● FCP - FortiGate 7.4 Administrator Exam Materials
Please note that the exam "FCP - FortiGate 7.4 Administrator Exam " is no longer offered by Fortinet and is not available for booking through Pearson VUE, so we opened it on free view,
It has been replaced by the exam "NSE 4 - FortiOS 7.6 Exam"
The new exam version is available on Brave-Dumps and can be purchased.
It has been replaced by the exam "NSE 4 - FortiOS 7.6 Exam"
The new exam version is available on Brave-Dumps and can be purchased.
Question #31
Question #32
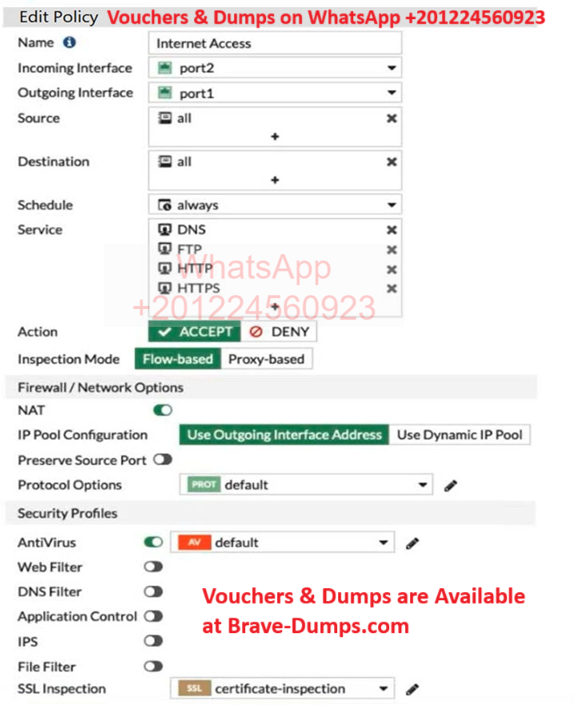
Refer to the exhibit to view the firewall policy.
Why would the firewall policy not block a well-known virus, for example eicar?
(Choose one answer)
- A. The action on the firewall policy is not set to deny
- B. The firewall policy is not configured in proxy-based inspection mode
- C. Web filter is not enabled on the firewall policy to complement the antivirus profile
- D. The firewall policy does not apply deep content inspection
Question #33

Refer to the exhibit.
FortiGate is configured for firewall authentication. When attempting to access an external website, the user is not presented with a login prompt.
What is the most likely reason for this situation?
(Choose one answer)
- A. The Service DNS is required in the firewall policy
- B. The user is using an incorrect user name
- C. The Remote-users group is not added to the Destination
- D. No matching user account exists for this user
Question #34
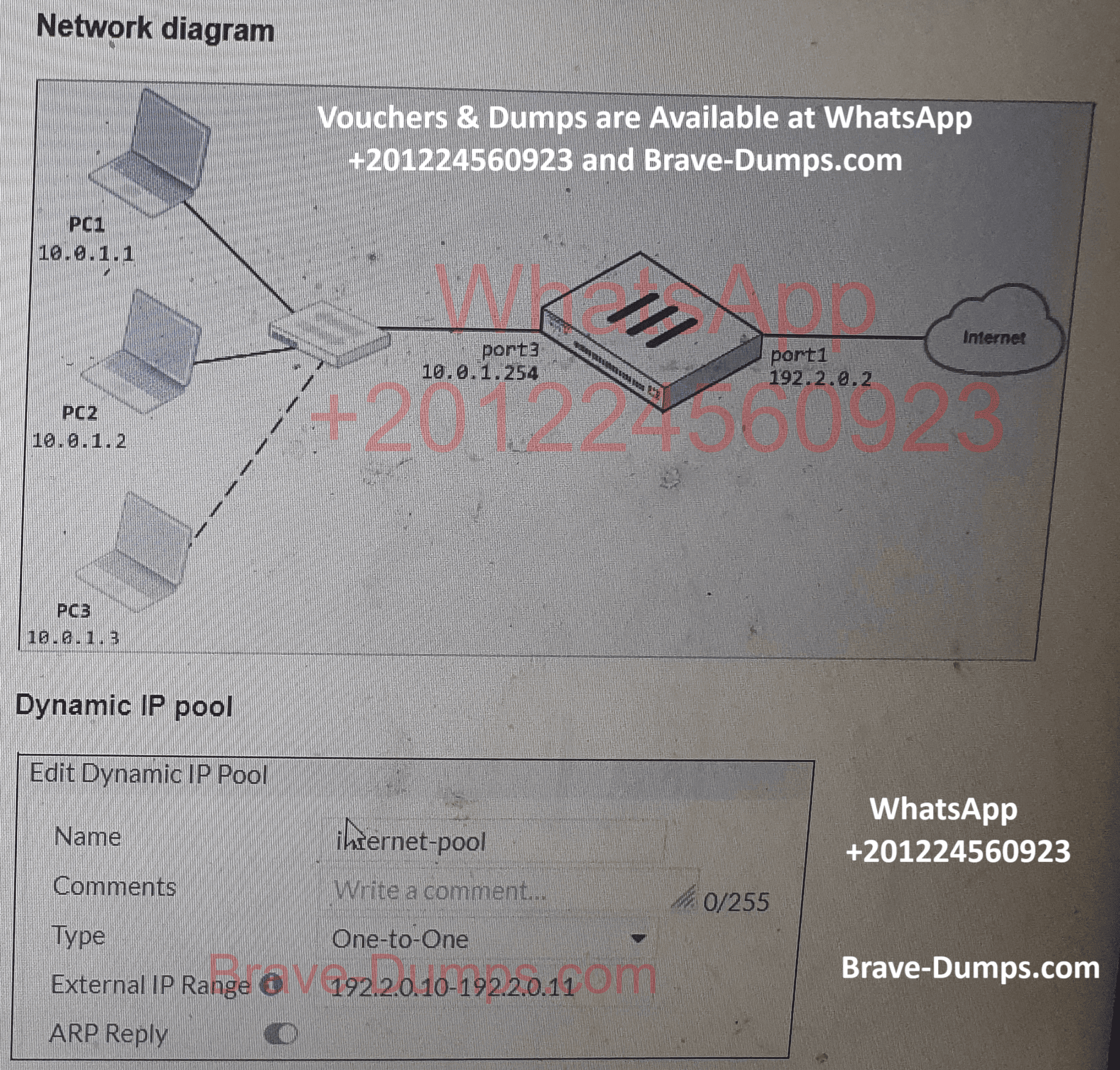
Refer to the exhibits.
The exhibits show a diagram of a FortiGate device connected to the network, as well as the firewall policy and IP pool configuration on the FortiGate device.
Two PCs, PC1 and PC2, are connected behind FortiGate and can access the internet successfully. However, when the administrator adds a third PC to the network (PC3), the PC cannot connect to the internet.
Based on the information shown in the exhibit, which two configuration options can the administrator use to fix the connectivity issue for PC3?
(Choose two answers)
- A. In the firewall policy configuration, add 10.0.1.3 as an address object in the source field.
- B. In the IP pool configuration, set endip to 192.2.0.12.
- C. In the IP pool configuration, set type to overload.
- D. Configure another firewall policy that matches only the address of PC3 as source, and then place the policy on top of the list.
Question #35
An administrator configured a FortiGate to act as a collector for agentless polling mode.
What must the administrator add to the FortiGate device to retrieve AD user group information?
(Choose one answer)
- A. RADIUS server
- B. LDAP server
- C. Windows server
- D. DHCP server
Question #36
Which method allows management access to the FortiGate CLI without network connectivity? (Choose one answer)
- A. CLI console widget
- B. Serial console
- C. SSH console
- D. Telnet console
Question #37
A network administrator is configuring an IPsec VPN tunnel for a sales employee travelling abroad.
Which IPsec Wizard template must the administrator apply?
(Choose one answer)
- A. Site to Site
- B. Hub-and-Spoke
- C. Dial up User
- D. Remote Access
Question #38
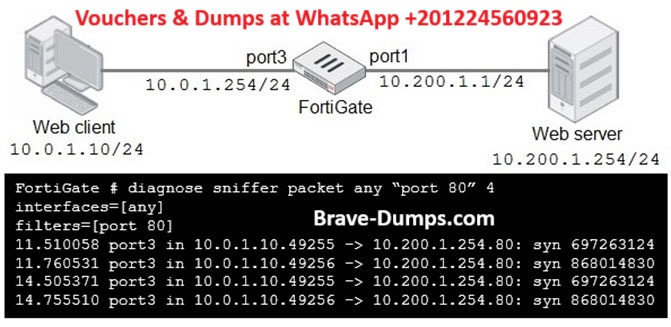
Refer to the exhibit:
In the network shown in the exhibit, the web client cannot connect to the HTTP web server. The administrator runs the FortiGate built-in sniffer and gets the output as shown in the exhibit.
What should the administrator do next to troubleshoot the problem?
(Choose one answer)
- A. Run a sniffer on the web server.
- B. Capture the traffic using an external sniffer connected to port1.
- C. Execute another sniffer in the FortiGate, this time with the filter "host 10.0.1.10"
- D. Execute a debug flow.
Question #39
Which three pieces of information does FortiGate use to identify the hostname of the SSL server when SSL certificate inspection is enabled? (Choose three answers)
- A. The subject field in the server certificate
- B. The subject alternative name (SAN) field in the server certificate
- C. The serial number in the server certificate
- D. The server name indication (SNI) extension in the client hello message
- E. The host field in the HTTP header
Question #40
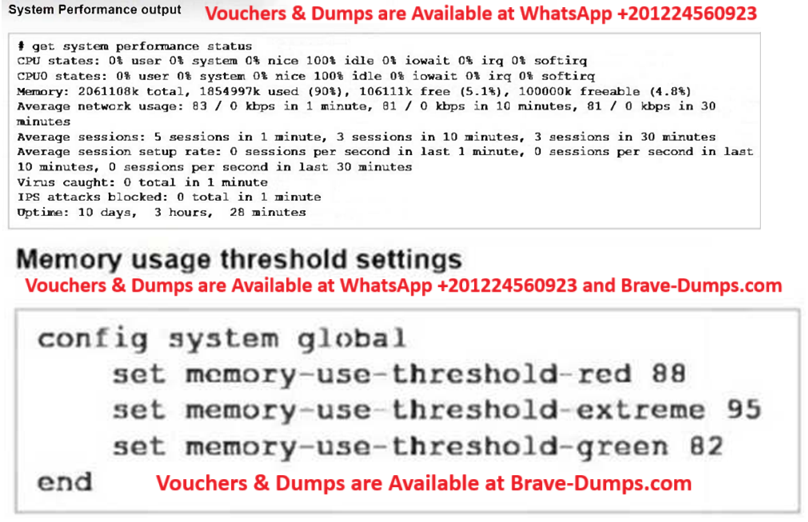
Based on the system performance output, what can be the two possible outcomes? (Choose two answers)
- A. FortiGate will start sending all files to FortiSandbox for inspection.
- B. FortiGate has entered conserve mode.
- C. Administrators cannot change the configuration.
- D. Administrators can access FortiGate only through the console port.
When FortiGate performs SSL/SSH full inspection, you can decide how it should react when it detects an invalid certificate.
Which three actions are valid actions that FortiGate can perform when it detects an invalid certificate? (Choose three answers)