● NSE 6 - OT Security 7.2 Architect Exam Materials
Please note that the exam "NSE 6 - OT Security 7.2 Architect" is no longer offered by Fortinet and is not available for booking through Pearson VUE, so we opened it on free view,
It has been replaced by the exam "NSE 6 - OT Security 7.6 Architect"
The new exam version is available on Brave-Dumps and can be purchased.
It has been replaced by the exam "NSE 6 - OT Security 7.6 Architect"
The new exam version is available on Brave-Dumps and can be purchased.
Question #51
Question #52
Which three methods of communication are used by FortiNAC to gather visibility information? (Choose three answers)
- A. SNMP
- B. ICMP
- C. API
- D. RADIUS
- E. TACACS
Question #53
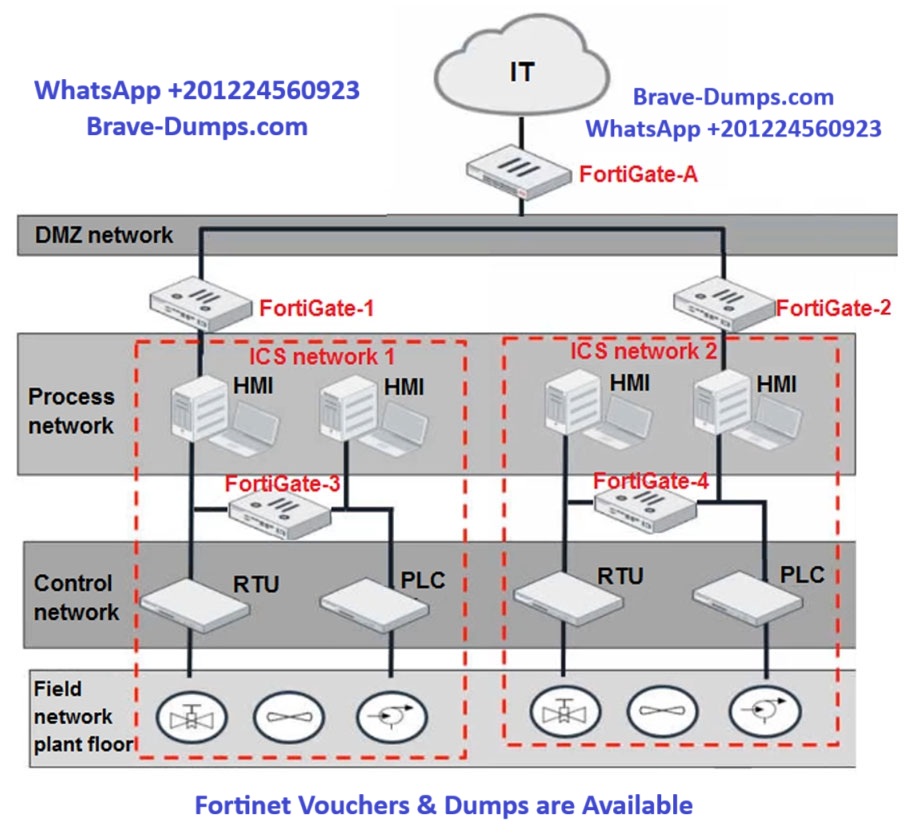
Refer to the exhibit.
Based on the topology designed by the OT architect, which two statements about implementing OT security are true?
(Choose two answers)
- A. Firewall policies should be configured on FortiGate-3 and FortiGate-4 with industrial protocol sensors.
- B. Micro-segmentation can be achieved only by replacing FortiGate-3 and FortiGate-4 with a pair of FortiSwitch devices.
- C. IT and OT networks are separated by segmentation.
- D. FortiGate-3 and FortiGate-4 devices must be in a transparent mode.
Question #54
As an OT administrator, it is important to understand how industrial protocols work in an OT network.
Which communication method is used by the Modbus protocol?
(Choose one answer)
- A. It uses OSI Layer 2 and the primary device sends data based on request from secondary device.
- B. It uses OSI Layer 2 and both the primary/secondary devices always send data during the communication.
- C. It uses OSI Layer 2 and both the primary/secondary devices send data based on a matching token ring.
- D. It uses OSI Layer 2 and the secondary device sends data based on request from primary device.
Question #55
Which three criteria can a FortiGate device use to look for a matching firewall policy to process traffic? (Choose three answers)
- A. Services defined in the firewall policy.
- B. Source defined as internet services in the firewall policy
- C. Lowest to highest policy ID number
- D. Destination defined as internet services in the firewall policy
- E. Highest to lowest priority defined in the firewall policy
Question #56
An OT supervisor needs to protect their network by implementing security with an industrial signature database on the FortiGate device.
Which statement about the industrial signature database on FortiGate is true?
.
(Choose one answer)
- A. A supervisor must purchase an industrial signature database and import it to the FortiGate.
- B. An administrator must create their own database using custom signatures.
- C. By default, the industrial database is enabled.
- D. A supervisor can enable it through the FortiGate CLI.
Question #57
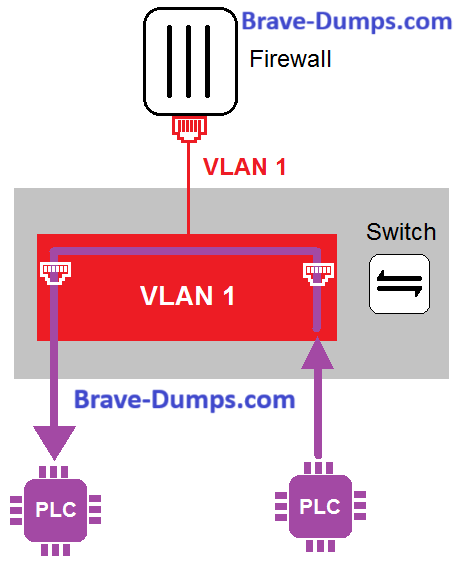
Refer to the exhibit.
In the topology shown in the exhibit, both PLCs can communicate directly with each other, without going through the firewall.
Which statement about the topology is true?
(Choose one answer)
- A. PLCs use IEEE802.1Q protocol to communicate each other.
- B. An administrator can create firewall policies in the switch to secure between PLCs.
- C. This integration solution expands VLAN capabilities from Layer 2 to Layer 3.
- D. There is no micro-segmentation in this topology.
Question #58
Which three common breach points can be found in a typical OT environment? (Choose three answers)
- A. VLAN exploits
- B. Black hat
- C. RTU exploits
- D. Hard hat
- E. Global hat
Question #59
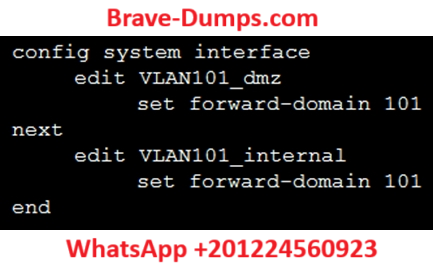
Refer to the exhibit.
Given the configurations on the FortiGate, which statement is true?
(Choose one answer)
- A. FortiGate is configured with forward-domains to reduce unnecessary traffic.
- B. FortiGate is configured with forward-domains to forward only domain controller traffic.
- C. FortiGate is configured with forward-domains to forward only company domain website traffic.
- D. FortiGate is configured with forward-domains to filter and drop non-domain controller traffic.
Question #60
An administrator wants to use FortiSoC and SOAR features on a FortiAnalyzer device to detect and block any unauthorized access to FortiGate devices in an OT network.
Which two statements about FortiSoC and SOAR features on FortiAnalyzer are true?
(Choose two answers)
- A. You must set correct operator in event handler to trigger an event.
- B. You can automate SOC tasks through playbooks.
- C. You cannot use Windows and Linux hosts security events with FortiSoC.
- D. Each playbook can include multiple triggers.
Which two frameworks are common to secure ICS industrial processes, including SCADA and DCS? (Choose two answers)