● FCP - FortiAuthenticator 6.5 Administrator Exam Materials
Please note that the exam "FCP - FortiAuthenticator 6.5 Administrator" is no longer offered by Fortinet and is not available for booking through Pearson VUE, so we opened it on free view,
Question #51
Question #52
Which two data items are not synchronized in an active-active HA deployment? (Choose two answers)
- A. User certificates
- B. Seeds
- C. FSSO events
- D. Group mappings
Question #53
An administrator has just learned that an intermediate CA certificate signed by the FortiAuthenticator, acting as the Root CA, has been compromised.
Which two steps should the administrator take to resolve the security issue?
(Choose two answers)
- A. Revoke the intermediate certificate so it is added to the CRL of the Root CA.
- B. Create a new intermediate certificate to override the compromised certificate.
- C. Update the OCSP responder URLs for the certificate.
- D. Revoke all end system/user certificates that this compromised intermediate CA has signed.
Question #54
Which two default admin profiles are included in a new FortiAuthenticator deployment? (Choose two answers)
- A. Contractor
- B. Sponsor
- C. Full Access
- D. Read-only Administrator
Question #55
An employee lost their assigned token and needs to authenticate to a resource which requires two factor authentication. The user does not have access to SMS or email.
How can an administrator provide access for the user?
(Choose one answer)
- A. Disable two-factor authentication on the resource
- B. Enable and provide an emergency code to the user
- C. Refresh the FTM provisioning status for the user
- D. Generate and provide an HOTP to the user
Question #56
A network administrator is using FortiAuthenticator as their RADIUS server for wired and wireless network access. The administrator wants to pass user's group information back to the RADIUS clients when users authenticate.
How would FortiAuthenticator accomplish this?
(Choose one answer)
- A. Syslog messages
- B. SNMP Traps
- C. RADIUS attributes
- D. SMS
Question #57
When implementing FIDO2, at a minimum, what information is stored on the service provider? (Choose one answer)
- A. Password and FIDO2 authenticator public key
- B. FIDO2 authenticator public key
- C. Username and FIDO2 authenticator private key
- D. Username and FIDO2 authenticator public key
Question #58
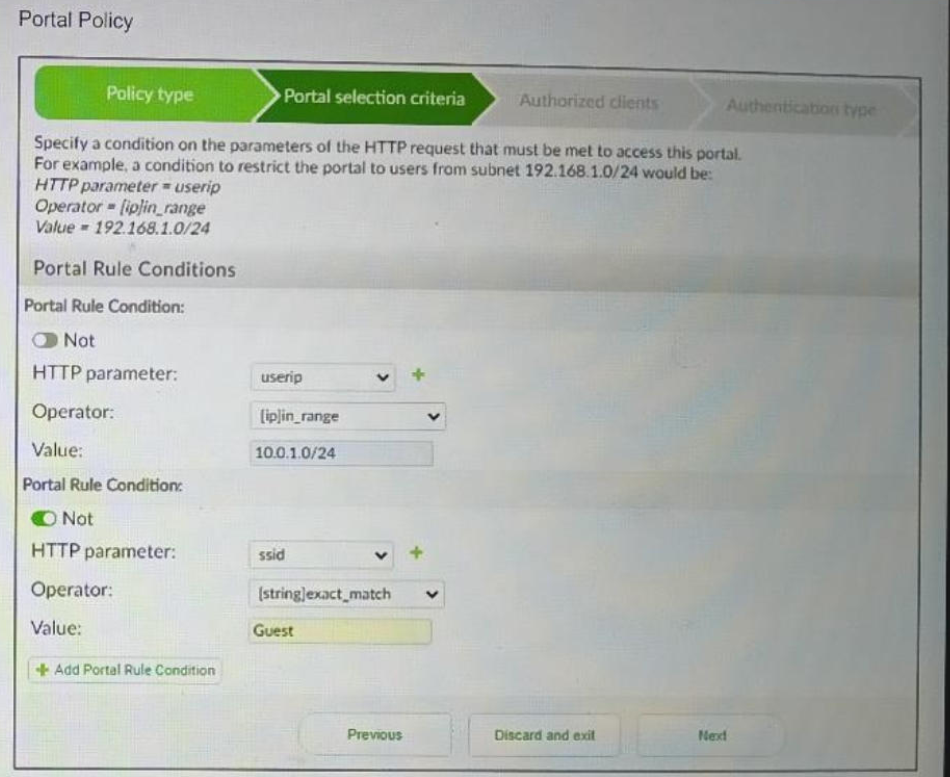
Refer to the exhibit.
An administrator has a captive portal configuration on their FortiGate that directs users to a portal page on FortiAuthenticator. A user whose laptop has an IP address of 10.0.1.85 and is connected through the Guest SSID, is failing to load the portal page.
What is the most likely cause of the problem?
(Choose one answer)
- A. The host IP address is not in the required range.
- B. The IP address is incorrect for the SSID.
- C. The host is connected to a prohibited SSID.
- D. The portal page will only be presented to wired hosts.
Question #59
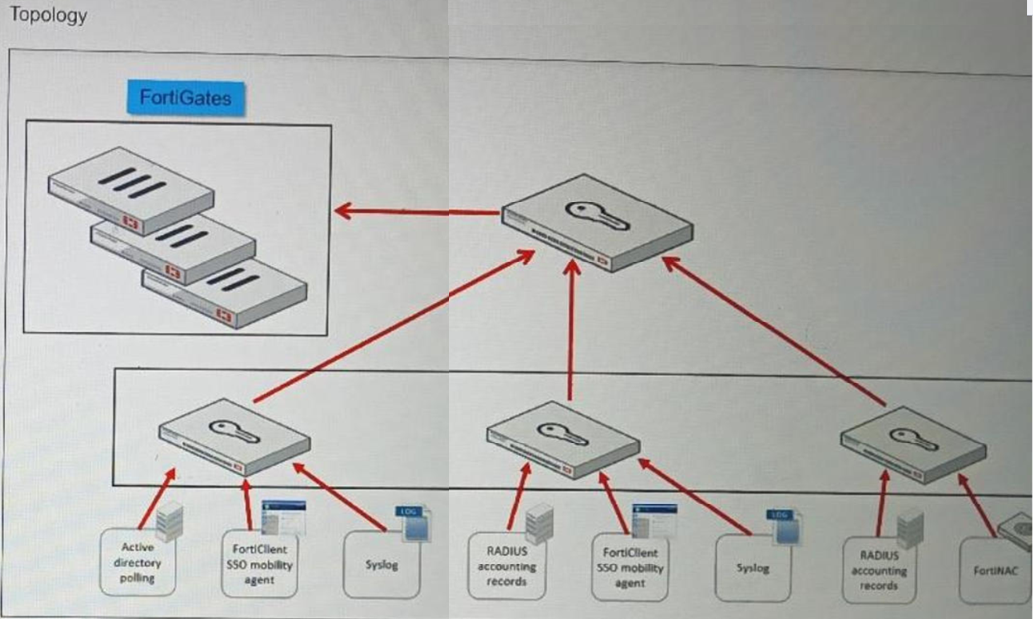
Refer to the exhibit.
What type of FortiAuthenticator configuration is shown in this topology?
(Choose one answer)
- A. Authentication load balancing nodes
- B. Active-active HA
- C. Tiered architecture
- D. RADIUS proxy
Question #60
An administrator wants users and devices that cannot be identified transparently, such as Android BYOD devices, to be able to register and create their own credentials.
In this case, which FortiAuthenticator user identity discovery method can the administrator use?
(Choose one answer)
- A. Portal authentication
- B. Syslog messaging or SAML IdP
- C. SSOMA
- D. Kerberos-based authentication
Which FortiAuthenticator feature allows users to authenticate against different backend databases, when using a single RADIUS policy? (Choose one answer)