● FCP - FortiAuthenticator 6.5 Administrator Exam Materials
Please note that the exam "FCP - FortiAuthenticator 6.5 Administrator" is no longer offered by Fortinet and is not available for booking through Pearson VUE, so we opened it on free view,
Question #41
Question #42
Which method is the most secure way of delivering FortiToken data once the token has been seeded? (Choose one answer)
- A. Online activation of the tokens through the FortiGuard network
- B. Shipment of the seed files on a CD using a tamper-evident envelope
- C. Using the in-house token provisioning tool
- D. Automatic token generation using FortiAuthenticator
Question #43
At a minimum, which two configurations are required to enable guest portal services on FortiAuthenticator? (Choose two answers)
- A. Configuring a portal policy
- B. Configuring at least one post-login service
- C. Configuring a RADIUS client
- D. Configuring an external authentication portal
Question #44
A digital certificate, also known as an X.509 certificate, contains which two pieces of information? (Choose two answers)
- A. Shared secret
- B. Public key
- C. Issuer
- D. Private key
Question #45
Which two statements about asymmetric cryptography are true? (Choose two answers)
- A. The public key can be openly distributed.
- B. It distributes key pairs to both the client and the server.
- C. Private keys are distributed in the server's digital certificates.
- D. It uses a mathematically linked public and private key pair.
Question #46
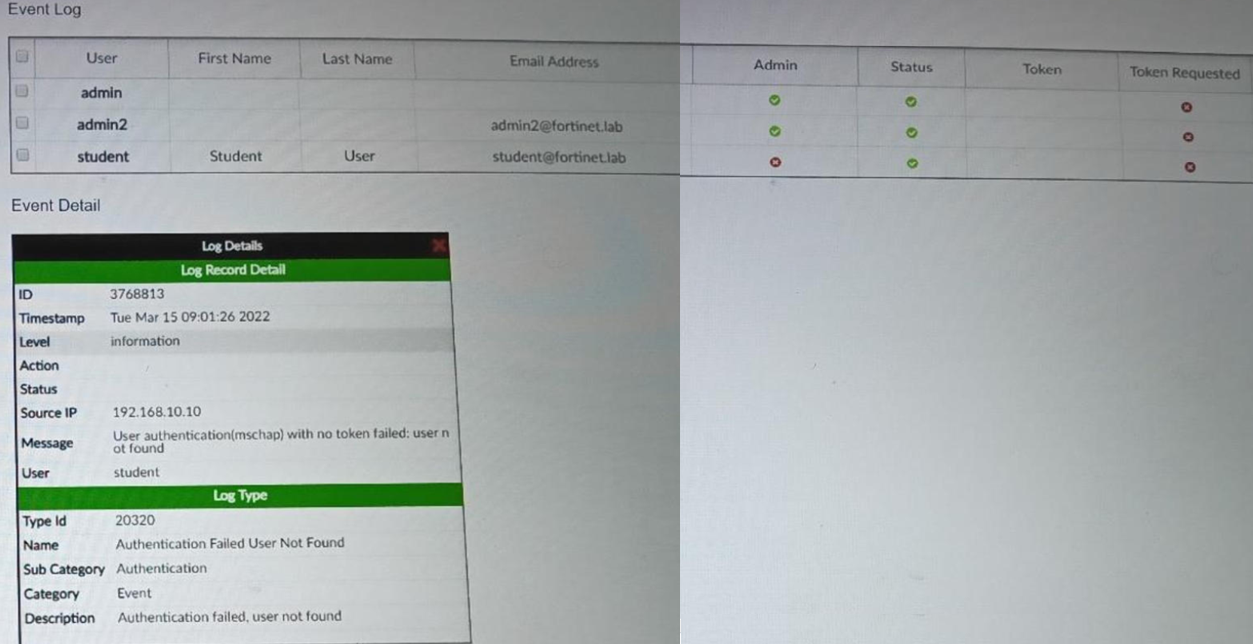
Refer to the exhibits.
An administrator has configured several wireless APs to use FortiAuthenticator as their RADIUS server. One user is unable to successfully authenticate. The user record exists in the system, but the FortiAuthenticator log shows Authentication failed, user not found.
What is the most likely cause of the problem?
(Choose one answer)
- A. The RADIUS traffic is being sourced from an IP address not listed as NAS.
- B. No client entry exists for the authenticating AP.
- C. RADIUS authentication is not enabled for the user.
- D. The RADIUS secret is incorrect.
Question #47
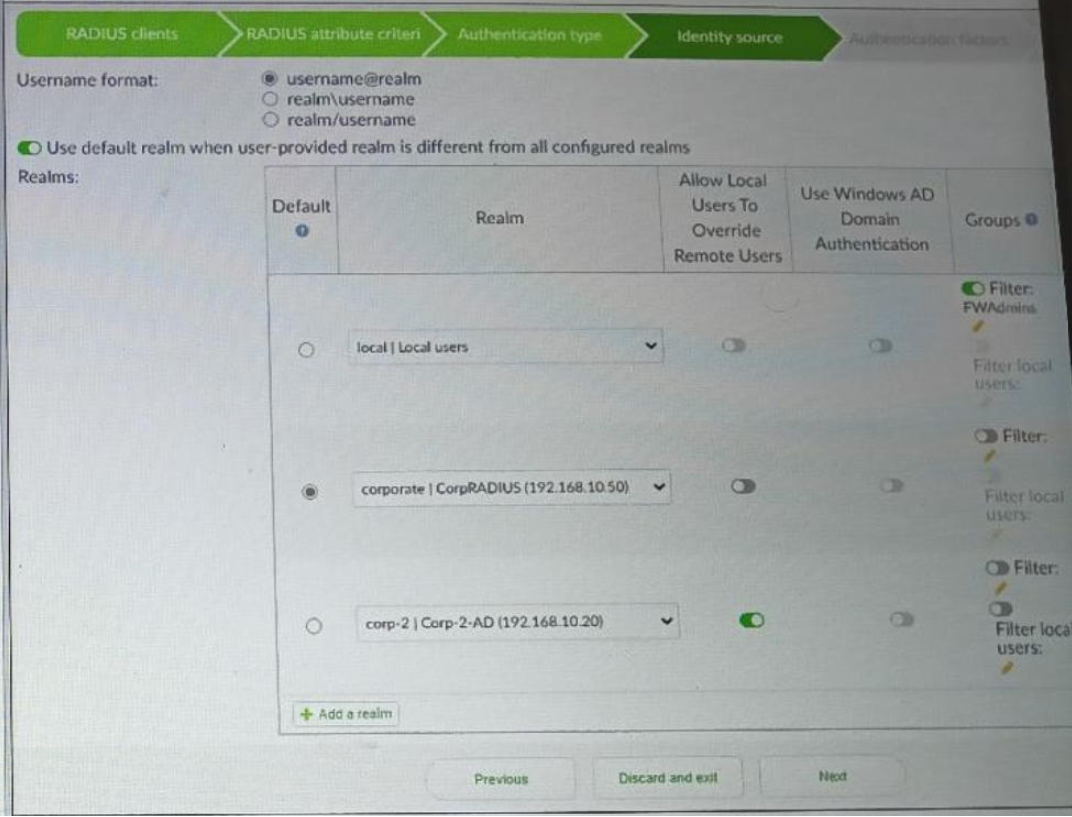
Refer to the exhibit.
Examine the RADIUS policy configuration shown in the exhibit. A user attempts to authenticate by entering the username [email protected] and their password.
Which realm will the user be authenticated against?
(Choose one answer)
- A. Corporate
- B. Local, but only if the account is a member of the FWAdmins group
- C. Local
- D. Corp-2, but only if the user has a local account
Question #48
When performing a remote LDAP server integration with FortiAuthenticator, how do server type templates assist with the integration? (Choose one answer)
- A. They automatically set the LDAP user auto provisioning settings.
- B. They autopopulate the simple and regular bind settings.
- C. They define the connection security and domain authentication settings for each LDAP server you integrate with.
- D. They populate the query element fields with defined attribute and class values.
Question #49
When configuring an active-passive HA deployment, what is the recommended data synchronization path? (Choose one answer)
- A. Dedicated fiber channel
- B. Direct cable connection
- C. Same VLAN
- D. Dedicated point-to-point VPN connection
Question #50
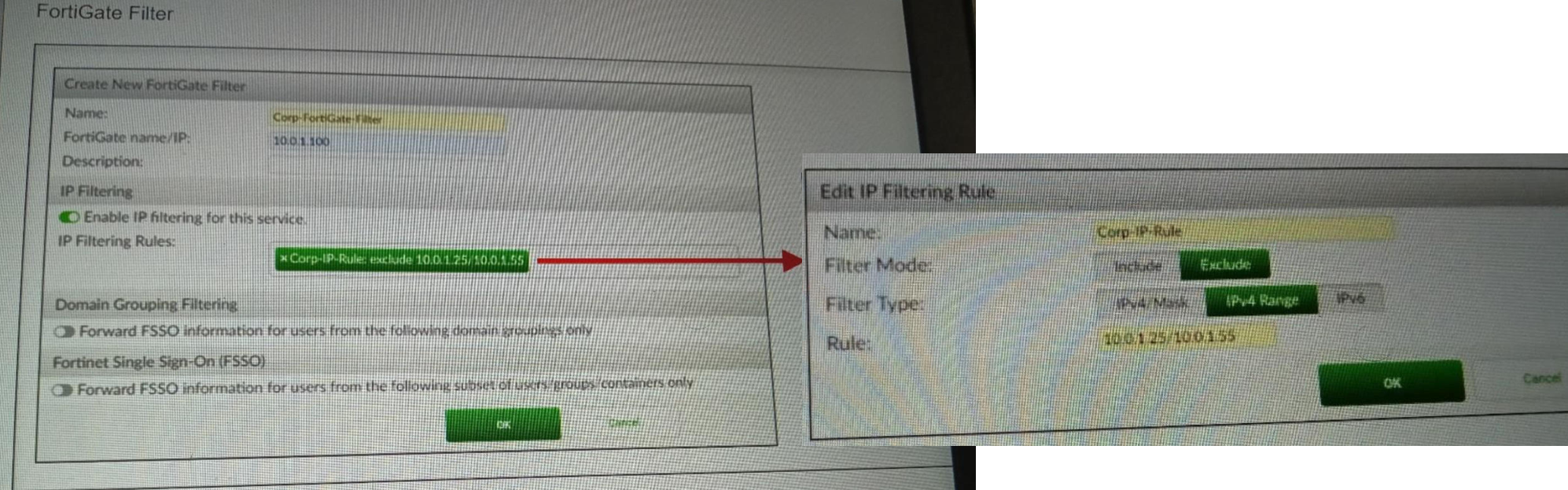
Refer to the exhibit.
What will be the result of this FortiGate filtering configuration?
(Choose one answer)
- A. FortiAuthenticator will send FSSO information from suppliers in the defined IP address range only.
- B. FortiAuthenticator will not send FSSO information to the FortiGate device for end points with IP addresses in the defined range.
- C. FortiGate will receive FSSO information from tiered FortiAuthenticator collectors in the defined IP address range only.
- D. FortiAuthenticator will not receive FSSO information from FortiGate devices in the defined IP address range.
What are three key features of FortiAuthenticator? (Choose three answers)