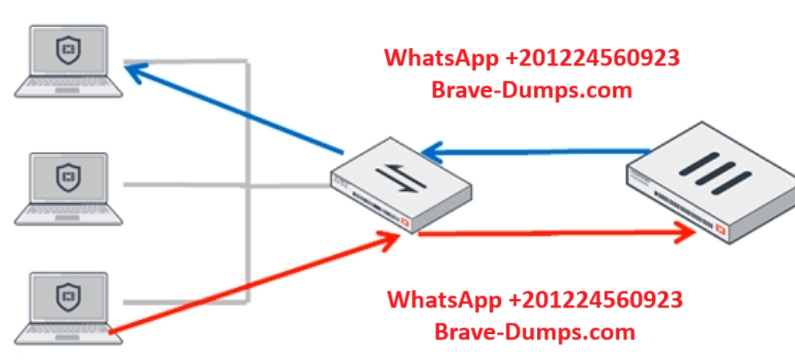
Refer to the exhibit.
In order for a FortiGate device to act as router on a stick, what configuration must an OT network architect implement on FortiGate to achieve inter-VLAN routing?
(Choose one answer)
- A. Set a unique forward domain on each interface on the network.
- B. Set FortiGate to operate in transparent mode.
- C. Set a software switch on FortiGate to handle inter-VLAN traffic.
- D. Set a FortiGate interface with the switch to operate as an 802.1q trunk.
Question #47
What two advantages does FortiNAC provide in the OT network? (Choose two answers)
- A. It can be used for IoT device detection.
- B. It can be used for industrial intrusion detection and prevention.
- C. It can be used for network micro-segmentation.
- D. It can be used for device profiling.
Question #48
Which two statements are true when you deploy FortiGate as an offline IDS? (Choose two answers)
- A. FortiGate acts as network sensor
- B. Network attacks can be detected and blocked
- C. FortiGate receives traffic from configured port mirroring
- D. Network traffic goes through FortiGate
Question #49
In a wireless network integration, how does FortiNAC obtain connecting MAC address information? (Choose one answer)
- A. MAC notification traps
- B. Link traps
- C. RADIUS
- D. End station traffic monitoring
Question #50
What are two critical tasks the OT network auditors must perform during OT network risk assessment and management? (Choose two answers)
- A. Implementing strategies to automatically bring PLCs offline
- B. Planning a threat hunting strategy
- C. Evaluating what can go wrong before it happens
- D. Creating disaster recovery plans to switch operations to a backup plant
What can be assigned using network access control policies? (Choose one answer)