● FCP - FortiGate 7.4 Administrator Exam Materials
Please note that the exam "FCP - FortiGate 7.4 Administrator Exam " is no longer offered by Fortinet and is not available for booking through Pearson VUE, so we opened it on free view,
It has been replaced by the exam "NSE 4 - FortiOS 7.6 Exam"
The new exam version is available on Brave-Dumps and can be purchased.
It has been replaced by the exam "NSE 4 - FortiOS 7.6 Exam"
The new exam version is available on Brave-Dumps and can be purchased.
Question #41
Question #42
A network administrator wants to set up redundant IPsec VPN tunnels on FortiGate by using two IPsec VPN tunnels and static routes.
- All traffic must be routed through the primary tunnel when both tunnels are up.
- The secondary tunnel must be used only if the primary tunnel goes down. In addition, FortiGate should be able to detect a dead tunnel to speed up tunnel failover.
Which two key configuration changes must the administrator make on FortiGate to meet the requirements?
(Choose two answers)
- A. Configure a higher distance on the static route for the primary tunnel, and a lower distance on the static route for the secondary tunnel.
- B. Enable Dead Peer Detection.
- C. Enable Auto-negotiate and Auto Keep Alive on the phase 2 configuration of both tunnels.
- D. Configure a lower distance on the static route for the primary tunnel, and a higher distance on the static route for the secondary tunnel.
Question #43
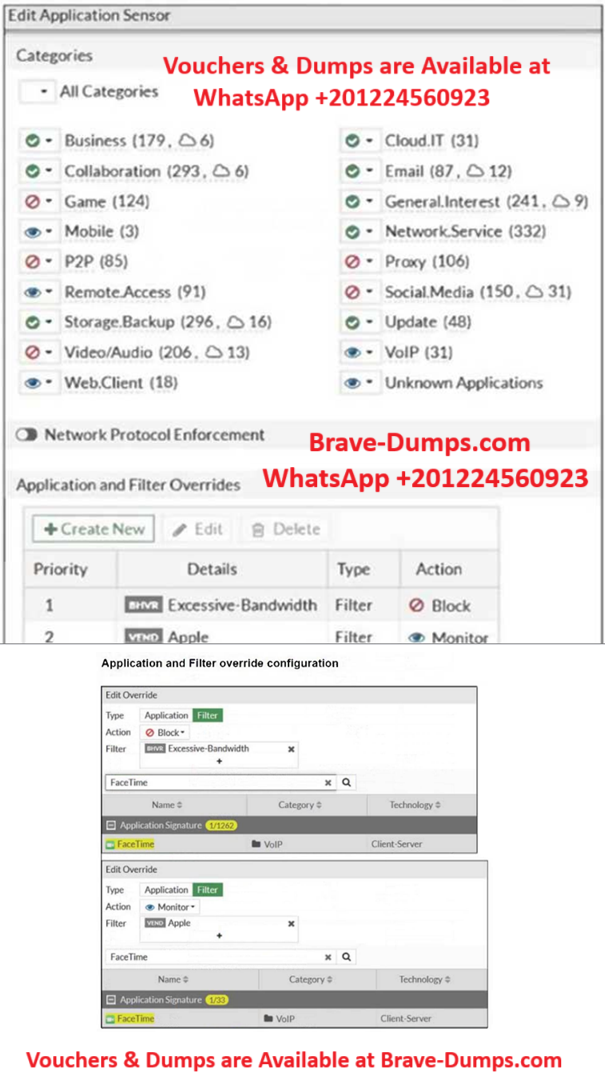
Refer to the exhibits.
Exhibit A shows the application sensor configuration. Exhibit B shows the Excessive-Bandwidth and Apple filter details.
Based on the configuration, what will happen to Apple FaceTime if there are only a few calls originating or incoming?
(Choose one answer)
- A. Apple FaceTime will be allowed, based on the Categories configuration.
- B. Apple FaceTime will be allowed, based on the Apple filter configuration.
- C. Apple FaceTime will be allowed only if the Apple filter in Application and Filter Overrides is set to Allow.
- D. Apple FaceTime will be blocked, based on the Excessive-Bandwidth filter configuration
Question #44
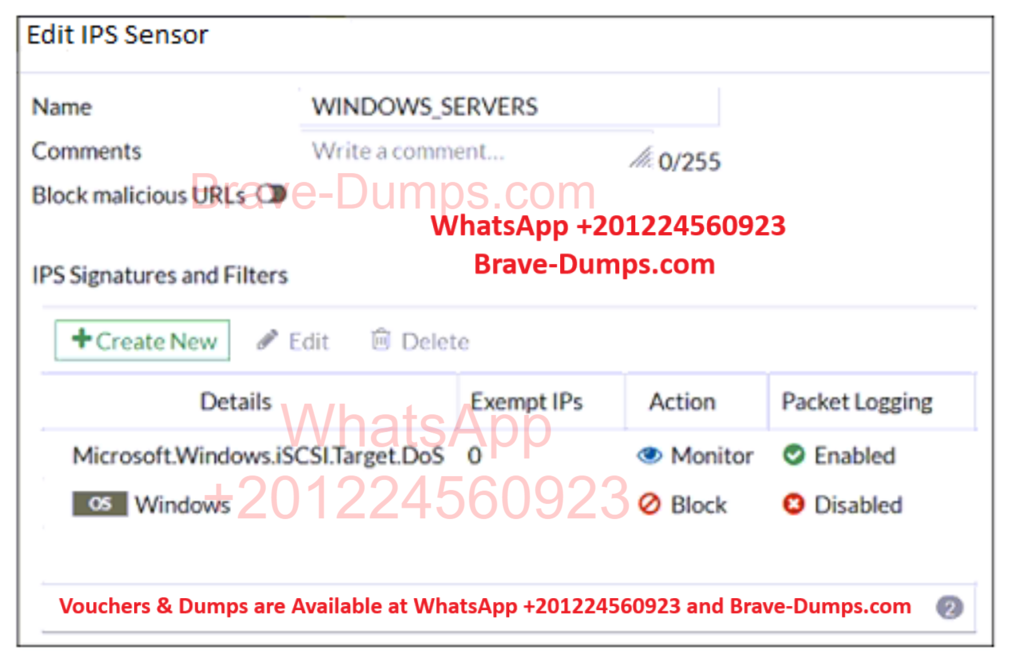
Refer to the exhibit, which shows the IPS sensor configuration.
If traffic matches this IPS sensor, which two actions is the sensor expected to take?
(Choose two answers)
- A. The sensor will gather a packet log for all matched traffic.
- B. The sensor will reset all connections that match these signatures.
- C. The sensor will allow attackers matching the Microsoft.Windows.iSCSI.Target.DoS signature.
- D. The sensor will block all attacks aimed at Windows servers.
Question #45
Which statement is a characteristic of automation stitches? (Choose one answer)
- A. They can be run only on devices in the Security Fabric
- B. They can be created only on downstream devices in the fabric.
- C. They can have one or more triggers
- D. They can run multiple actions at the same time.
Question #46
What is the primary FortiGate election process when the HA override setting is disabled? (Choose one answer)
- A. Connected monitored ports > Priority > System uptime > FortiGate serial number
- B. Connected monitored ports > System uptime > Priority > FortiGate serial number
- C. Connected monitored ports > Priority > HA uptime > FortiGate serial number
- D. Connected monitored ports > HA uptime > Priority > FortiGate serial number
Question #47
Which two settings are required for SSL VPN to function between two FortiGate devices? (Choose two answers)
- A. The client FortiGate requires the SSL VPN tunnel interface type to connect SSL VPN
- B. The server FortiGate requires a CA certificate to verify the client FortiGate certificate.
- C. The client FortiGate requires a client certificate signed by the CA on the server FortiGate.
- D. The client FortiGate requires a manually added route to remote subnets
Question #48
Which two statements describe how the RPF check is used? (Choose two answers)
- A. The RPF check is run on the first sent packet of any new session
- B. The RPF check is run on the first reply packet of any new session.
- C. The RPF check is run on the first sent and reply packet of any new session.
- D. The RPF check is a mechanism that protects FortiGate and the network from IP spoofing attacks.
Question #49
Which two features of IPsec IKEv1 authentication are supported by FortiGate? (Choose two answers)
- A. Pre-shared key and certificate signature as authentication methods
- B. Extended authentication (XAuth)to request the remote peer to provide a username and password
- C. Extended authentication (XAuth) for faster authentication because fewer packets are exchanged
- D. No certificate is required on the remote peer when you set the certificate signature as the authentication method
Question #50
What are two features of the NGFW profile-based mode? (Choose two answers)
- A. NGFW profile-based mode can only be applied globally and not on individual VDOMs
- B. NGFW profile-based mode must require the use of central source NAT policy
- C. NGFW profile-based mode policies support both flow inspection and proxy inspection.
- D. NGFW profile-based mode supports applying applications and web filtering profiles in a firewall
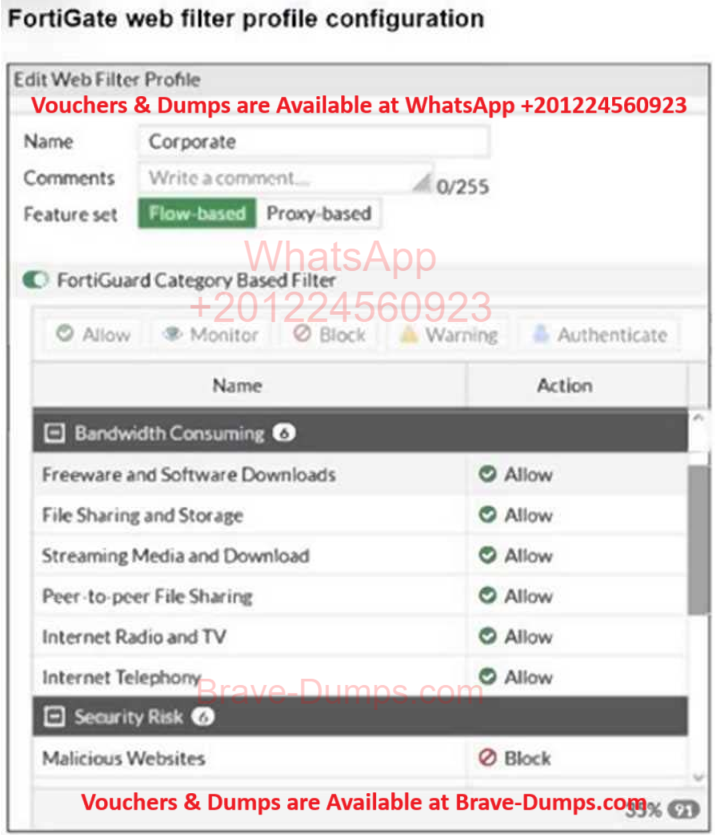
The exhibit shows the FortiGuard Category Based Filter section of a corporate web filter profile.
An administrator must block access to download.com, which belongs to the Freeware and Software Downloads category. The administrator must also allow other websites in the same category.
What are two solutions for satisfying the requirement? (Choose two answers)